RemoteIoT Behind Firewall Examples: Unlocking Secure Connectivity
In today's interconnected world, RemoteIoT behind firewall examples play a crucial role in ensuring secure and efficient communication between devices, networks, and systems. As IoT technology continues to expand, organizations face growing challenges in maintaining robust cybersecurity measures while enabling seamless connectivity. Understanding how to manage IoT devices behind firewalls is essential for both IT professionals and decision-makers.
The proliferation of IoT devices has revolutionized industries, offering innovative solutions for automation, monitoring, and data collection. However, with this rapid expansion comes the need for secure implementation strategies. Firewalls act as critical barriers that protect internal networks from external threats, but they also pose challenges for IoT devices that require access to external resources.
This article delves into the concept of RemoteIoT behind firewalls, providing practical examples and strategies to ensure secure connectivity. Whether you're an IT administrator, a network engineer, or a business leader, this guide will equip you with the knowledge and tools needed to implement effective solutions for your organization.
- Mcdonalds Nutrition Menu
- Cooke Maroney Age
- Where Can I Watch The Trump Musk Interview
- Actor Jeremy Allen White
Table of Contents
- Introduction to RemoteIoT
- Firewall Basics and Importance
- Challenges of RemoteIoT Behind Firewalls
- Secure Connection Methods for RemoteIoT
- Data Encryption Techniques
- Network Segmentation Strategies
- Real-World RemoteIoT Behind Firewall Examples
- Best Practices for RemoteIoT Security
- Emerging Technologies in RemoteIoT
- Conclusion and Call to Action
Introduction to RemoteIoT
RemoteIoT refers to the practice of managing and interacting with IoT devices located in remote environments. These devices often operate within private networks protected by firewalls, which can complicate communication processes. Understanding the fundamentals of RemoteIoT is essential for ensuring secure and reliable connectivity.
IoT devices rely on consistent network access to function effectively. However, traditional firewalls are designed to block unauthorized access, creating potential barriers for IoT devices that need external connectivity. By exploring RemoteIoT behind firewall examples, organizations can develop strategies to overcome these challenges while maintaining strong security protocols.
Firewall Basics and Importance
A firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. It acts as a barrier between trusted internal networks and untrusted external networks, such as the internet. Firewalls are critical for protecting sensitive data and preventing unauthorized access.
In the context of RemoteIoT, firewalls play a dual role. They safeguard internal networks from external threats while enabling authorized devices to communicate securely. Understanding firewall configurations and their impact on IoT devices is essential for designing effective RemoteIoT solutions.
Challenges of RemoteIoT Behind Firewalls
Implementing RemoteIoT behind firewalls presents several challenges:
- Network Restrictions: Firewalls often block unauthorized traffic, making it difficult for IoT devices to establish connections.
- Latency Issues: Complex firewall configurations can introduce delays in communication, affecting device performance.
- Security Concerns: Opening firewall ports for IoT devices may expose networks to potential vulnerabilities.
Addressing these challenges requires a combination of advanced security measures and optimized network configurations.
Secure Connection Methods for RemoteIoT
VPN Solutions
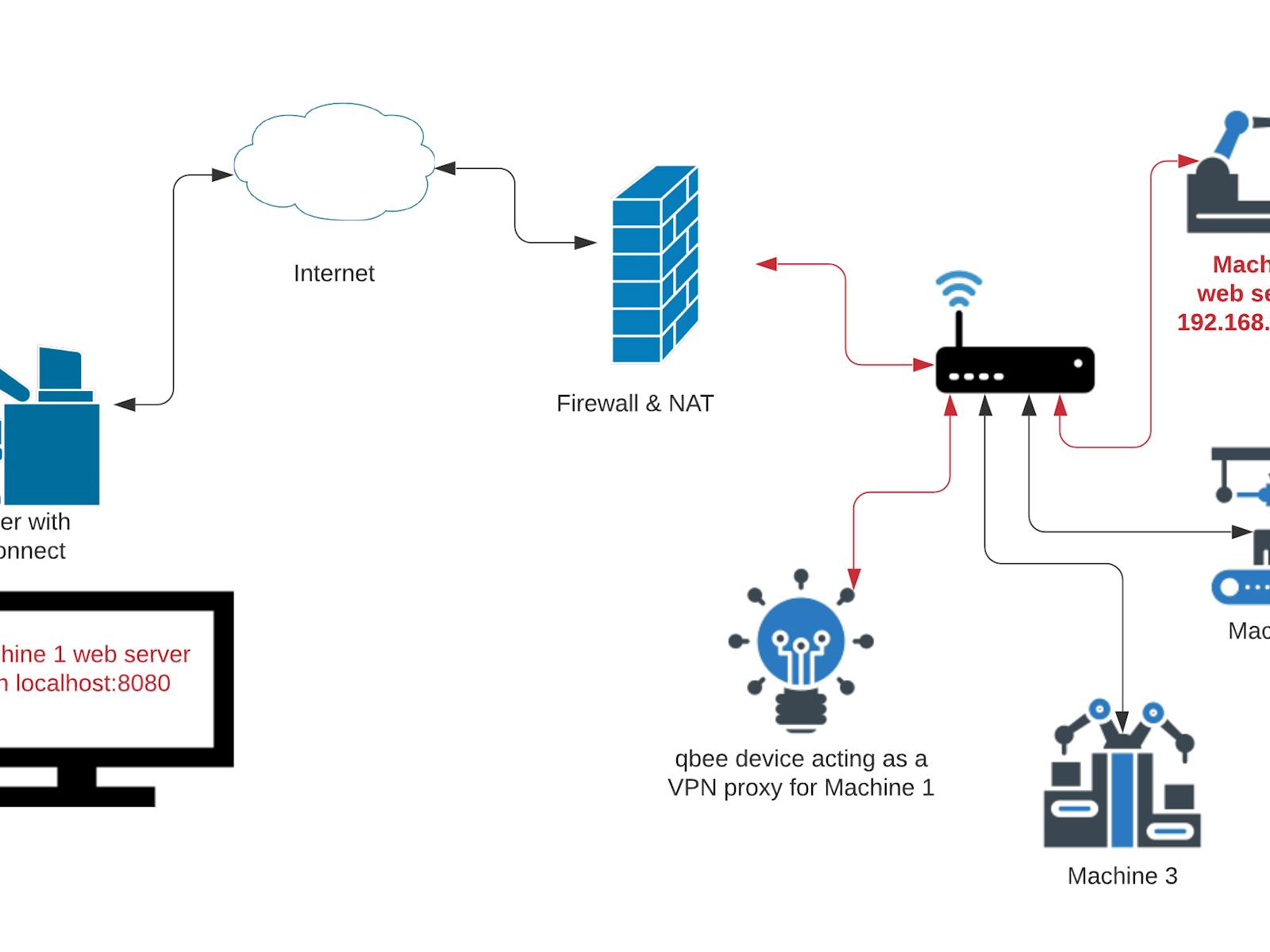
Virtual Private Networks (VPNs) provide a secure tunnel for IoT devices to communicate across public networks. By encrypting data and routing it through a secure channel, VPNs ensure that sensitive information remains protected from unauthorized access.
SSH Tunneling
Secure Shell (SSH) tunneling offers another effective method for securing RemoteIoT connections. This technique involves encapsulating data within an encrypted SSH session, allowing IoT devices to bypass firewall restrictions while maintaining high levels of security.
Data Encryption Techniques
Data encryption is a fundamental aspect of securing RemoteIoT communications. Advanced encryption protocols, such as AES (Advanced Encryption Standard) and TLS (Transport Layer Security), play a vital role in protecting sensitive information. Organizations should implement robust encryption mechanisms to safeguard data transmitted between IoT devices and external networks.
Network Segmentation Strategies
Network segmentation involves dividing a network into smaller, isolated segments to enhance security and improve performance. By implementing network segmentation strategies, organizations can limit the exposure of IoT devices to potential threats while maintaining efficient connectivity.
Key benefits of network segmentation include:
- Reduced attack surface
- Improved network performance
- Enhanced monitoring and control
Real-World RemoteIoT Behind Firewall Examples
Several industries have successfully implemented RemoteIoT solutions behind firewalls. For instance, healthcare organizations use IoT devices to monitor patient vitals, while manufacturing companies rely on IoT sensors for predictive maintenance. These real-world examples demonstrate the effectiveness of secure RemoteIoT implementations.
One notable example involves a smart factory that leverages IoT devices to optimize production processes. By deploying a combination of firewalls, encryption protocols, and network segmentation strategies, the factory ensures secure communication between devices while maintaining high levels of operational efficiency.
Best Practices for RemoteIoT Security
To ensure secure RemoteIoT implementations, organizations should adhere to the following best practices:
- Regularly update firewall rules and configurations
- Implement strong authentication mechanisms
- Monitor network activity for suspicious behavior
- Conduct regular security audits and assessments
By following these guidelines, organizations can minimize risks and maximize the benefits of RemoteIoT technology.
Emerging Technologies in RemoteIoT
Advancements in technology continue to shape the future of RemoteIoT. Emerging solutions, such as edge computing and 5G networks, offer new possibilities for enhancing connectivity and security. These technologies enable faster data processing and reduced latency, making them ideal for RemoteIoT applications.
For example, edge computing allows data to be processed closer to the source, reducing the need for constant communication with external networks. This approach not only improves performance but also enhances security by minimizing exposure to potential threats.
Conclusion and Call to Action
RemoteIoT behind firewall examples highlight the importance of secure and efficient connectivity in modern networks. By understanding the challenges and implementing effective solutions, organizations can unlock the full potential of IoT technology while maintaining robust cybersecurity measures.
We encourage readers to explore the strategies and techniques discussed in this article and apply them to their own RemoteIoT implementations. Your feedback and insights are valuable, so please feel free to leave a comment or share this article with others who may benefit from it. Together, we can advance the field of RemoteIoT and drive innovation in secure connectivity solutions.
Sources:
- IEEE Xplore Digital Library
- International Journal of IoT and Applications
- Network Security Journal

RemoteIoT Behind Firewall Examples A Comprehensive Guide To Secure
RemoteIoT Behind Firewall Examples A Comprehensive Guide To Secure
Mastering RemoteIoT Behind Firewall On Windows A Comprehensive Guide