How Do I Get Started With Secure Tunneling For AWS IoT Device Management?
Secure tunneling for AWS IoT Device Management has become a crucial component for modern IoT deployments. With the increasing demand for remote device management, secure tunneling offers a reliable solution to access and manage devices without exposing them to public networks. Whether you're a beginner or an experienced professional, understanding the fundamentals of secure tunneling is essential for ensuring robust security and seamless connectivity.
In this article, we will explore the basics of secure tunneling for AWS IoT Device Management. You'll learn how to set up secure tunnels, understand their importance, and discover best practices to ensure your IoT devices remain protected. This guide is designed to help you navigate through the complexities of IoT security while providing actionable insights.
Whether you're managing a few devices or a large-scale IoT deployment, secure tunneling plays a vital role in maintaining privacy and control. By the end of this article, you'll have a comprehensive understanding of how to implement secure tunneling effectively, ensuring your IoT ecosystem remains secure and efficient.
Table of Contents:
- Introduction to AWS IoT Device Management
- What is Secure Tunneling?
- Benefits of Secure Tunneling
- How to Get Started with Secure Tunneling
- Security Best Practices
- Common Use Cases
- Troubleshooting Tips
- Comparison with Other Methods
- Future of Secure Tunneling
- Conclusion
Introduction to AWS IoT Device Management
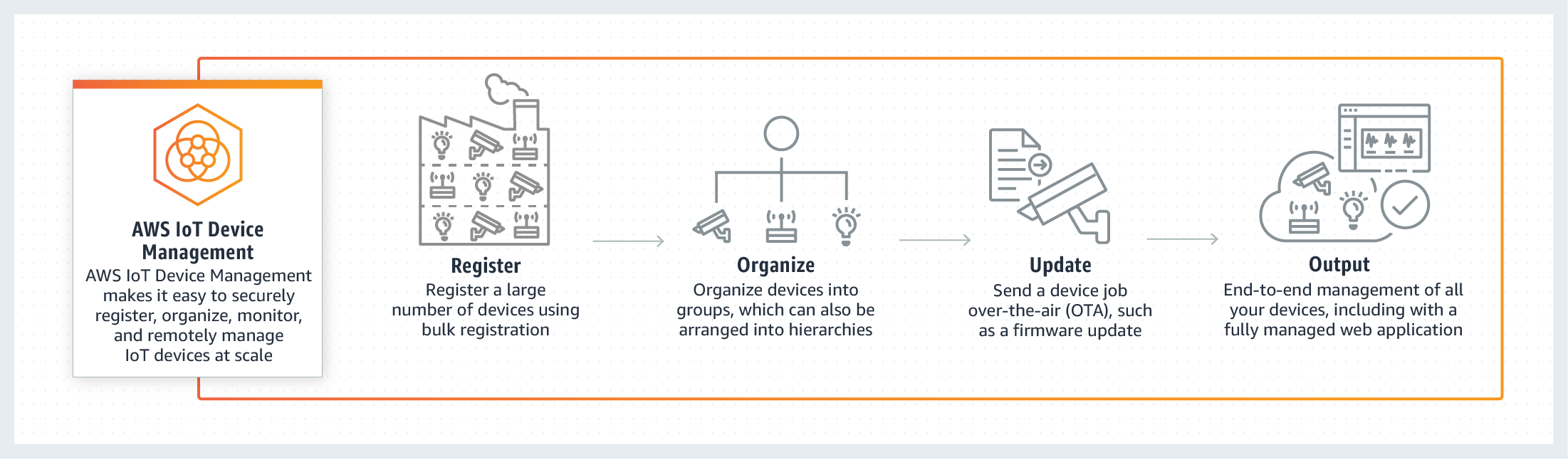
AWS IoT Device Management is a powerful platform designed to simplify the process of managing IoT devices at scale. It provides tools for organizing, monitoring, and remotely managing IoT devices, making it easier for businesses to maintain control over their IoT ecosystems. With features like device provisioning, firmware updates, and secure tunneling, AWS IoT Device Management ensures that your devices remain secure and operational.
One of the key features of AWS IoT Device Management is secure tunneling. This functionality allows users to establish secure, encrypted connections to IoT devices without exposing them to public networks. By leveraging secure tunneling, businesses can perform remote diagnostics, software updates, and troubleshooting without compromising security.
Understanding how secure tunneling works within AWS IoT Device Management is essential for anyone looking to implement robust IoT solutions. In the following sections, we'll delve deeper into the concept of secure tunneling and explore how it can benefit your IoT deployment.
What is Secure Tunneling?
Secure tunneling is a method of establishing a secure, encrypted connection between two devices over a network. In the context of AWS IoT Device Management, secure tunneling allows you to access IoT devices remotely without exposing them to public networks. This is achieved by creating a secure, encrypted tunnel that protects data transmitted between the devices.
Secure tunneling works by using Transport Layer Security (TLS) to encrypt data in transit. This ensures that even if the connection is intercepted, the data remains unreadable to unauthorized parties. AWS IoT Device Management simplifies the process of setting up secure tunnels, making it easier for users to manage their IoT devices securely.
Some of the key benefits of secure tunneling include enhanced security, reduced exposure to public networks, and simplified remote access. By implementing secure tunneling, businesses can ensure that their IoT devices remain protected while maintaining the ability to perform essential tasks remotely.
Benefits of Secure Tunneling
Secure tunneling offers numerous advantages for businesses looking to manage their IoT devices effectively. Below are some of the key benefits:
- Enhanced Security: Secure tunneling encrypts data in transit, ensuring that sensitive information remains protected from unauthorized access.
- Reduced Exposure: By avoiding the need to expose devices to public networks, secure tunneling minimizes the risk of cyberattacks and unauthorized access.
- Simplified Remote Access: Secure tunneling allows users to access IoT devices remotely without the need for complex network configurations.
- Cost-Effective: With secure tunneling, businesses can reduce the need for on-site visits, saving time and resources.
- Scalability: Secure tunneling can be easily scaled to accommodate large-scale IoT deployments, ensuring consistent performance and security.
These benefits make secure tunneling an essential tool for businesses looking to manage their IoT devices securely and efficiently.
How to Get Started with Secure Tunneling
Getting started with secure tunneling for AWS IoT Device Management involves several key steps. Below, we'll walk you through the process of setting up secure tunnels and accessing your IoT devices.
Step 1: Setting Up AWS IoT
Before you can create a secure tunnel, you need to set up AWS IoT Device Management. This involves creating an AWS account, setting up the necessary permissions, and configuring your IoT devices. Follow these steps:
- Create an AWS account if you don't already have one.
- Set up AWS IoT by navigating to the AWS Management Console and selecting "IoT" from the services menu.
- Configure your IoT devices by registering them in AWS IoT and setting up the necessary policies and certificates.
Once you've completed these steps, you'll be ready to move on to creating a secure tunnel.
Step 2: Creating a Tunnel
Creating a secure tunnel involves using the AWS IoT Device Management console or CLI to establish a connection between your device and the AWS cloud. Follow these steps:
- Open the AWS IoT Device Management console and navigate to the "Secure Tunneling" section.
- Select the device you want to connect to and click "Create Tunnel."
- Choose the type of tunnel you want to create (e.g., TCP or WebSocket) and configure the necessary settings.
Once the tunnel is created, you'll receive a unique tunnel ID that can be used to access the device.
Step 3: Accessing Devices
Accessing devices through a secure tunnel involves using the AWS IoT Device Management CLI or SDK to establish a connection. Follow these steps:
- Install the AWS IoT Device Management CLI or SDK on your local machine.
- Use the tunnel ID to establish a connection to the device.
- Perform the necessary tasks, such as diagnostics or firmware updates, through the secure tunnel.
By following these steps, you can ensure that your IoT devices remain securely accessible from anywhere.
Security Best Practices
While secure tunneling offers numerous security benefits, it's essential to follow best practices to ensure the highest level of protection. Below are some key security best practices:
- Use Strong Authentication: Ensure that all devices and users are authenticated using strong credentials, such as multi-factor authentication (MFA).
- Encrypt Data at Rest: Encrypt sensitive data stored on your devices to protect it from unauthorized access.
- Regularly Update Firmware: Keep your devices up to date with the latest firmware updates to address any security vulnerabilities.
- Monitor Activity: Regularly monitor activity on your secure tunnels to detect any suspicious behavior or unauthorized access attempts.
- Limit Access: Restrict access to your secure tunnels to only authorized users and devices.
By following these best practices, you can ensure that your IoT devices remain secure and protected.
Common Use Cases
Secure tunneling for AWS IoT Device Management has numerous use cases across various industries. Below are some common examples:
- Remote Diagnostics: Use secure tunnels to diagnose and troubleshoot IoT devices remotely, reducing the need for on-site visits.
- Firmware Updates: Deploy firmware updates to IoT devices securely and efficiently using secure tunnels.
- Configuration Management: Manage device configurations remotely without exposing devices to public networks.
- Data Collection: Collect data from IoT devices securely using secure tunnels, ensuring that sensitive information remains protected.
These use cases demonstrate the versatility and effectiveness of secure tunneling in managing IoT devices.
Troubleshooting Tips
Like any technology, secure tunneling can encounter issues that may require troubleshooting. Below are some common issues and their solutions:
- Connection Failures: Check the device's network connection and ensure that all necessary certificates and policies are correctly configured.
- Authentication Errors: Verify that all credentials and permissions are correctly set up and that MFA is enabled where required.
- Performance Issues: Monitor the device's performance and ensure that it meets the minimum requirements for secure tunneling.
- Security Alerts: Investigate any security alerts or warnings and take appropriate action to address potential threats.
By addressing these issues promptly, you can ensure that your secure tunnels remain functional and secure.
Comparison with Other Methods
While secure tunneling is a powerful tool for managing IoT devices, it's important to compare it with other methods to determine the best approach for your needs. Below is a comparison of secure tunneling with other methods:
- Public Network Exposure: Unlike methods that expose devices to public networks, secure tunneling ensures that devices remain protected while still allowing remote access.
- VPNs: While VPNs can provide secure access, they often require complex configurations and may not scale as easily as secure tunneling.
- Direct Connections: Direct connections may be faster, but they lack the security and flexibility of secure tunneling.
Secure tunneling offers a balanced approach to remote device management, combining security, simplicity, and scalability.
Future of Secure Tunneling
As IoT technology continues to evolve, secure tunneling is expected to play an increasingly important role in device management. Advances in encryption, authentication, and network protocols will enhance the security and efficiency of secure tunneling, making it even more valuable for businesses.
Additionally, the integration of AI and machine learning into IoT ecosystems may further enhance the capabilities of secure tunneling, enabling more intelligent and automated device management. As businesses continue to adopt IoT solutions, secure tunneling will remain a crucial component of their security strategies.
Conclusion
In conclusion, secure tunneling for AWS IoT Device Management offers a powerful solution for managing IoT devices securely and efficiently. By following the steps outlined in this article, you can implement secure tunneling effectively and ensure that your IoT ecosystem remains protected.
We encourage you to explore the resources and tools provided by AWS IoT Device Management to deepen your understanding of secure tunneling. Don't forget to leave a comment or share this article with others who may find it useful. For more information on IoT security and management, be sure to check out our other articles on the topic.
Sources:
- AWS IoT Device Management Documentation
- Transport Layer Security (TLS) Standards
- Best Practices for IoT Security

Securing IoT Devices AWS IoT Device Defender AWS

Introducing Secure Tunneling for AWS IoT Device Management, a new
Monitoring IoT Devices AWS IoT Device Management AWS