Best Remote IoT Device SSH: Unlocking Secure And Efficient Connectivity
As technology continues to evolve, the need for secure and efficient remote access to IoT devices has become more critical than ever. The best remote IoT device SSH solutions offer a secure way to manage and interact with these devices from anywhere in the world. This article explores the top options available, their features, and how they can enhance your IoT infrastructure.
In today's interconnected world, IoT devices are transforming industries and daily life. However, ensuring secure access to these devices remotely is essential to protect sensitive data and maintain system integrity. SSH (Secure Shell) plays a pivotal role in this process by providing encrypted communication channels.
This comprehensive guide will delve into the best remote IoT device SSH solutions, offering actionable insights and expert recommendations. Whether you're a beginner or an experienced professional, this article will equip you with the knowledge to make informed decisions about securing your IoT infrastructure.
Table of Contents:
- Introduction to Remote IoT Device SSH
- Key Benefits of Using SSH for IoT Devices
- Top Remote IoT Device SSH Solutions
- Essential Security Features to Look For
- Comparison of Leading SSH Solutions
- How to Implement SSH for IoT Devices
- Common Challenges in Remote IoT SSH
- Future Trends in IoT SSH Technology
- Best Practices for Secure IoT SSH
- Conclusion and Next Steps
Introduction to Remote IoT Device SSH
What is SSH and Why It Matters for IoT
SSH, or Secure Shell, is a cryptographic network protocol designed to secure data communication, remote command execution, and file transfers between devices. For IoT devices, SSH provides an encrypted channel that ensures data privacy and protects against unauthorized access. This is particularly important as IoT devices often operate in environments where security risks are high.
How Remote IoT SSH Works
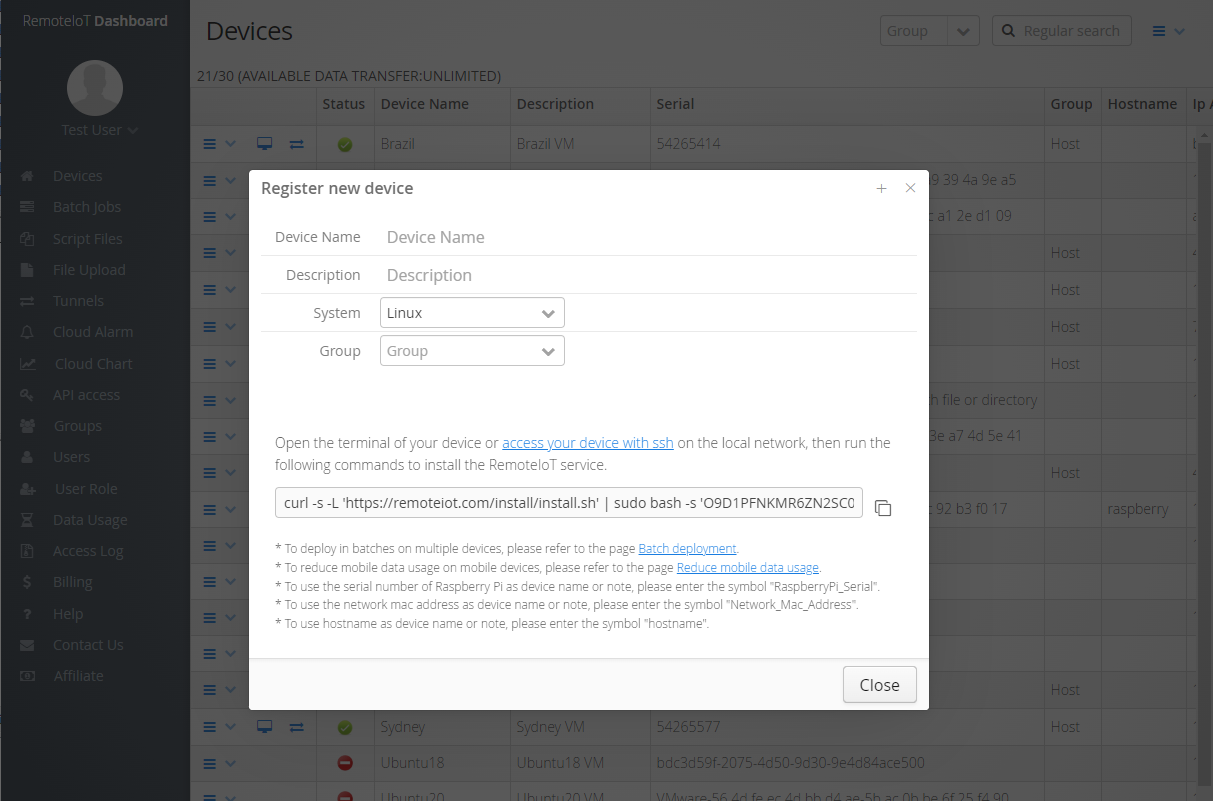
Remote IoT SSH works by establishing a secure connection between a client device and an IoT device. The process involves authentication, encryption, and data integrity checks. Once the connection is established, users can remotely manage and interact with IoT devices as if they were physically present.
Why Choose SSH for IoT Devices
Choosing SSH for IoT devices offers several advantages, including enhanced security, ease of use, and compatibility with various platforms. Unlike other protocols, SSH provides robust encryption and authentication mechanisms, making it an ideal choice for securing remote IoT communications.
Key Benefits of Using SSH for IoT Devices
Using SSH for IoT devices brings numerous benefits that contribute to the overall security and efficiency of your network. Below are some of the most significant advantages:
- Enhanced Security: SSH encrypts all data transmitted between devices, protecting against eavesdropping and data breaches.
- Authentication: SSH supports strong authentication methods, such as public-key cryptography, ensuring only authorized users can access IoT devices.
- Scalability: SSH can handle a large number of devices and users, making it suitable for enterprise-level IoT deployments.
- Compatibility: SSH works across different platforms and operating systems, providing flexibility in managing diverse IoT ecosystems.
Top Remote IoT Device SSH Solutions
1. OpenSSH
OpenSSH is one of the most widely used SSH implementations, known for its open-source nature and robust security features. It supports a wide range of encryption algorithms and authentication methods, making it a reliable choice for securing IoT devices.
2. Dropbear SSH
Dropbear SSH is a lightweight SSH server and client designed for embedded systems, making it ideal for resource-constrained IoT devices. Its small footprint and efficient performance make it a popular choice in the IoT space.
3. Bitvise SSH Server
Bitvise SSH Server offers a user-friendly interface and advanced security features, such as two-factor authentication and session monitoring. It is particularly well-suited for organizations requiring high levels of security and compliance.
Essential Security Features to Look For
When selecting an SSH solution for your IoT devices, it's crucial to consider the following security features:
- Encryption: Ensure the solution uses strong encryption algorithms, such as AES-256, to protect data in transit.
- Authentication: Look for support for multi-factor authentication and public-key cryptography to enhance security.
- Logging and Auditing: Choose solutions that provide detailed logs and auditing capabilities to monitor and track access attempts.
- Regular Updates: Ensure the solution receives regular updates and patches to address emerging security threats.
Comparison of Leading SSH Solutions
Below is a comparison of the top remote IoT device SSH solutions based on key criteria:
| Feature | OpenSSH | Dropbear SSH | Bitvise SSH Server |
|---|---|---|---|
| Platform Compatibility | Wide range of platforms | Embedded systems | Windows-based systems |
| Resource Usage | Standard usage | Lightweight | Higher resource usage |
| Security Features | Comprehensive | Basic | Advanced |
How to Implement SSH for IoT Devices
Step 1: Choose the Right SSH Solution
Select an SSH solution that aligns with your specific requirements, considering factors such as platform compatibility, security features, and resource usage.
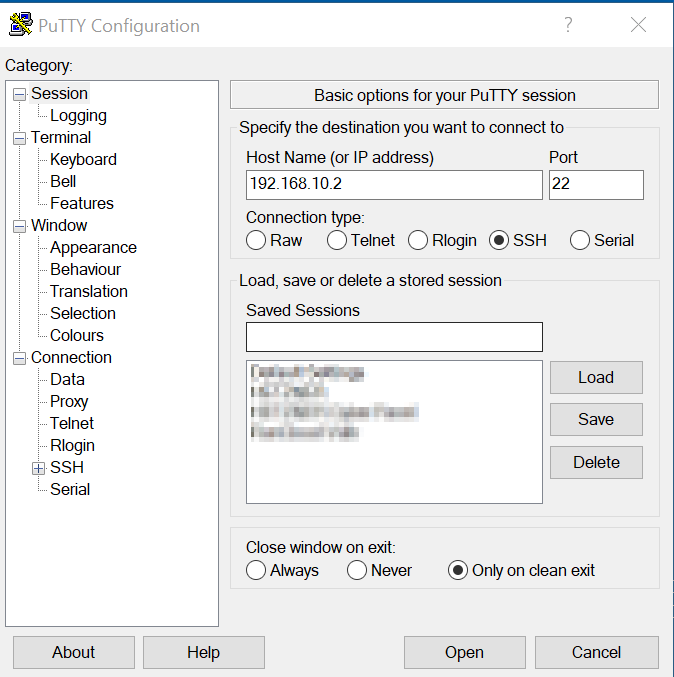
Step 2: Configure SSH Settings
Set up SSH on your IoT devices by configuring settings such as port numbers, encryption algorithms, and authentication methods. Refer to the documentation of your chosen solution for detailed instructions.
Step 3: Test the Connection
Once configured, test the SSH connection to ensure it is functioning correctly. This step is crucial to identify and resolve any issues before deploying the solution in a production environment.
Common Challenges in Remote IoT SSH
While SSH offers numerous benefits for IoT devices, there are also challenges to consider:
- Resource Constraints: Many IoT devices have limited processing power and memory, which can impact the performance of SSH.
- Network Latency: Remote SSH connections may experience delays due to network latency, affecting the responsiveness of IoT devices.
- Key Management: Managing SSH keys across multiple devices can be complex, requiring robust key management practices.
Future Trends in IoT SSH Technology
The future of IoT SSH technology looks promising, with several trends shaping its development:
- Quantum-Resistant Encryption: As quantum computing advances, SSH solutions will need to adopt quantum-resistant encryption algorithms to ensure long-term security.
- AI-Powered Security: Artificial intelligence will play a significant role in enhancing SSH security by detecting and mitigating threats in real-time.
- Edge Computing Integration: SSH will increasingly integrate with edge computing to provide secure and efficient communication for IoT devices at the network edge.
Best Practices for Secure IoT SSH
To ensure the security of your IoT SSH implementation, follow these best practices:
- Use Strong Passwords: Implement complex passwords and enforce regular updates to prevent unauthorized access.
- Enable Two-Factor Authentication: Add an extra layer of security by requiring users to provide two forms of identification before accessing IoT devices.
- Regularly Update SSH Software: Keep your SSH solution up to date with the latest patches and updates to address vulnerabilities.
Conclusion and Next Steps
In conclusion, the best remote IoT device SSH solutions offer a secure and efficient way to manage and interact with IoT devices from anywhere in the world. By understanding the key benefits, challenges, and best practices, you can make informed decisions about securing your IoT infrastructure.
We encourage you to take the next step by exploring the SSH solutions mentioned in this article and implementing them in your IoT projects. Don't forget to share your thoughts and experiences in the comments section below. For more insights and updates on IoT security, subscribe to our newsletter or follow us on social media.
References:
18 Best SSH Client Software Tools for Windows/MAC/Linux (2024)
How to remotely ssh iot device in web browser
Best RemoteIoT Device SSH A Comprehensive Guide For Secure Remote Access