Understanding ISIS Anu Login: A Comprehensive Guide
In the digital age, online security and privacy have become critical topics. One term that often surfaces in discussions about cybersecurity is "ISIS Anu Login." This article aims to provide a detailed exploration of what this term entails, its significance, and related aspects that you need to know.
ISIS Anu Login has become a subject of interest not only for tech enthusiasts but also for individuals concerned about online safety. As the world becomes increasingly interconnected, understanding such terms can empower users to navigate the internet securely.
Through this article, we will delve into various aspects of ISIS Anu Login, including its origins, implications, and steps you can take to protect your digital presence. Let's begin by breaking down the concept and exploring its relevance in today's digital landscape.
What is ISIS Anu Login?
ISIS Anu Login refers to a specific login system or process associated with online platforms or databases. While the term itself may sound complex, it essentially relates to authentication methods used to verify user identities. This section will explain the basics of the term and its importance in cybersecurity.
Understanding the terminology behind "ISIS Anu Login" is crucial for anyone seeking to enhance their digital literacy. It involves examining the structure of login systems, their functions, and how they contribute to safeguarding sensitive information.
Key Components of Login Systems
- Username: A unique identifier assigned to each user.
- Password: A secret code used to authenticate the user's identity.
- Two-Factor Authentication (2FA): An additional layer of security beyond the standard username and password.
- Encryption: The process of encoding data to prevent unauthorized access.
History and Background of ISIS Anu Login
To fully grasp the concept of ISIS Anu Login, it's essential to explore its historical context. The development of authentication systems has evolved significantly over the years, adapting to the growing threats in cyberspace. This section will outline the timeline of login mechanisms and highlight key milestones in their evolution.
Evolution of Authentication Systems
- Early Systems: Basic username and password combinations.
- Modern Systems: Incorporation of biometric data and multi-factor authentication.
- Future Trends: Advancements in AI-driven authentication methods.
Why is ISIS Anu Login Important?
In today's interconnected world, securing personal and corporate data is paramount. ISIS Anu Login plays a vital role in ensuring that only authorized individuals can access sensitive information. By implementing robust authentication protocols, organizations can mitigate the risks of data breaches and cyberattacks.
Risks of Weak Authentication
- Data breaches leading to identity theft.
- Unauthorized access to confidential information.
- Financial losses and reputational damage.
How Does ISIS Anu Login Work?
The functionality of ISIS Anu Login revolves around several core processes. These include user verification, data encryption, and system monitoring. By understanding how these processes work, users can better appreciate the importance of secure login systems.
Steps in the Authentication Process
- User enters login credentials.
- System verifies the credentials against stored data.
- Encryption ensures secure transmission of information.
- Access is granted or denied based on verification results.
Best Practices for Secure Login Systems
Implementing secure login systems requires adherence to best practices. This section will provide actionable tips for individuals and organizations looking to enhance their cybersecurity measures.
Tips for Users
- Create strong, unique passwords for each account.
- Enable two-factor authentication whenever possible.
- Avoid using public Wi-Fi for sensitive transactions.
Tips for Organizations
- Regularly update security protocols to address emerging threats.
- Conduct employee training on cybersecurity awareness.
- Invest in advanced encryption technologies.
Common Misconceptions About ISIS Anu Login
There are several misconceptions surrounding the term "ISIS Anu Login." This section will address these myths and provide clarity on the actual processes involved in authentication systems.
Myth vs. Reality
- Myth: All login systems are equally secure.
- Reality: Security levels vary depending on the system's design and implementation.
- Myth: Passwords alone are sufficient for protection.
- Reality: Multi-factor authentication significantly enhances security.
Legal and Ethical Considerations
Authentication systems like ISIS Anu Login must comply with legal and ethical standards. This section will discuss the regulations governing data protection and the responsibilities of organizations in safeguarding user information.
Key Regulations
- General Data Protection Regulation (GDPR).
- California Consumer Privacy Act (CCPA).
- Other regional data protection laws.
Future of Authentication Systems
As technology continues to advance, the future of authentication systems looks promising. Innovations such as biometric authentication, behavioral analytics, and AI-driven solutions are set to redefine how we secure our digital identities.
Emerging Technologies
- Biometric Authentication: Fingerprint, facial recognition, and voice recognition.
- Behavioral Analytics: Monitoring user behavior patterns to detect anomalies.
- AI-Driven Security: Utilizing machine learning to enhance threat detection.
Conclusion
In conclusion, understanding ISIS Anu Login and its implications is essential for anyone navigating the digital landscape. By adopting best practices and staying informed about the latest developments in cybersecurity, users and organizations can better protect themselves from potential threats.
We encourage you to share this article with others who may benefit from the insights provided. Additionally, feel free to leave a comment below with any questions or feedback. For further reading, explore our other articles on cybersecurity and digital safety.
Table of Contents
- What is ISIS Anu Login?
- History and Background of ISIS Anu Login
- Why is ISIS Anu Login Important?
- How Does ISIS Anu Login Work?
- Best Practices for Secure Login Systems
- Common Misconceptions About ISIS Anu Login
- Legal and Ethical Considerations
- Future of Authentication Systems
- Conclusion
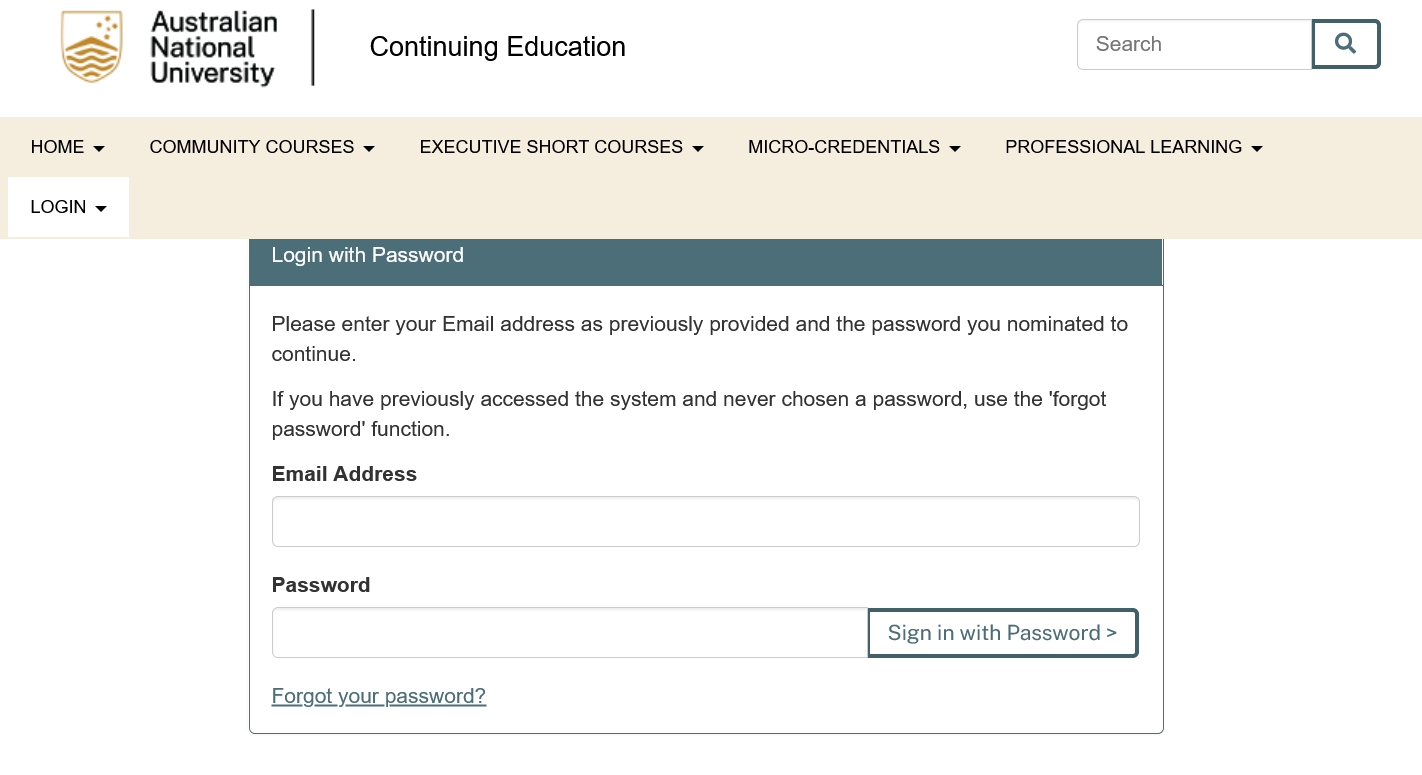
ANU ISIS Login Guide to Access Australian National University Student
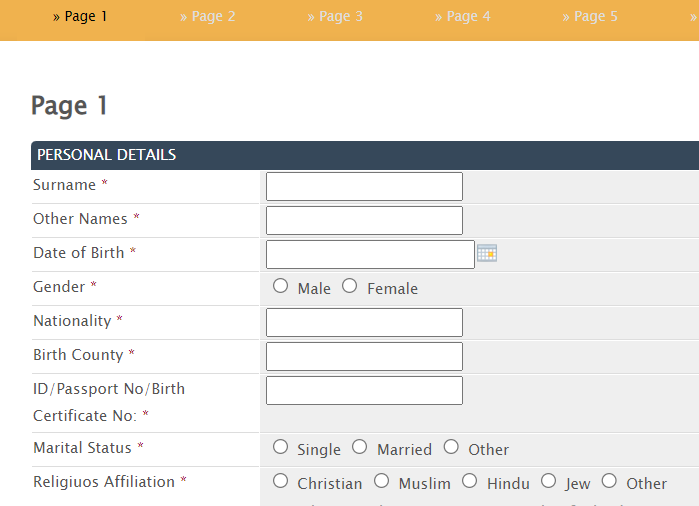
ANU Admission Portal Login Apply
Anu Tailam Namo Nakshartra Health Care Pvt. Ltd.