AWS IoT Secure Tunnel API: Revolutionizing Secure Remote Access
In today's interconnected world, AWS IoT Secure Tunnel API has emerged as a game-changer for secure remote access solutions. This powerful tool allows users to establish encrypted connections between devices and applications without exposing them to public networks. Whether you're managing IoT devices remotely or ensuring secure communication between systems, AWS IoT Secure Tunnel API provides the reliability and security required for modern digital infrastructure.
As businesses increasingly rely on IoT devices for operations, the need for secure communication channels becomes paramount. Traditional methods of remote access often expose devices to potential vulnerabilities. AWS IoT Secure Tunnel API addresses these challenges by offering a secure, private, and efficient way to connect devices and applications.
This article delves into the capabilities, benefits, and implementation strategies of AWS IoT Secure Tunnel API. By the end of this comprehensive guide, you'll have a thorough understanding of how this service can enhance your IoT infrastructure's security and efficiency while maintaining compliance with industry standards.
Table of Contents
- Overview of AWS IoT Secure Tunnel API
- Architecture and Components
- Security Features
- Use Cases and Applications
- Implementation Steps
- Benefits of Using AWS IoT Secure Tunnel API
- Comparison with Traditional Methods
- Pricing and Cost Considerations
- Integration with Other AWS Services
- Best Practices for Optimal Usage
Overview of AWS IoT Secure Tunnel API
AWS IoT Secure Tunnel API is a service designed to facilitate secure remote access to IoT devices without requiring public IP addresses or opening firewall ports. This solution is particularly beneficial for scenarios where devices are located behind NAT or firewalls, making traditional remote access methods impractical or insecure.
The service operates by creating encrypted tunnels between a client application and a target device through AWS cloud infrastructure. These tunnels ensure that all communication remains private and secure, even when devices are not directly accessible from the internet. By leveraging AWS IoT Core, the API integrates seamlessly with existing AWS services, providing a robust and scalable solution for remote device management.
How AWS IoT Secure Tunnel API Works
At its core, the API employs a broker-based architecture where AWS acts as the intermediary for all communication between devices and applications. This eliminates the need for direct connections, reducing exposure to potential security threats. The process involves three primary components:
- Client application initiating the tunnel request
- AWS IoT Secure Tunnel service managing the connection
- Target device receiving and responding to the connection request
Architecture and Components
The architecture of AWS IoT Secure Tunnel API is built around several key components that work together to provide a secure and efficient remote access solution. Understanding these components is essential for effectively implementing and managing the service.
Key Components
- Client SDK: A software development kit used by applications to initiate secure tunnel requests.
- Tunnel Manager: An AWS service responsible for creating and managing tunnels between clients and devices.
- Device SDK: A library installed on IoT devices to handle incoming tunnel requests and establish secure connections.
These components work in harmony to ensure seamless communication while maintaining high levels of security and performance.
Security Features
Security is at the heart of AWS IoT Secure Tunnel API's design. The service employs multiple layers of protection to safeguard data and ensure secure communication between devices and applications.
Encryption and Authentication
All data transmitted through AWS IoT Secure Tunnel API is encrypted using industry-standard protocols. Additionally, the service supports robust authentication mechanisms, including:
- IoT device certificates
- Amazon Cognito for user authentication
- Custom authentication providers
These features ensure that only authorized parties can access sensitive information, reducing the risk of unauthorized access or data breaches.
Use Cases and Applications
AWS IoT Secure Tunnel API finds applications in various industries and scenarios where secure remote access is critical. Some common use cases include:
Industrial IoT
In manufacturing and industrial settings, the API enables engineers to remotely monitor and troubleshoot machinery without compromising security. This capability leads to improved operational efficiency and reduced downtime.
Smart Home Devices
For consumer electronics, AWS IoT Secure Tunnel API allows manufacturers to provide secure updates and support for connected devices, enhancing user experience while maintaining privacy.
Healthcare
In healthcare, the service ensures secure communication between medical devices and monitoring systems, complying with stringent regulatory requirements.
Implementation Steps
Implementing AWS IoT Secure Tunnel API involves several steps, from setting up the necessary infrastructure to configuring devices and applications. Below is a high-level overview of the process:
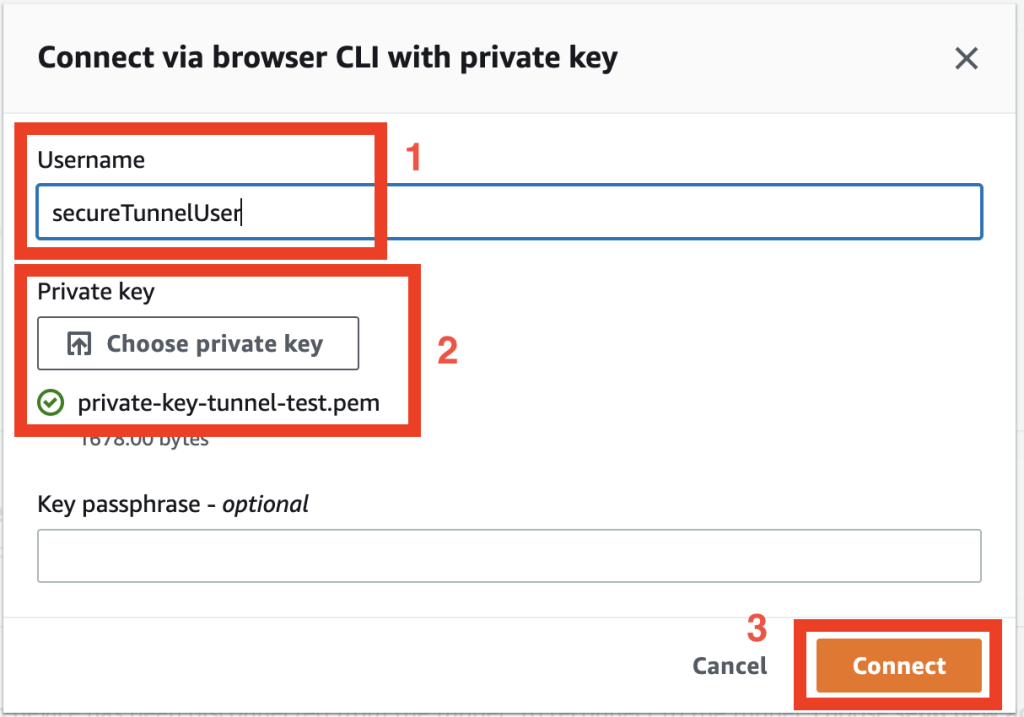
Step-by-Step Guide
- Set up an AWS account and enable IoT Core services.
- Install and configure the Device SDK on target devices.
- Integrate the Client SDK into your application for initiating tunnel requests.
- Test the connection to ensure secure and reliable communication.
Following these steps ensures a smooth deployment of AWS IoT Secure Tunnel API in your environment.
Benefits of Using AWS IoT Secure Tunnel API
Adopting AWS IoT Secure Tunnel API offers numerous advantages for organizations looking to enhance their IoT infrastructure's security and efficiency. Some key benefits include:
- Enhanced security through encrypted tunnels and robust authentication
- Improved scalability and flexibility for growing IoT deployments
- Reduced complexity in managing remote device access
- Compliance with industry standards and regulations
These benefits make AWS IoT Secure Tunnel API an attractive solution for businesses across various sectors.
Comparison with Traditional Methods
Compared to traditional remote access methods, AWS IoT Secure Tunnel API provides several advantages. Unlike methods that require exposing devices to public networks, this service ensures private communication without compromising security. Additionally, its integration with AWS IoT Core simplifies management and monitoring, reducing administrative overhead.
Key Differences
- No need for public IP addresses or port forwarding
- Reduced exposure to potential security threats
- Seamless integration with AWS ecosystem
These differences highlight the superiority of AWS IoT Secure Tunnel API over conventional approaches.
Pricing and Cost Considerations
AWS IoT Secure Tunnel API operates on a pay-as-you-go pricing model, making it cost-effective for businesses of all sizes. Pricing is based on the number of tunnels created and the amount of data transferred through the service. AWS provides detailed pricing information on its official website, allowing users to estimate costs based on their specific needs.
Cost Optimization Tips
- Monitor usage patterns to identify potential cost savings
- Utilize AWS Cost Explorer for detailed cost analysis
- Implement efficient data transfer strategies to minimize costs
By following these tips, organizations can effectively manage and optimize their AWS IoT Secure Tunnel API expenses.
Integration with Other AWS Services
AWS IoT Secure Tunnel API integrates seamlessly with other AWS services, enhancing its functionality and versatility. Some notable integrations include:
- AWS Lambda for automating tasks and processing data
- Amazon S3 for storing and managing data
- AWS IoT Core for comprehensive device management
These integrations enable users to build robust and scalable solutions that meet their specific requirements.
Best Practices for Optimal Usage
To maximize the benefits of AWS IoT Secure Tunnel API, it's essential to follow best practices for implementation and management. Some recommendations include:
- Regularly update device firmware and software to ensure compatibility and security
- Monitor tunnel activity and performance metrics for early detection of issues
- Implement strong authentication and authorization policies
- Follow AWS security best practices for securing your AWS environment
Adhering to these practices ensures optimal performance and security of your AWS IoT Secure Tunnel API implementation.
Conclusion
AWS IoT Secure Tunnel API represents a significant advancement in secure remote access solutions for IoT devices. By providing a private, encrypted communication channel, the service addresses critical security challenges faced by modern businesses. Its seamless integration with the AWS ecosystem and scalable architecture make it an ideal choice for organizations seeking to enhance their IoT infrastructure's security and efficiency.
We encourage readers to explore AWS IoT Secure Tunnel API further and consider implementing it in their environments. For more information, visit the official AWS documentation or consult with an AWS solutions architect. Don't forget to share your thoughts and experiences in the comments section below and explore other articles on our site for additional insights into AWS services and IoT technologies.
Sources:
- AWS Official Documentation - AWS IoT Secure Tunneling
- AWS Blog - AWS IoT Secure Tunneling Now Generally Available
- Gomyfinance Invest Open Now
- Where Can I Watch The Trump Musk Interview
- Ages Of The Jackson
- Matt Cimber
Connect to remote devices using AWS IoT Secure Tunneling The

Connect to remote devices using AWS IoT Secure Tunneling The

Connect to remote devices using AWS IoT Secure Tunneling The