How Do I Secure My Raspberry Pi On My Network?
Securing your Raspberry Pi on your network is crucial to prevent unauthorized access and potential cyberattacks. As more devices become connected, the importance of network security cannot be overstated. By implementing the right strategies, you can protect your Raspberry Pi and ensure its safe operation.
Raspberry Pi has become one of the most popular single-board computers worldwide, thanks to its versatility and affordability. However, this affordability and flexibility also make it a target for hackers who may exploit vulnerabilities. Understanding how to secure your Raspberry Pi is essential for maintaining the integrity of your network.
This guide will walk you through the steps to secure your Raspberry Pi, covering everything from basic configurations to advanced security measures. Whether you're a beginner or an experienced user, this article will provide you with actionable insights to enhance your Raspberry Pi's security on your network.
Table of Contents
- Understanding Raspberry Pi
- Initial Setup for Security
- Password Management
- Firewall Configuration
- Securing SSH
- Network Configuration
- Software Updates
- Data Protection
- Monitoring and Logging
- Advanced Security Measures
- Conclusion
Understanding Raspberry Pi
Raspberry Pi Overview
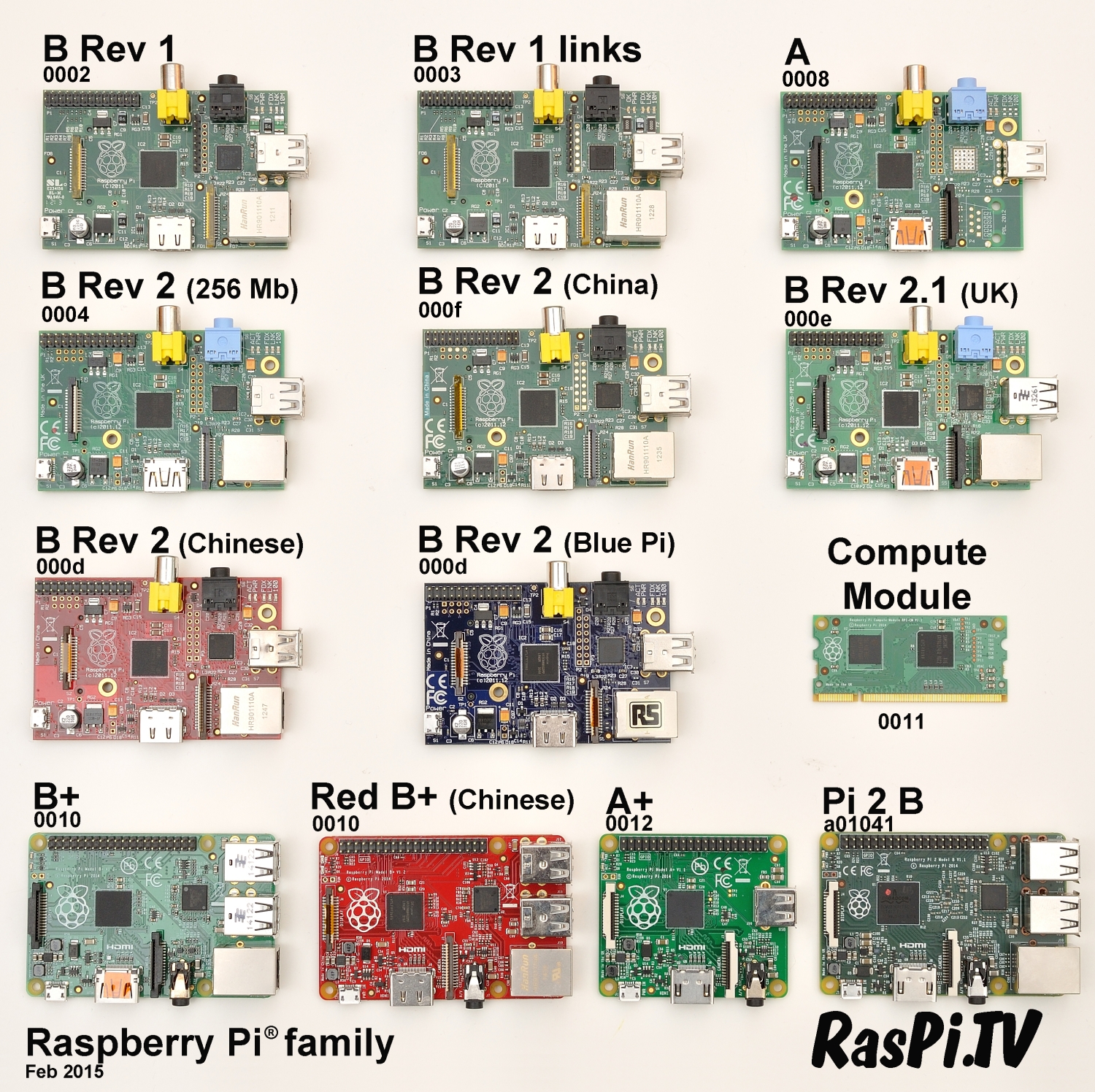
Raspberry Pi is a series of small single-board computers developed by the Raspberry Pi Foundation. Initially created to promote basic computer science education, it has since become a versatile tool for hobbyists, developers, and professionals alike. The device runs on Linux-based operating systems, making it highly customizable and open to a wide range of applications.
Despite its small size and low cost, Raspberry Pi can perform tasks ranging from media streaming to home automation. However, its open nature also means it can be vulnerable to attacks if not properly secured.
Initial Setup for Security
Securing Your Raspberry Pi from the Start
Before diving into advanced security measures, it's important to establish a secure foundation during the initial setup. Here are some key steps:
- Change Default Credentials: Replace the default username and password with strong, unique credentials.
- Disable Root Login: Avoid using the root account for regular tasks and disable root login to reduce risks.
- Set Up a Static IP Address: Assign a static IP address to your Raspberry Pi for easier management and monitoring.
These steps ensure that your Raspberry Pi is not exposed to unnecessary risks from the very beginning.
Password Management
Creating Strong Passwords
Passwords are the first line of defense against unauthorized access. To secure your Raspberry Pi, follow these best practices:
- Use Complex Passwords: Include a mix of uppercase and lowercase letters, numbers, and special characters.
- Avoid Common Words: Stay away from easily guessable passwords like "password" or "123456."
- Regularly Update Passwords: Change your passwords periodically to maintain security.
Implementing strong password management practices is essential for protecting your Raspberry Pi and your network.
Firewall Configuration
Using UFW for Enhanced Security
A firewall is a critical component of network security. The Uncomplicated Firewall (UFW) is a user-friendly tool for managing firewall rules on your Raspberry Pi. Here's how to set it up:
- Install UFW: Use the command `sudo apt install ufw` to install UFW on your Raspberry Pi.
- Set Default Rules: Configure default rules to deny all incoming connections and allow all outgoing connections.
- Allow Necessary Ports: Open only the ports required for your specific applications.
By properly configuring the firewall, you can significantly reduce the risk of unauthorized access to your Raspberry Pi.
Securing SSH
Protecting Remote Access
Secure Shell (SSH) is commonly used for remote access to Raspberry Pi. However, it can also be a vulnerability if not properly secured. Follow these steps to enhance SSH security:
- Disable Password Authentication: Use SSH keys instead of passwords for authentication.
- Change the Default Port: Alter the default SSH port (22) to a non-standard port to deter automated attacks.
- Limit User Access: Restrict SSH access to specific users or groups.
By securing SSH, you can ensure that only authorized users can access your Raspberry Pi remotely.
Network Configuration
Optimizing Network Settings
Proper network configuration is vital for securing your Raspberry Pi. Consider the following tips:
- Use a Private Network: Place your Raspberry Pi on a private network segment to isolate it from other devices.
- Enable Network Encryption: Use WPA3 encryption for Wi-Fi connections to enhance security.
- Monitor Network Traffic: Regularly review network activity to detect any suspicious behavior.
Optimizing your network settings can help protect your Raspberry Pi from external threats.
Software Updates
Keeping Your System Up-to-Date
Regular software updates are crucial for maintaining the security of your Raspberry Pi. Outdated software can contain vulnerabilities that hackers may exploit. Follow these guidelines:
- Enable Automatic Updates: Configure your system to automatically install security updates.
- Regularly Check for Updates: Manually check for updates periodically to ensure your system is fully patched.
- Remove Unused Software: Eliminate unnecessary software to reduce potential attack vectors.
Staying current with software updates is one of the most effective ways to secure your Raspberry Pi.
Data Protection
Encrypting and Backing Up Data
Protecting your data is essential to prevent loss or unauthorized access. Here are some strategies:
- Enable Disk Encryption: Use tools like LUKS to encrypt your Raspberry Pi's storage.
- Set Up Regular Backups: Schedule automatic backups to an external drive or cloud storage.
- Restrict File Permissions: Limit access to sensitive files and directories.
By implementing data protection measures, you can safeguard your information and ensure business continuity.
Monitoring and Logging
Tracking System Activity
Monitoring and logging system activity can help you detect and respond to potential security threats. Consider the following:
- Enable System Logging: Configure your Raspberry Pi to log important events and errors.
- Use Intrusion Detection Systems: Implement tools like fail2ban to monitor and block suspicious login attempts.
- Regularly Review Logs: Analyze logs to identify any unusual patterns or activities.
Proactive monitoring allows you to address security issues before they escalate.
Advanced Security Measures
Taking Security to the Next Level
For those seeking additional protection, consider these advanced security measures:
- Use a Hardware Security Module (HSM): Employ an HSM for secure key storage and cryptographic operations.
- Implement Multi-Factor Authentication (MFA): Require multiple forms of verification for accessing your Raspberry Pi.
- Regularly Conduct Security Audits: Perform periodic assessments to identify and address vulnerabilities.
By adopting advanced security measures, you can fortify your Raspberry Pi against sophisticated cyber threats.
Conclusion
Securing your Raspberry Pi on your network is a multifaceted process that requires attention to detail and a proactive approach. From initial setup to advanced security measures, each step plays a critical role in protecting your device and your network. By following the guidelines outlined in this article, you can significantly enhance the security of your Raspberry Pi.
We encourage you to take action by implementing these strategies and sharing your experiences with others. If you found this article helpful, please consider leaving a comment or exploring other resources on our site. Together, we can build a safer digital environment for everyone.

Getting started with the Camera Module Introduction Raspberry Pi
B+ or 2B? Raspberry Pi Forums

Raspberry pi 4 routeros