How To Remote Connect Raspberry Pi Behind Firewall Without Issues
Connecting to a Raspberry Pi remotely from behind a firewall can seem daunting, especially for beginners. However, with the right tools and techniques, it becomes an achievable task. Whether you're a tech enthusiast or a professional IT administrator, this guide will provide step-by-step instructions to help you set up a secure and reliable remote connection.
As more people work and manage systems remotely, the ability to access devices like Raspberry Pi without being physically present is essential. This is where remote connectivity plays a critical role. However, firewalls often pose challenges by blocking unauthorized access, making it necessary to explore alternative methods.
In this article, we'll explore how to remote connect Raspberry Pi behind a firewall without complications. We'll cover everything from setting up the necessary software to configuring firewalls and utilizing secure connection methods. Let’s dive in!
Table of Contents
- Introduction to Raspberry Pi
- Understanding Firewalls
- How to Remote Connect Raspberry Pi
- Setting Up SSH for Raspberry Pi
- Configuring Port Forwarding
- Using Secure Remote Access Tools
- Alternatives to Port Forwarding
- Troubleshooting Common Issues
- Best Practices for Security
- Conclusion and Next Steps
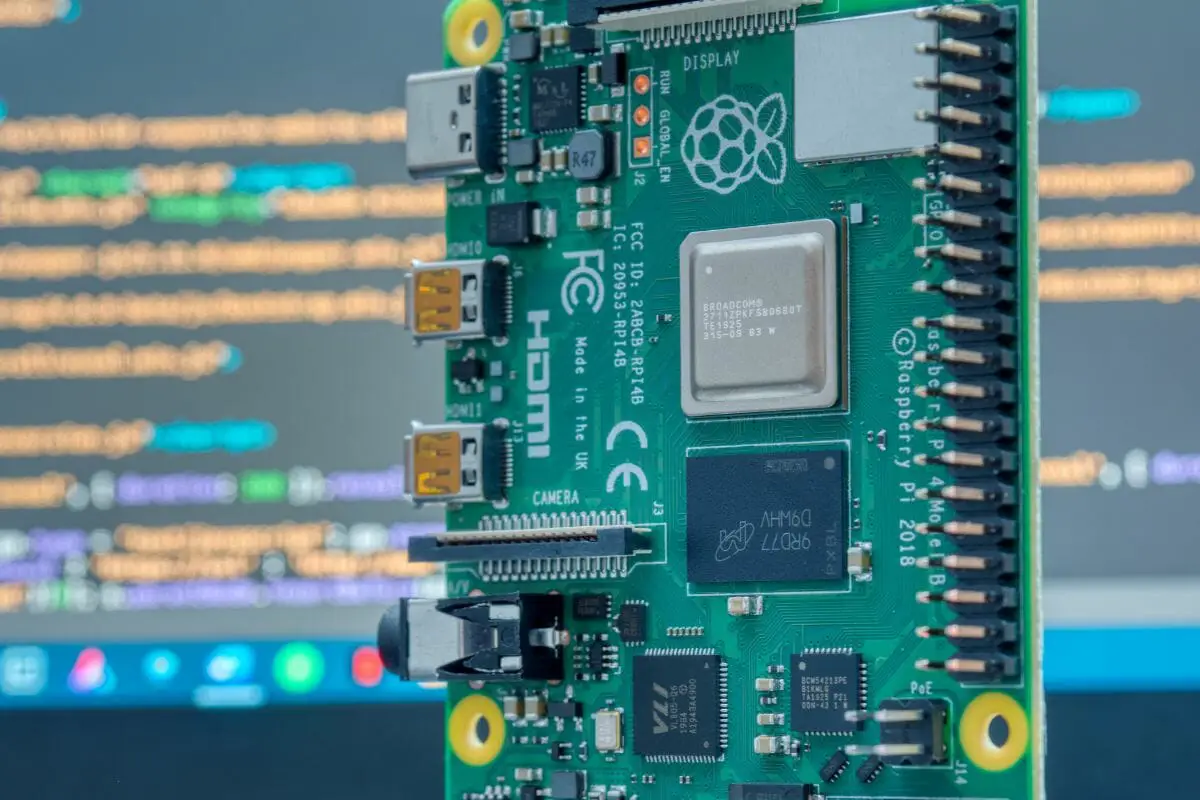
Introduction to Raspberry Pi
The Raspberry Pi is a compact, affordable single-board computer that has gained immense popularity among hobbyists, educators, and professionals alike. Its versatility allows it to be used for a wide range of applications, from home automation to server hosting. However, one common challenge users face is accessing their Raspberry Pi remotely when it's behind a firewall.
Firewalls are designed to protect networks by blocking unauthorized access. While this is beneficial for security, it can complicate remote access to devices like Raspberry Pi. Therefore, understanding how to bypass these restrictions securely is crucial.
Why Use Raspberry Pi for Remote Connections?
- Cost-effective solution for hosting servers and applications.
- Highly customizable and compatible with various operating systems.
- Energy-efficient and compact design for remote management.
Understanding Firewalls
A firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. It acts as a barrier between trusted internal networks and untrusted external networks, such as the internet. Firewalls are essential for protecting devices from malicious attacks and unauthorized access.
- What Happened Toarah Goldberg American Idol
- Zac Brown Weight Loss F1
- Richard Egan Actor
- Actor Jeremy Allen White
When you attempt to remote connect Raspberry Pi behind a firewall, the firewall may block the connection request unless specific rules are configured to allow it. Understanding how firewalls work is the first step in overcoming these challenges.
Types of Firewalls
- Packet Filtering Firewalls: Analyze individual packets of data and decide whether to allow or block them.
- Stateful Inspection Firewalls: Monitor active connections and make decisions based on context.
- Application-Level Gateways: Act as intermediaries between internal and external networks.
How to Remote Connect Raspberry Pi Behind Firewall Without Issues
Connecting to your Raspberry Pi remotely involves several steps, including configuring the device, setting up the network, and ensuring security. Below, we outline the key processes involved in achieving a seamless connection.
One of the most common methods for remote access is using SSH (Secure Shell). SSH allows you to securely log into another computer over a network, execute commands, and transfer files. However, when your Raspberry Pi is behind a firewall, additional configurations may be required.
Steps to Remote Connect Raspberry Pi
- Ensure SSH is enabled on your Raspberry Pi.
- Identify your Raspberry Pi's local IP address.
- Configure port forwarding on your router.
- Use a dynamic DNS service if your IP address changes frequently.
- Test the connection from a remote location.
Setting Up SSH for Raspberry Pi
SSH is a network protocol that provides secure communication between two systems. To enable SSH on your Raspberry Pi, follow these steps:
- Power on your Raspberry Pi and log in.
- Open the terminal and type
sudo raspi-config. - Navigate to
Interfacing Optionsand selectSSH. - Choose
Yesto enable SSH and then reboot your Raspberry Pi.
Once SSH is enabled, you can connect to your Raspberry Pi using an SSH client like PuTTY (for Windows) or the built-in terminal on macOS and Linux.
Securing Your SSH Connection
- Change the default SSH port (usually 22) to a non-standard port.
- Disable password-based authentication and use SSH keys instead.
- Limit access to specific IP addresses using firewall rules.
Configuring Port Forwarding
Port forwarding allows you to direct incoming traffic from the internet to a specific device on your local network. To configure port forwarding for your Raspberry Pi:
- Log in to your router's admin interface using its IP address.
- Navigate to the port forwarding or virtual server settings.
- Add a new rule, specifying the external port (e.g., 2222) and the internal IP address of your Raspberry Pi.
- Save the changes and restart your router if necessary.
Port forwarding is a straightforward way to access your Raspberry Pi remotely, but it requires careful configuration to ensure security.
Best Practices for Port Forwarding
- Use non-standard ports to reduce the risk of automated attacks.
- Regularly update your router's firmware to patch vulnerabilities.
- Monitor your network for suspicious activity.
Using Secure Remote Access Tools
While port forwarding is a common method, there are alternative tools that provide secure remote access to your Raspberry Pi. Some popular options include:
1. TunnelBear
TunnelBear is a user-friendly VPN service that allows you to create secure tunnels for remote access. By setting up a tunnel, you can bypass firewall restrictions and connect to your Raspberry Pi from anywhere.
2. ngrok
ngrok is a lightweight tool that creates secure tunnels to localhost. It's particularly useful for developers who need to test and debug applications remotely. Simply install ngrok on your Raspberry Pi and run the command ngrok tcp 22 to expose your SSH port.
Alternatives to Port Forwarding
If you prefer not to use port forwarding, there are several alternative methods for remote connecting Raspberry Pi behind a firewall:
1. Dynamic DNS (DDNS)
Dynamic DNS services automatically update your domain name with your current IP address, making it easier to connect to your Raspberry Pi even if your IP changes. Popular DDNS providers include No-IP and DuckDNS.
2. Reverse SSH Tunnel
A reverse SSH tunnel allows you to initiate a connection from your Raspberry Pi to a remote server, effectively bypassing firewall restrictions. This method is ideal for situations where you have limited control over the network configuration.
Troubleshooting Common Issues
Even with careful planning, issues can arise when trying to remote connect Raspberry Pi behind a firewall. Below are some common problems and their solutions:
1. Connection Timeout
- Ensure your Raspberry Pi's IP address is correct.
- Verify that port forwarding is properly configured on your router.
- Check for any firewall rules blocking the connection.
2. Authentication Failure
- Double-check your SSH credentials.
- Ensure SSH keys are correctly configured if using key-based authentication.
- Disable any conflicting authentication methods.
Best Practices for Security
Security should always be a top priority when setting up remote access to your Raspberry Pi. Follow these best practices to protect your device:
- Use strong, unique passwords for all accounts.
- Regularly update your Raspberry Pi's operating system and software.
- Limit access to trusted IP addresses using firewall rules.
- Monitor logs for any suspicious activity.
Conclusion and Next Steps
Remote connecting Raspberry Pi behind a firewall without issues is achievable with the right tools and techniques. By following the steps outlined in this article, you can securely access your Raspberry Pi from anywhere in the world. Remember to prioritize security and regularly update your configurations to protect against potential threats.
We encourage you to experiment with different methods and tools to find the one that best suits your needs. If you have any questions or feedback, feel free to leave a comment below. Additionally, don't forget to explore other articles on our site for more insightful guides and tutorials.
References:
Raspberry Pi Connect Raspberry Pi
How To Install And Manage The Raspberry Pi Firewall? Revised 2025
How To Install And Manage The Raspberry Pi Firewall? Revised 2025