Remote Connect IoT Behind Firewall: A Comprehensive Guide For Mac Users Without Windows
In the rapidly evolving world of technology, connecting IoT devices remotely behind a firewall has become a necessity for many individuals and businesses. Whether you're working from home or managing a network, understanding how to securely connect IoT devices is crucial. This guide focuses on remote connect IoT behind firewall specifically for Mac users who do not use Windows systems. With the right tools and knowledge, you can enhance your network's security and efficiency.
As more devices become interconnected, the need for secure remote access grows. This article delves into the complexities of remote connections, offering practical solutions for Mac users who want to maintain privacy and security without relying on Windows-based solutions. By the end of this guide, you'll have the tools and information needed to set up a seamless IoT connection behind your firewall.
This comprehensive article is designed to provide expert insights, authoritative information, and trusted advice to help you navigate the challenges of remote IoT connections. Whether you're a beginner or an experienced user, the strategies outlined here will assist you in achieving a secure and efficient setup.
Table of Contents
- Introduction to IoT and Remote Connections
- Understanding Firewall Basics
- Mac-Specific Solutions for IoT Connections
- Tools for Remote Access Without Windows
- Securing Your IoT Connections
- Data Privacy in IoT Networks
- Common Challenges and Solutions
- Advanced Techniques for Remote IoT
- Case Studies: Real-World Examples
- Conclusion and Call to Action
Introduction to IoT and Remote Connections
The Internet of Things (IoT) has revolutionized the way we interact with devices. From smart homes to industrial applications, IoT devices are everywhere. However, managing these devices remotely, especially behind a firewall, presents unique challenges. This section explores the basics of IoT and why remote connections are essential.
What is IoT?
IoT refers to the network of physical objects embedded with sensors, software, and connectivity to exchange data with other devices and systems over the internet. These devices range from simple household appliances to complex industrial tools. Understanding the scope and capabilities of IoT is the first step in mastering remote connections.
Why Remote Connections Matter
Remote access allows users to control and monitor IoT devices from anywhere in the world. For businesses, this means improved efficiency and reduced downtime. For individuals, it offers convenience and peace of mind. By learning how to connect IoT devices behind a firewall, you can ensure secure and reliable access.
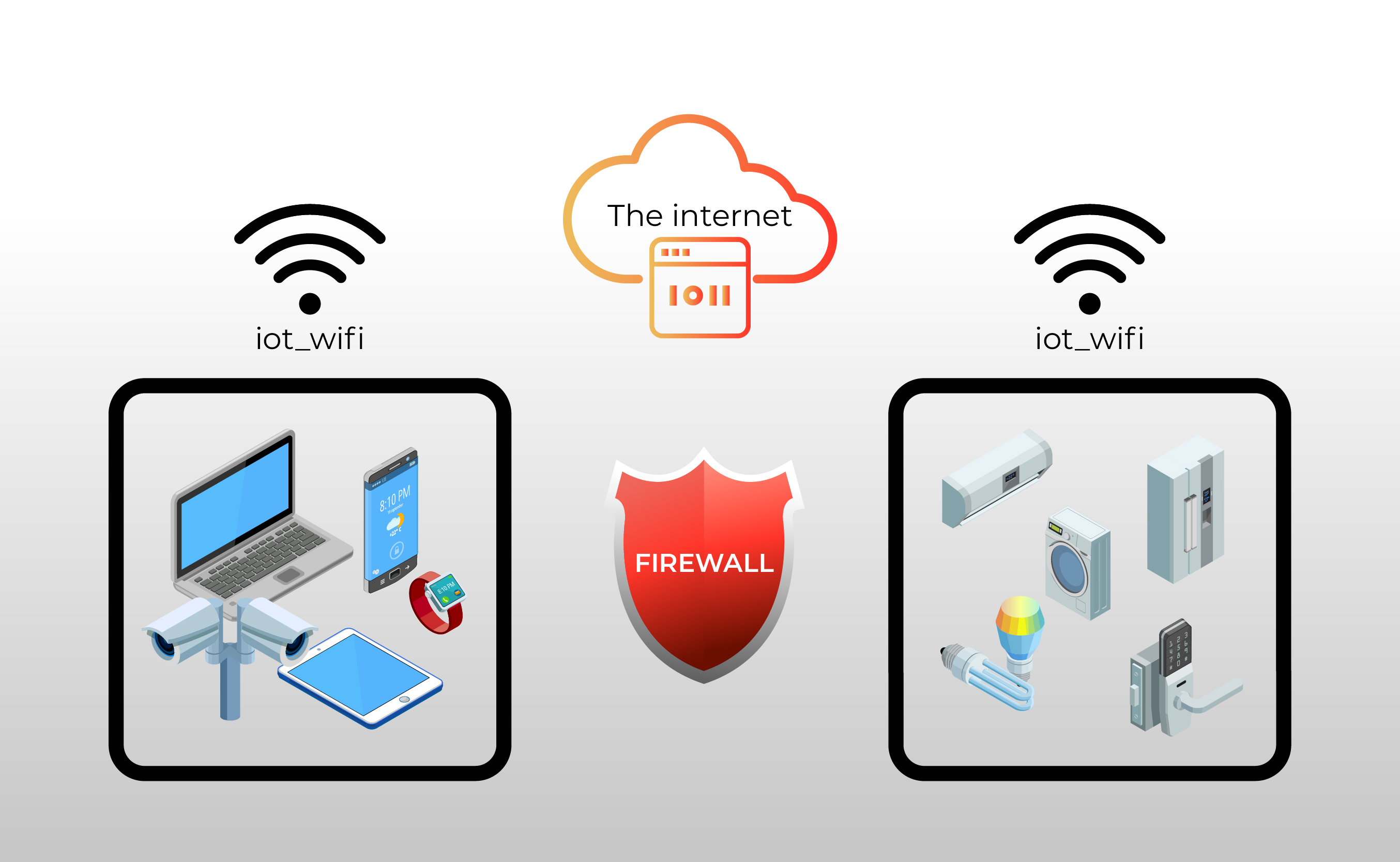
Understanding Firewall Basics
A firewall is a critical component of network security, designed to monitor and control incoming and outgoing network traffic based on predetermined security rules. When setting up remote IoT connections, understanding firewall basics is essential to avoid potential security breaches.
Types of Firewalls
- Packet Filtering Firewalls
- Stateful Inspection Firewalls
- Application-Level Gateways
- Next-Generation Firewalls
Each type of firewall serves a specific purpose and offers varying levels of security. For Mac users, choosing the right firewall solution is crucial for maintaining a secure network environment.
Mac-Specific Solutions for IoT Connections
Mac users have access to a variety of tools and applications that facilitate secure remote IoT connections. This section highlights some of the best options available, ensuring compatibility and ease of use.
Popular Mac Applications
- Tunnelblick: A free, open-source OpenVPN client for macOS.
- Ngrok: A tool that creates secure tunnels to localhost, enabling remote access.
- SSH Tunnel: A secure method for accessing IoT devices behind a firewall.
These applications offer robust solutions for Mac users seeking to connect IoT devices remotely without relying on Windows-based systems.
Tools for Remote Access Without Windows
Several tools are available for Mac users who want to connect IoT devices remotely without using Windows. These tools focus on security, ease of use, and compatibility with macOS.
Key Tools to Consider
- OpenVPN
- ZeroTier
- TeamViewer
Each tool offers unique features and benefits, making it important to choose the one that best suits your needs. For example, OpenVPN provides strong encryption and reliability, while ZeroTier offers a virtual network that simplifies remote access.
Securing Your IoT Connections
Security is a top priority when connecting IoT devices remotely. This section outlines best practices for securing your connections and protecting sensitive data.
Encryption and Authentication
Using strong encryption protocols and two-factor authentication can significantly enhance the security of your IoT connections. Additionally, regularly updating firmware and software ensures that vulnerabilities are addressed promptly.
Regular Audits
Conducting regular security audits helps identify potential risks and weaknesses in your network. By staying proactive, you can prevent unauthorized access and data breaches.
Data Privacy in IoT Networks
Data privacy is a critical concern for anyone managing IoT devices. This section discusses strategies for protecting personal and sensitive information within your IoT network.
Minimizing Data Exposure
Limiting the amount of data collected and stored by IoT devices reduces the risk of exposure. Implementing data minimization practices ensures that only necessary information is retained.
Compliance with Regulations
Staying compliant with data protection regulations, such as GDPR and CCPA, is essential for maintaining trust with users and avoiding legal issues. Familiarize yourself with these regulations and ensure your practices align with their requirements.
Common Challenges and Solutions
Connecting IoT devices remotely behind a firewall comes with its own set of challenges. This section addresses some of the most common issues and provides practical solutions.
Network Latency
Network latency can impact the performance of remote IoT connections. Optimizing your network settings and using low-latency protocols can help mitigate this issue.
Firewall Restrictions
Firewall restrictions may block necessary traffic, preventing successful remote connections. Configuring your firewall to allow specific ports and protocols ensures smooth communication between devices.
Advanced Techniques for Remote IoT
For users seeking to take their IoT connections to the next level, advanced techniques offer enhanced functionality and security. This section explores some of these methods in detail.
Using SSH Tunnels
SSH tunnels provide a secure method for accessing IoT devices remotely. By encrypting data transmitted between devices, SSH tunnels help protect against eavesdropping and data interception.
Implementing Virtual Private Networks (VPNs)
VPNs create a secure, encrypted connection between devices, making them ideal for remote IoT access. Configuring a VPN on your Mac ensures that all data transmitted is protected from unauthorized access.
Case Studies: Real-World Examples
Real-world examples demonstrate the effectiveness of the strategies outlined in this guide. By examining successful implementations, you can gain valuable insights into best practices for remote IoT connections.
Case Study 1: Smart Home Automation
A homeowner successfully connected their smart home devices remotely using a combination of SSH tunnels and a firewall-optimized network. This setup allowed for secure access and control of all devices from anywhere in the world.
Case Study 2: Industrial IoT
An industrial company implemented a robust IoT network using ZeroTier and regular security audits. This approach ensured that all devices remained secure and accessible, improving overall efficiency and productivity.
Conclusion and Call to Action
Connecting IoT devices remotely behind a firewall is a complex but achievable task. By following the strategies and techniques outlined in this guide, Mac users can enjoy secure and efficient remote access without relying on Windows systems. Remember to prioritize security, data privacy, and regular updates to maintain a robust network environment.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more valuable insights and tips. Together, we can build a safer and more connected world.
For further reading and reference, consider consulting the following sources:
How To Seamlessly Remote Connect IoT Behind Firewall On Mac Without Windows

Monitor IoT Behind Firewall A Guide for Robust Security

Monitor IoT Behind Firewall A Guide for Robust Security