Securely Connect Remote IoT VPC AWS: A Comprehensive Guide
In the rapidly evolving world of IoT (Internet of Things), securely connecting remote IoT devices to AWS Virtual Private Cloud (VPC) is more critical than ever. With the increasing reliance on cloud computing and IoT devices, organizations must prioritize robust security measures to safeguard their data and infrastructure. This article will explore the best practices and strategies for securely connecting remote IoT devices to AWS VPC.
As businesses expand their IoT networks, the need for secure connectivity grows exponentially. AWS VPC provides an isolated environment where organizations can deploy their IoT applications securely. Understanding how to integrate IoT devices into this secure ecosystem is essential for maintaining data integrity and privacy.
This guide will cover everything from basic concepts to advanced strategies for securing remote IoT devices within AWS VPC. Whether you're a beginner or an experienced professional, this article will provide valuable insights to enhance your understanding of IoT security in AWS environments.
- What Happened Toarah Goldberg American Idol
- Taylor Swift Brothers Name
- Evy Norlund Today Jamesarren And Wife
- Moji Afolayan Age
Table of Contents
- Introduction to IoT and AWS VPC
- Why Secure Connections Are Critical
- AWS VPC Basics
- Securing Remote IoT Devices
- Best Practices for Secure Connections
- Tools and Services for Secure Connections
- Common Security Challenges
- Implementing VPC Endpoints
- Monitoring and Logging
- Conclusion and Next Steps
Introduction to IoT and AWS VPC
The Internet of Things (IoT) has transformed industries by enabling devices to communicate and share data seamlessly. However, as IoT adoption grows, so does the need for secure connectivity. AWS VPC plays a pivotal role in ensuring that IoT devices operate in a secure and controlled environment. By leveraging AWS VPC, organizations can isolate their IoT applications from the public internet, reducing the risk of unauthorized access.
AWS VPC offers a range of features that make it ideal for IoT deployments, including customizable network configurations, secure data transfer, and advanced security controls. Understanding the fundamentals of AWS VPC is essential for anyone looking to securely connect remote IoT devices.
Why Secure Connections Are Critical
In today's digital landscape, data breaches and cyberattacks are a significant concern for organizations of all sizes. Securely connecting remote IoT devices to AWS VPC is crucial for protecting sensitive information and maintaining operational continuity. Without proper security measures, IoT devices can become vulnerable to attacks, leading to data loss, financial damage, and reputational harm.
According to a report by Gartner, the global IoT security market is expected to reach $3.1 billion by 2023. This growth highlights the increasing demand for robust security solutions in IoT environments. By prioritizing secure connections, organizations can mitigate risks and ensure the reliability of their IoT systems.
AWS VPC Basics
Amazon Web Services (AWS) Virtual Private Cloud (VPC) is a service that allows users to create an isolated virtual network in the AWS Cloud. This network can be customized to meet specific security and operational requirements. Key features of AWS VPC include:
- Subnets for organizing resources
- Security groups for controlling access
- Network access control lists (ACLs) for additional security
- Internet gateways for connecting to the public internet
These features enable organizations to deploy IoT applications in a secure and controlled environment. By leveraging AWS VPC, businesses can ensure that their IoT devices communicate securely and efficiently.
Securing Remote IoT Devices
Network Security
Network security is a critical component of securing remote IoT devices in AWS VPC. By implementing strong network security measures, organizations can protect their IoT systems from unauthorized access and potential threats. Some best practices for network security include:
- Using private subnets for sensitive resources
- Configuring security groups to restrict inbound and outbound traffic
- Implementing network ACLs for additional protection
These measures help create a secure network environment where IoT devices can operate without compromising data integrity.
Data Encryption
Data encryption is another vital aspect of securing remote IoT devices. Encrypting data in transit and at rest ensures that sensitive information remains protected from unauthorized access. AWS provides several encryption options, including:
- AWS Key Management Service (KMS) for managing encryption keys
- SSL/TLS for securing data in transit
- Amazon S3 server-side encryption for storing data securely
By leveraging these encryption tools, organizations can enhance the security of their IoT systems and protect valuable data.
Best Practices for Secure Connections
To ensure secure connections between remote IoT devices and AWS VPC, organizations should adopt the following best practices:
- Use strong authentication mechanisms, such as AWS Identity and Access Management (IAM)
- Regularly update and patch IoT devices to address security vulnerabilities
- Implement network segmentation to isolate sensitive resources
- Monitor network traffic for suspicious activity
By following these best practices, organizations can minimize security risks and ensure the reliability of their IoT systems.
Tools and Services for Secure Connections
AWS offers a range of tools and services to help organizations securely connect remote IoT devices to VPC. Some of these tools include:
- AWS IoT Core for managing IoT devices and data
- AWS Shield for protecting against DDoS attacks
- AWS WAF for filtering malicious web traffic
These tools provide comprehensive security solutions for IoT environments, enabling organizations to protect their systems from a wide range of threats.
Common Security Challenges
While AWS VPC provides a robust platform for securing IoT devices, organizations may face several challenges when implementing secure connections. Common challenges include:
- Managing large numbers of IoT devices
- Ensuring consistent security policies across multiple devices
- Addressing hardware and software vulnerabilities
By understanding these challenges and implementing effective solutions, organizations can overcome obstacles and maintain secure IoT systems.
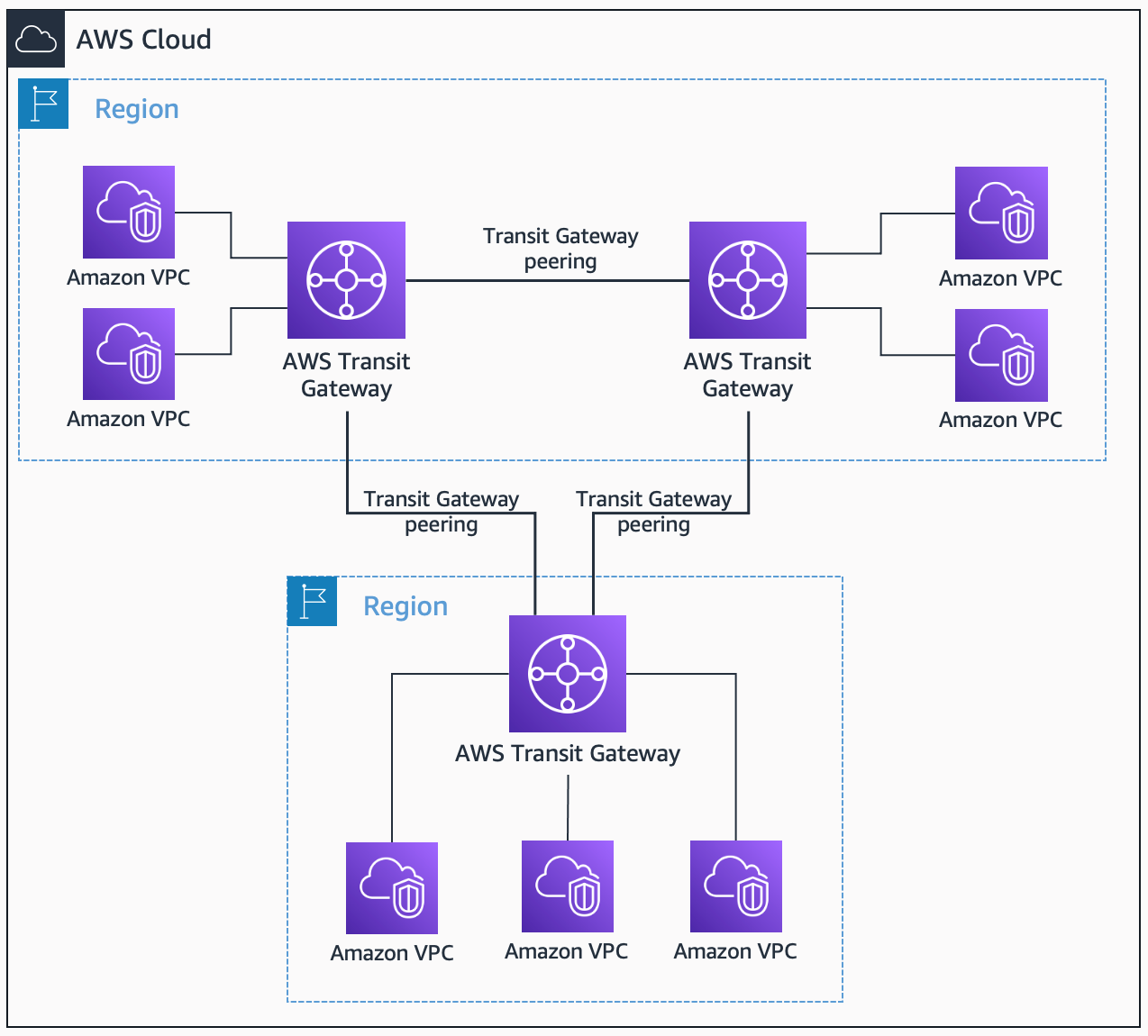
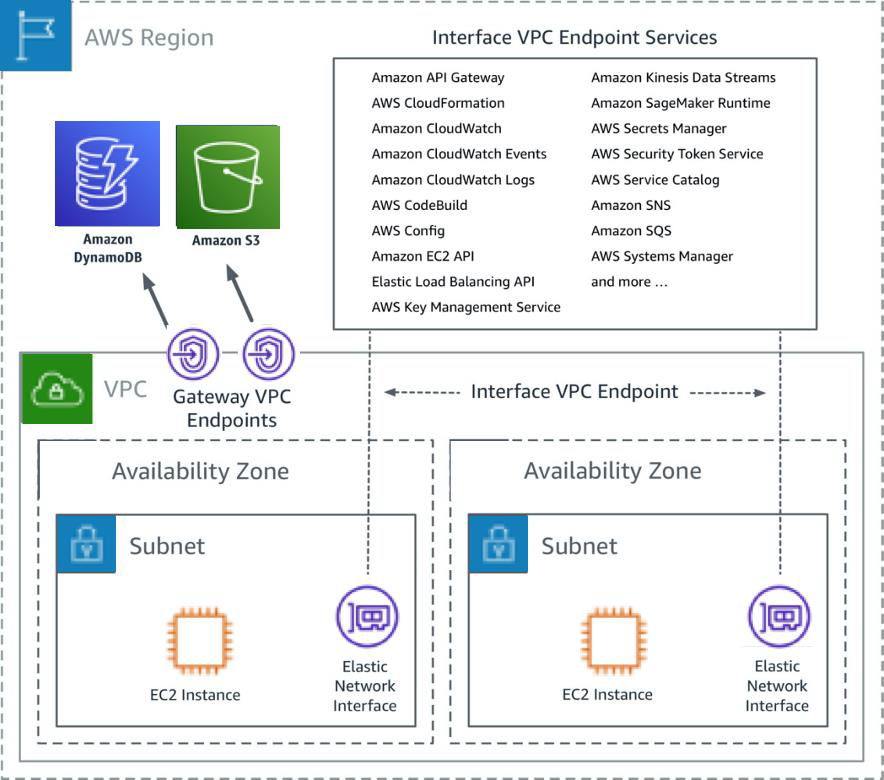
Implementing VPC Endpoints
VPC endpoints allow organizations to establish private connections between their IoT devices and AWS services without using the public internet. This feature enhances security by reducing the risk of data exposure during transmission. To implement VPC endpoints, organizations should:
- Create a VPC endpoint for the desired AWS service
- Configure security groups to control access to the endpoint
- Test the endpoint to ensure proper functionality
By leveraging VPC endpoints, organizations can improve the security and performance of their IoT systems.
Monitoring and Logging
Monitoring and logging are essential for maintaining the security of IoT systems in AWS VPC. By continuously monitoring network activity and analyzing logs, organizations can detect and respond to potential threats in real-time. AWS provides several tools for monitoring and logging, including:
- AWS CloudTrail for tracking API activity
- AWS CloudWatch for monitoring metrics and logs
- AWS Config for assessing resource configurations
These tools enable organizations to maintain visibility into their IoT systems and address security issues proactively.
Conclusion and Next Steps
Securing remote IoT devices in AWS VPC is a critical task for organizations looking to protect their data and infrastructure. By following the strategies and best practices outlined in this article, businesses can enhance the security of their IoT systems and ensure reliable operations. Remember to:
- Implement strong network security measures
- Use encryption to protect sensitive data
- Leverage AWS tools and services for comprehensive security
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into IoT security and AWS solutions. Together, we can build a safer and more connected digital world.
Securely Connect RemoteIoT VPC To AWS A Comprehensive Guide
What are VPC endpoints? Securely Access Services Over AWS PrivateLink

How To Securely Connect RemoteIoT VPC AWS A Comprehensive Guide