Mastering RemoteIoT VPC SSH: A Comprehensive Guide For Secure Access
In today's rapidly evolving digital landscape, remote access to cloud-based infrastructures is becoming increasingly vital for businesses and individuals alike. RemoteIoT VPC SSH has emerged as a powerful solution to facilitate secure and seamless connectivity to virtual private clouds. This guide will explore the intricacies of RemoteIoT VPC SSH and its significance in modern network architectures.
As more organizations adopt cloud computing, ensuring secure access to virtual environments becomes a top priority. RemoteIoT VPC SSH serves as a cornerstone for protecting sensitive data and maintaining network integrity. This technology leverages Secure Shell (SSH) protocols to create encrypted connections between devices and Virtual Private Clouds (VPCs), enhancing security and efficiency.
This article aims to provide a thorough understanding of RemoteIoT VPC SSH, covering its functionalities, benefits, challenges, and best practices. Whether you're a network administrator, IT professional, or someone interested in cloud security, this guide will equip you with the knowledge needed to implement and manage this critical technology effectively.
Below is a detailed table of contents to help you navigate through the article:
Table of Contents
- What is RemoteIoT VPC SSH?
- Importance of Secure Connections in Cloud Computing
- Key Components of VPC SSH
- Benefits of RemoteIoT VPC SSH
- Common Challenges in Implementing RemoteIoT VPC SSH
- Best Practices for Using RemoteIoT VPC SSH
- How to Set Up RemoteIoT VPC SSH
- Security Considerations for RemoteIoT VPC SSH
- Case Studies: Real-World Applications of RemoteIoT VPC SSH
- The Future of RemoteIoT VPC SSH
What is RemoteIoT VPC SSH?
RemoteIoT VPC SSH refers to the integration of Secure Shell (SSH) protocols with Virtual Private Clouds (VPCs) to enable secure remote access for Internet of Things (IoT) devices. This technology ensures that communication between IoT devices and cloud servers remains encrypted and protected from unauthorized access.
SSH acts as a secure tunnel for data transmission, while VPC provides an isolated network environment where sensitive operations can be performed without exposing them to the public internet. Together, they form a robust solution for managing IoT devices in cloud-based ecosystems.
How Does RemoteIoT VPC SSH Work?
The process begins with the establishment of an SSH session between the client device and the VPC endpoint. Once the connection is authenticated, all data exchanged between the two parties is encrypted, ensuring confidentiality and integrity. Below are the key steps involved:
- Authentication: The client device verifies its identity using SSH keys or passwords.
- Encryption: Data packets are encrypted using advanced cryptographic algorithms.
- Transmission: Encrypted data is transmitted through the SSH tunnel to the VPC.
- Decryption: Upon reaching the destination, the data is decrypted and processed securely.
Importance of Secure Connections in Cloud Computing
In the age of cloud computing, secure connections have become indispensable for safeguarding sensitive information. RemoteIoT VPC SSH plays a crucial role in this context by addressing several critical security concerns:
Why Security Matters?
With the increasing frequency of cyberattacks, organizations must prioritize securing their networks and data. RemoteIoT VPC SSH offers a multi-layered security approach, combining encryption, authentication, and access control mechanisms to protect against unauthorized access and data breaches.
Impact on Business Operations
Secure connections enhance operational efficiency by reducing downtime caused by security incidents. They also help organizations comply with regulatory requirements, such as GDPR and HIPAA, which mandate stringent data protection measures.
Key Components of VPC SSH
Understanding the components of VPC SSH is essential for effectively implementing RemoteIoT VPC SSH. Below are the primary elements:
1. Virtual Private Cloud (VPC)
A VPC is an isolated network environment within the cloud, providing a secure space for deploying applications and services. It ensures that all traffic within the network remains private and protected.
2. Secure Shell (SSH)
SSH is a network protocol that facilitates secure communication between devices over an unsecured network. It uses encryption to protect data in transit and authentication mechanisms to verify the identities of communicating parties.
3. IoT Devices
IoT devices are the end points in this architecture, responsible for collecting and transmitting data to the cloud. Ensuring their secure integration into the VPC is vital for maintaining overall network security.
Benefits of RemoteIoT VPC SSH
Implementing RemoteIoT VPC SSH offers numerous advantages that make it an attractive solution for modern cloud infrastructures:
Enhanced Security
By encrypting all data transmissions, RemoteIoT VPC SSH significantly reduces the risk of data breaches and unauthorized access.
Improved Performance
With secure and reliable connections, organizations can achieve better performance and uptime for their cloud-based applications.
Cost Efficiency
Using SSH for secure access eliminates the need for costly hardware-based solutions, making it a cost-effective option for businesses of all sizes.
Common Challenges in Implementing RemoteIoT VPC SSH
Despite its benefits, implementing RemoteIoT VPC SSH comes with its own set of challenges. Below are some of the most common obstacles:
Complex Configuration
Setting up and configuring SSH keys, firewalls, and network settings can be complex and time-consuming for inexperienced users.
Key Management
Managing SSH keys securely and ensuring their proper rotation is critical for maintaining long-term security.
Performance Overhead
Encrypting and decrypting data can introduce latency, potentially impacting the performance of real-time applications.
Best Practices for Using RemoteIoT VPC SSH
To maximize the effectiveness of RemoteIoT VPC SSH, it's important to follow best practices. Here are some recommendations:
Use Strong Authentication Methods
Employ SSH keys instead of passwords for authentication to enhance security.
Regularly Update Software
Ensure that all software components, including SSH clients and servers, are updated with the latest security patches.
Monitor Network Activity
Implement monitoring tools to detect and respond to suspicious activities in real time.
How to Set Up RemoteIoT VPC SSH
Setting up RemoteIoT VPC SSH involves several steps, including configuring the VPC, generating SSH keys, and establishing secure connections. Below is a step-by-step guide:
Step 1: Configure the VPC
Create a VPC in your cloud provider's console and define its subnets, gateways, and security groups.
Step 2: Generate SSH Keys
Use tools like OpenSSH to generate public and private key pairs for secure authentication.
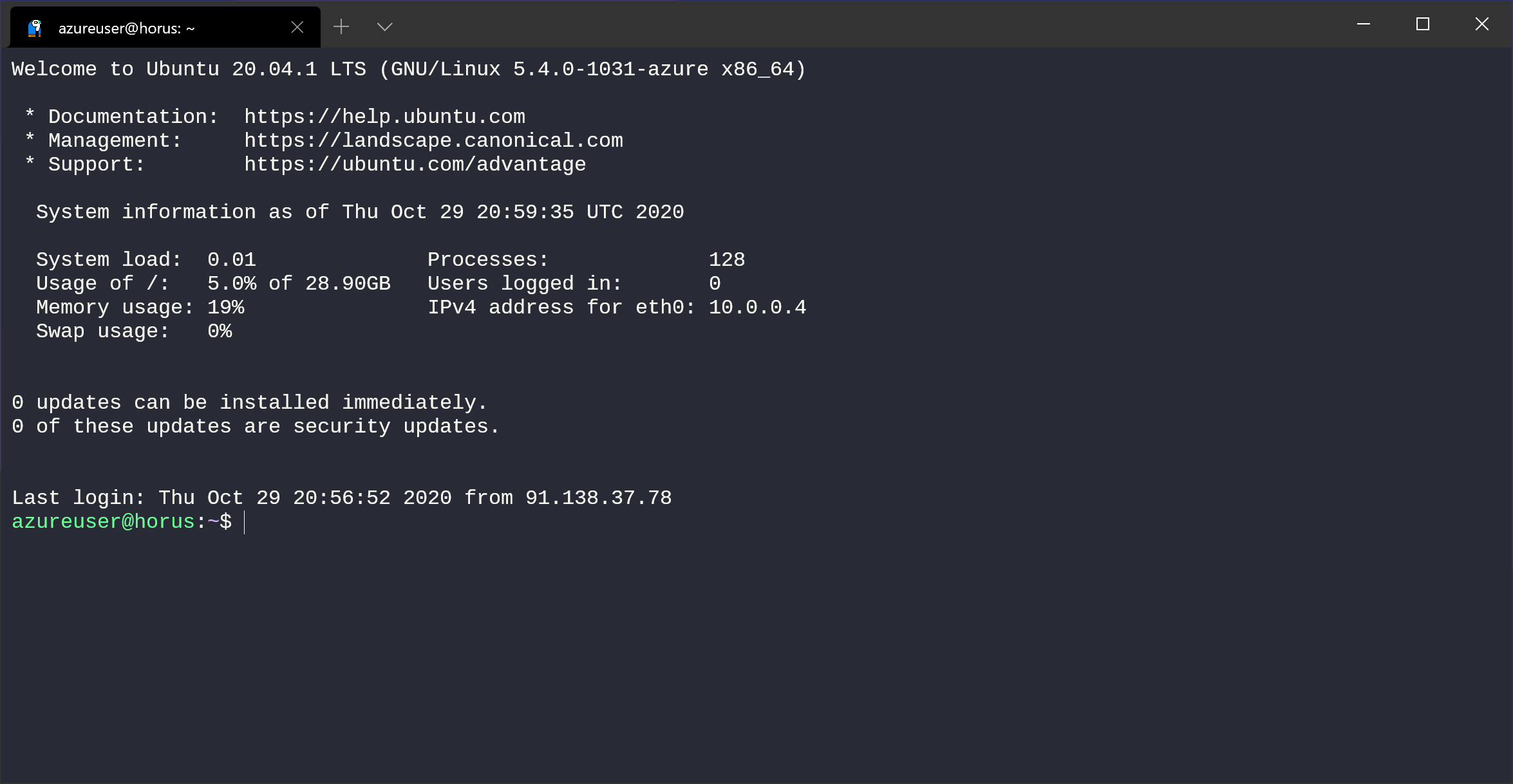
Step 3: Establish SSH Connection
Connect to the VPC endpoint using the generated SSH key and verify the connection.
Security Considerations for RemoteIoT VPC SSH
While RemoteIoT VPC SSH provides robust security, it's important to address potential vulnerabilities. Below are some key considerations:
Regular Audits
Conduct regular audits of your SSH configurations and VPC settings to identify and remediate security gaps.
Use Multi-Factor Authentication
Implement multi-factor authentication (MFA) to add an extra layer of security to your SSH connections.
Case Studies: Real-World Applications of RemoteIoT VPC SSH
Several organizations have successfully implemented RemoteIoT VPC SSH to enhance their cloud security. Below are two examples:
Case Study 1: Smart Agriculture
Agricultural company XYZ used RemoteIoT VPC SSH to securely monitor and control IoT sensors deployed in remote farms, ensuring real-time data collection without compromising security.
Case Study 2: Healthcare Monitoring
Hospital ABC implemented RemoteIoT VPC SSH to enable secure access to patient data stored in the cloud, complying with HIPAA regulations.
The Future of RemoteIoT VPC SSH
As technology continues to evolve, the future of RemoteIoT VPC SSH looks promising. Advances in encryption algorithms, quantum computing, and artificial intelligence are expected to further enhance its capabilities, making it an even more secure and efficient solution for cloud-based operations.
Conclusion
RemoteIoT VPC SSH represents a powerful tool for securing cloud-based IoT infrastructures. By understanding its components, benefits, and challenges, organizations can leverage this technology to protect their data and maintain operational efficiency. We encourage readers to implement the best practices outlined in this guide and explore the real-world applications discussed in the case studies.
Feel free to leave your thoughts and questions in the comments section below. Additionally, share this article with others who may find it useful, and don't hesitate to explore more content on our website for further insights into cloud security and IoT technologies.

RemoteIoT VPC SSH Raspberry Pi Download Free A Comprehensive Guide
Mastering RemoteIoT VPC SSH On Windows 10 Without Complications

Mastering RemoteIoT VPC SSH On Windows 10 Without Complications