Is SSH On Raspberry Pi Secure? A Comprehensive Guide To Secure Your Raspberry Pi Via SSH
SSH (Secure Shell) is a protocol widely used for remote access and secure communication between devices, including the Raspberry Pi. Many users wonder whether SSH on Raspberry Pi is secure enough for their needs. This article will delve into this question, providing you with a detailed understanding of SSH security on Raspberry Pi and offering actionable tips to enhance your setup.
Whether you're a beginner or an advanced user, securing your Raspberry Pi is crucial, especially if it’s connected to the internet. With SSH, you can remotely manage your device, but it also introduces potential vulnerabilities if not properly configured.
In this guide, we’ll explore the security aspects of SSH on Raspberry Pi, discuss common threats, and provide practical solutions to ensure your device remains secure. Let’s dive in!
Table of Contents
- Introduction to SSH on Raspberry Pi
- How Does SSH Work on Raspberry Pi?
- Is SSH Secure on Raspberry Pi?
- Common SSH Security Threats
- How to Secure SSH on Raspberry Pi
- Best Practices for Using SSH on Raspberry Pi
- Alternatives to SSH for Raspberry Pi
- Troubleshooting SSH Issues on Raspberry Pi
- FAQ About SSH on Raspberry Pi
- Conclusion
Introduction to SSH on Raspberry Pi
SSH, short for Secure Shell, is a cryptographic network protocol designed for secure communication over unsecured networks. On the Raspberry Pi, SSH allows users to access their device remotely, facilitating tasks such as file transfers, system administration, and software updates.
By default, SSH is disabled on newer versions of Raspberry Pi OS to enhance security. Users must enable it manually, which provides an initial layer of protection against unauthorized access. However, enabling SSH without proper configuration can expose your device to potential threats.
Understanding the basics of SSH is essential for ensuring the security of your Raspberry Pi. This section will explore how SSH works, its benefits, and why it’s a popular choice for remote access.
How Does SSH Work on Raspberry Pi?
Understanding the SSH Protocol
SSH operates on a client-server model, where the client initiates a connection to the server. In the context of Raspberry Pi, the Pi acts as the server, while your computer or another device serves as the client.
- Encryption: SSH encrypts all data transmitted between the client and server, ensuring confidentiality and integrity.
- Authentication: Users must authenticate themselves before gaining access, typically through passwords or public key authentication.
- Port Number: SSH typically uses port 22 for communication, although this can be changed for added security.
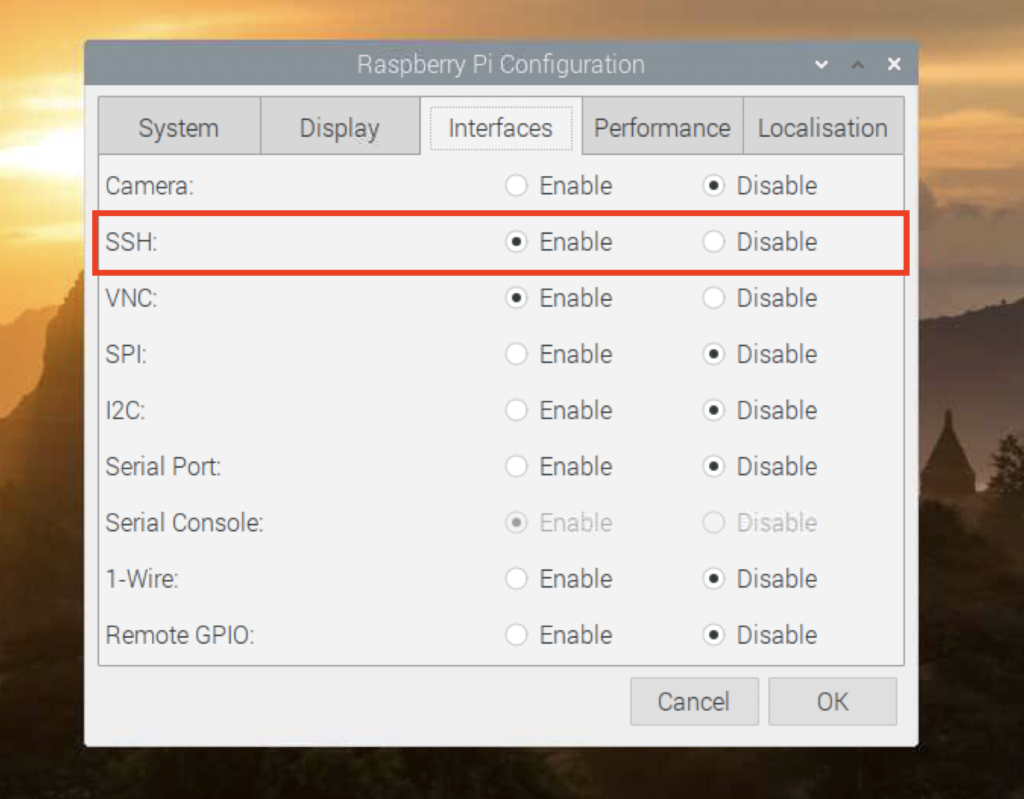
Enabling SSH on Raspberry Pi
To enable SSH on your Raspberry Pi, follow these steps:
- Access the Raspberry Pi Configuration tool by typing
sudo raspi-configin the terminal. - Select the "Interfacing Options" menu.
- Enable SSH and confirm your choice.
Alternatively, you can enable SSH by creating an empty file named "ssh" on the boot partition of your Raspberry Pi SD card.
Is SSH Secure on Raspberry Pi?
SSH is generally considered secure when properly configured. However, the security of SSH on your Raspberry Pi depends on several factors, including:
- Strong Passwords: Weak passwords can make your device vulnerable to brute-force attacks.
- Public Key Authentication: Using key-based authentication instead of passwords enhances security.
- Firewall Configuration: Restricting access to SSH through firewalls can prevent unauthorized access attempts.
While SSH provides encryption and secure communication, neglecting these security measures can expose your Raspberry Pi to risks.
Common SSH Security Threats
Brute-Force Attacks
Brute-force attacks involve automated attempts to guess your SSH login credentials. Attackers use scripts to try numerous combinations of usernames and passwords until they succeed.
Man-in-the-Middle Attacks
In a man-in-the-middle attack, an attacker intercepts and alters communication between the client and server. While SSH encrypts data, using outdated or compromised keys can still pose a risk.
Unauthorized Access
Leaving SSH open to the public internet without proper security measures can allow unauthorized users to access your Raspberry Pi, potentially leading to data breaches or system compromise.
How to Secure SSH on Raspberry Pi
1. Disable Root Login
Disabling root login prevents attackers from gaining full administrative access to your Raspberry Pi. To disable root login, edit the SSH configuration file:
- Open the file using
sudo nano /etc/ssh/sshd_config. - Set
PermitRootLogin no. - Restart the SSH service using
sudo systemctl restart ssh.
2. Use Strong Passwords
Strong passwords are crucial for SSH security. Avoid using easily guessable passwords and consider using a password manager to generate and store complex passwords.
3. Enable Public Key Authentication
Public key authentication is a more secure alternative to password-based authentication. Follow these steps to set it up:
- Generate a key pair on your client machine using
ssh-keygen. - Copy the public key to your Raspberry Pi using
ssh-copy-id user@raspberrypi. - Disable password authentication in the SSH configuration file.
Best Practices for Using SSH on Raspberry Pi
Regularly Update Your Raspberry Pi
Keeping your Raspberry Pi OS and SSH software up to date ensures you have the latest security patches and features. Use the following commands to update your system:
sudo apt updatesudo apt upgrade
Limit SSH Access
Restrict SSH access to specific IP addresses or networks using a firewall. For example, you can configure ufw to allow SSH connections only from trusted IPs:
sudo ufw allow from [trusted-ip] to any port 22
Alternatives to SSH for Raspberry Pi
While SSH is the most popular choice for remote access, other alternatives exist:
- VNC (Virtual Network Computing): Provides a graphical interface for remote access but is less secure than SSH.
- Web-based Interfaces: Some applications offer web-based interfaces for managing Raspberry Pi, but these should be used with caution due to potential security risks.
Troubleshooting SSH Issues on Raspberry Pi
Common SSH issues include connection timeouts, permission denied errors, and configuration problems. Here are some troubleshooting tips:
- Check SSH Service Status: Use
sudo systemctl status sshto verify if the SSH service is running. - Verify Firewall Settings: Ensure your firewall allows SSH traffic on the specified port.
- Review Logs: Examine SSH logs in
/var/log/auth.logfor error messages.
FAQ About SSH on Raspberry Pi
Q: Can I change the default SSH port?
Yes, you can change the default SSH port (22) to a custom port for added security. Edit the SSH configuration file and set Port [custom-port].
Q: Is SSH encryption strong enough?
SSH uses strong encryption algorithms, such as AES and RSA, to protect data. However, using outdated or weak keys can compromise security.
Conclusion
SSH on Raspberry Pi is a powerful tool for remote access and management, but its security depends on proper configuration and best practices. By following the tips outlined in this guide, you can significantly enhance the security of your Raspberry Pi and protect it from potential threats.
We encourage you to take action by implementing the security measures discussed and regularly reviewing your SSH setup. Don’t forget to share this article with others who may find it useful and leave your thoughts in the comments below. For more information on Raspberry Pi security, explore our other articles on the topic.
How to SSH Into Your Raspberry Pi in Under 3 Minutes
How to Enable SSH on Raspberry Pi? TechSphinx

Accessing Raspberry Pi thorugh SSH