Mastering Raspberry Pi SSH Tunnel: A Comprehensive Guide
Raspberry Pi SSH tunnel is an essential tool for anyone looking to enhance their network security and remote access capabilities. Whether you're a hobbyist or a professional, understanding how to set up and utilize this technology can significantly improve your computing experience. This article aims to provide a detailed exploration of Raspberry Pi SSH tunnel, ensuring you have the knowledge to implement it effectively.
Raspberry Pi has become a go-to device for countless projects, from home automation to server hosting. One of its most powerful features is the ability to create secure connections through SSH tunneling. This method allows users to access their Raspberry Pi remotely while maintaining the highest level of security.
As technology advances, so does the importance of securing your data and devices. By mastering Raspberry Pi SSH tunnel, you can protect sensitive information and streamline your workflow. In this guide, we'll cover everything you need to know, from the basics to advanced configurations.
Table of Contents
- Introduction to Raspberry Pi SSH Tunnel
- Understanding the Basics of SSH
- Setting Up SSH on Raspberry Pi
- Creating an SSH Tunnel
- Enhancing Security with SSH Keys
- Common Issues and Troubleshooting
- Benefits of Using Raspberry Pi SSH Tunnel
- Advanced Configurations
- Useful Tools for Managing SSH
- Conclusion and Next Steps
Introduction to Raspberry Pi SSH Tunnel
Secure Shell (SSH) is a network protocol designed to provide secure communication between devices over an unsecured network. When combined with Raspberry Pi, SSH tunneling becomes a powerful tool for remote access and data protection. By leveraging Raspberry Pi's capabilities, users can create encrypted tunnels that safeguard their data transmissions.
SSH tunneling is particularly useful for scenarios where sensitive information needs to be transmitted securely. Whether you're accessing a remote server, managing a home network, or running a web application, Raspberry Pi SSH tunnel offers a reliable solution. In this section, we'll delve deeper into the concept and its practical applications.
Understanding the importance of SSH tunneling is crucial for anyone working with Raspberry Pi. This technology ensures that your data remains protected from unauthorized access and potential cyber threats. By the end of this guide, you'll have a comprehensive understanding of how to implement and optimize SSH tunneling for your specific needs.
Understanding the Basics of SSH
Before diving into Raspberry Pi SSH tunnel, it's essential to grasp the fundamentals of SSH itself. Developed in the 1990s, SSH was designed to replace insecure protocols like Telnet and rsh. Its primary function is to encrypt data transmissions, ensuring that information remains confidential and tamper-proof.
Key Features of SSH
- Encryption: SSH encrypts all data transmitted between client and server, preventing eavesdropping and data interception.
- Authentication: It provides robust authentication mechanisms, ensuring that only authorized users can access the system.
- Integrity: SSH ensures data integrity by detecting any modifications during transmission.
These features make SSH an indispensable tool for secure communication. By understanding its core functionalities, you can better appreciate the benefits of implementing SSH tunneling on Raspberry Pi.
Setting Up SSH on Raspberry Pi
To begin using Raspberry Pi SSH tunnel, you must first enable SSH on your device. This process is straightforward and can be accomplished through the Raspberry Pi Configuration tool or by editing configuration files directly.
Steps to Enable SSH
- Open the Raspberry Pi Configuration tool from the main menu.
- Navigate to the "Interfaces" tab.
- Select "SSH" and choose "Enable."
- Reboot your Raspberry Pi to apply the changes.
Alternatively, you can enable SSH by creating an empty file named "ssh" on the boot partition of your Raspberry Pi's SD card. This method is particularly useful if you're setting up a headless Raspberry Pi without a monitor or keyboard.
Creating an SSH Tunnel
Once SSH is enabled on your Raspberry Pi, you can proceed to create an SSH tunnel. This process involves establishing a secure connection between your local machine and the Raspberry Pi, allowing you to forward traffic through the tunnel.
Basic SSH Tunnel Command
To create a basic SSH tunnel, use the following command:
ssh -L [local_port]:[destination_host]:[destination_port] [username]@[raspberry_pi_ip]
In this command:
- [local_port] is the port on your local machine.
- [destination_host] is the address of the server you want to access.
- [destination_port] is the port number of the service you want to connect to.
- [username] is your Raspberry Pi username.
- [raspberry_pi_ip] is the IP address of your Raspberry Pi.
By executing this command, you establish a secure tunnel that forwards traffic from your local machine to the specified destination through your Raspberry Pi.
Enhancing Security with SSH Keys
While passwords provide a basic level of security, using SSH keys offers a more robust and convenient method of authentication. SSH keys consist of a public key and a private key, which work together to verify your identity without requiring a password.
Generating SSH Keys
To generate SSH keys, follow these steps:
- Open a terminal on your local machine.
- Run the command: ssh-keygen -t rsa
- Follow the prompts to specify the location and passphrase for your keys.
- Copy the public key to your Raspberry Pi using the command: ssh-copy-id [username]@[raspberry_pi_ip]
By implementing SSH keys, you eliminate the need for password-based authentication, reducing the risk of brute-force attacks and unauthorized access.
Common Issues and Troubleshooting
Even with proper setup, issues may arise when working with Raspberry Pi SSH tunnel. Below are some common problems and their solutions:
- Connection Refused: Ensure that SSH is enabled on your Raspberry Pi and that the IP address and port number are correct.
- Permission Denied: Verify that your SSH keys are correctly configured and that the correct username is being used.
- Timeout Errors: Check your network connection and ensure that any firewalls or routers are not blocking the SSH port (default is 22).
By addressing these issues promptly, you can maintain a stable and secure SSH tunnel connection.
Benefits of Using Raspberry Pi SSH Tunnel
Raspberry Pi SSH tunnel offers numerous advantages for users seeking secure and efficient remote access. Some of the key benefits include:
- Enhanced Security: SSH tunneling encrypts all data transmissions, protecting sensitive information from unauthorized access.
- Remote Access: It allows users to access their Raspberry Pi from anywhere in the world, provided they have an internet connection.
- Flexibility: SSH tunnels can be configured to forward traffic for various services, such as web traffic, email, and file transfers.
These benefits make Raspberry Pi SSH tunnel an invaluable tool for both personal and professional use.
Advanced Configurations
For users looking to maximize the potential of Raspberry Pi SSH tunnel, advanced configurations can further enhance its capabilities. These include setting up dynamic port forwarding, configuring SSH tunneling for multiple services, and automating the connection process.
Dynamic Port Forwarding
Dynamic port forwarding allows you to use SSH as a SOCKS proxy, routing all traffic through the tunnel. This can be achieved with the following command:
ssh -D [local_port] [username]@[raspberry_pi_ip]
By implementing advanced configurations, you can tailor the SSH tunnel to meet your specific needs and optimize its performance.
Useful Tools for Managing SSH
Several tools are available to simplify the management of SSH connections on Raspberry Pi. Some popular options include:
- Putty: A widely used SSH client for Windows users, offering a user-friendly interface for managing connections.
- SSHFS: Allows you to mount remote file systems over SSH, providing seamless access to your Raspberry Pi's files.
- Keychain: A utility for managing SSH keys, ensuring they remain secure while simplifying the authentication process.
Utilizing these tools can streamline your workflow and enhance your experience with Raspberry Pi SSH tunnel.
Conclusion and Next Steps
In conclusion, Raspberry Pi SSH tunnel is a powerful tool for securing your data and enabling remote access. By following the steps outlined in this guide, you can implement and optimize SSH tunneling to meet your specific requirements. Whether you're a beginner or an experienced user, mastering this technology can significantly enhance your computing capabilities.
We encourage you to take the next steps by experimenting with advanced configurations and exploring the various tools available for managing SSH connections. Additionally, feel free to share your thoughts and experiences in the comments section below. Don't forget to explore other articles on our site for more insightful content related to Raspberry Pi and network security.
How to access Raspberry Pi SSH sessions over the PiTunnel
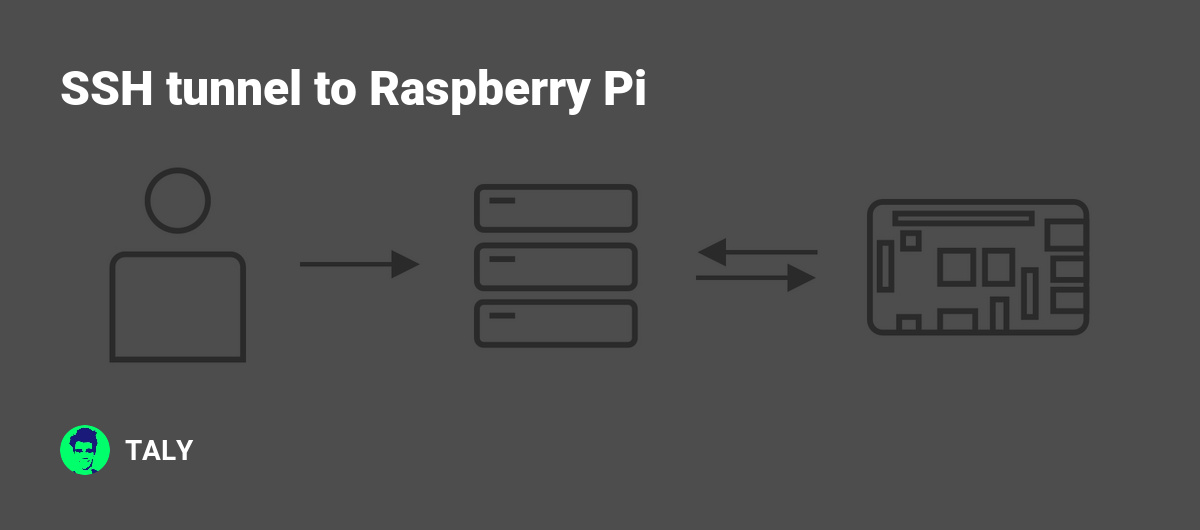
SSH tunnel to Raspberry Pi

How to Connect via SSH to a Raspberry Pi Tony Teaches Tech