Secure Tunneling For AWS IoT Device Management: Enhancing Connectivity And Security
As the Internet of Things (IoT) continues to expand, the demand for secure and reliable communication between devices has never been higher. Secure tunneling for AWS IoT Device Management plays a critical role in ensuring seamless and encrypted connectivity. This technology allows users to manage IoT devices securely, even when they are behind firewalls or NATs, making it indispensable for modern IoT applications.
In today's interconnected world, IoT devices generate massive amounts of data that need to be transmitted securely. Without proper security measures, sensitive information could be vulnerable to cyberattacks. AWS IoT Device Management offers a robust solution by integrating secure tunneling capabilities, enabling remote access to devices while maintaining high levels of security.
This article will explore the concept of secure tunneling for AWS IoT Device Management in-depth, covering its benefits, implementation, best practices, and real-world applications. By the end of this guide, you will have a comprehensive understanding of how secure tunneling enhances IoT device management and why it is essential for businesses operating in the IoT landscape.
Table of Contents
- Introduction to Secure Tunneling for AWS IoT Device Management
- What is Secure Tunneling?
- Understanding AWS IoT Device Management
- Benefits of Secure Tunneling in AWS IoT
- How to Implement Secure Tunneling in AWS IoT
- Key Security Features of Secure Tunneling
- Best Practices for Secure Tunneling
- Real-World Applications of Secure Tunneling
- Troubleshooting Common Issues
- Future Trends in Secure Tunneling
- Conclusion
Introduction to Secure Tunneling for AWS IoT Device Management
Secure tunneling for AWS IoT Device Management is a cutting-edge technology designed to facilitate secure and reliable communication between IoT devices and cloud services. This technology enables remote access to IoT devices without compromising security, making it ideal for industries that require high levels of data protection. By leveraging secure tunneling, organizations can ensure that their IoT infrastructure remains protected from unauthorized access and cyber threats.
AWS IoT Device Management provides a suite of tools and features that simplify the process of managing IoT devices at scale. Secure tunneling is one of the key components of this platform, allowing users to establish encrypted connections with devices located behind firewalls or NATs. This capability is particularly valuable for organizations that need to monitor and control IoT devices remotely, ensuring that they remain operational and secure.
What is Secure Tunneling?
Secure tunneling refers to the process of creating an encrypted connection between two endpoints, typically a client and a server, to facilitate secure communication. In the context of AWS IoT Device Management, secure tunneling enables users to access IoT devices remotely while maintaining the integrity and confidentiality of the data being transmitted.
How Does Secure Tunneling Work?
Secure tunneling works by encapsulating data packets within an encrypted channel, ensuring that they cannot be intercepted or tampered with during transmission. This process involves the use of cryptographic protocols such as TLS (Transport Layer Security) to establish a secure connection between the client and server.
Key components of secure tunneling include:
- Encryption: Data is encrypted before being transmitted over the network, ensuring that it remains confidential.
- Authentication: Both endpoints are authenticated to verify their identities and prevent unauthorized access.
- Integrity: Cryptographic techniques are used to ensure that the data has not been altered during transmission.
Understanding AWS IoT Device Management
AWS IoT Device Management is a fully managed service that simplifies the process of managing IoT devices at scale. This platform provides a range of features designed to streamline device provisioning, monitoring, and maintenance, making it easier for organizations to deploy and manage IoT solutions.
Features of AWS IoT Device Management
AWS IoT Device Management offers several features that make it an ideal choice for organizations looking to manage IoT devices effectively. These include:
- Device Provisioning: Automate the process of onboarding new devices to the IoT infrastructure.
- Device Monitoring: Monitor device performance and health in real-time, enabling proactive maintenance.
- Secure Communication: Ensure secure communication between devices and the cloud using secure tunneling.
Benefits of Secure Tunneling in AWS IoT
Secure tunneling for AWS IoT Device Management offers numerous benefits that make it an essential component of modern IoT solutions. These benefits include:
Enhanced Security
Secure tunneling ensures that all communication between IoT devices and the cloud is encrypted, protecting sensitive data from unauthorized access and cyber threats.
Remote Access
By enabling remote access to IoT devices, secure tunneling simplifies the process of managing and maintaining devices located in remote or hard-to-reach locations.
Scalability
AWS IoT Device Management, combined with secure tunneling, allows organizations to manage IoT devices at scale, accommodating the growing demand for IoT solutions.
How to Implement Secure Tunneling in AWS IoT
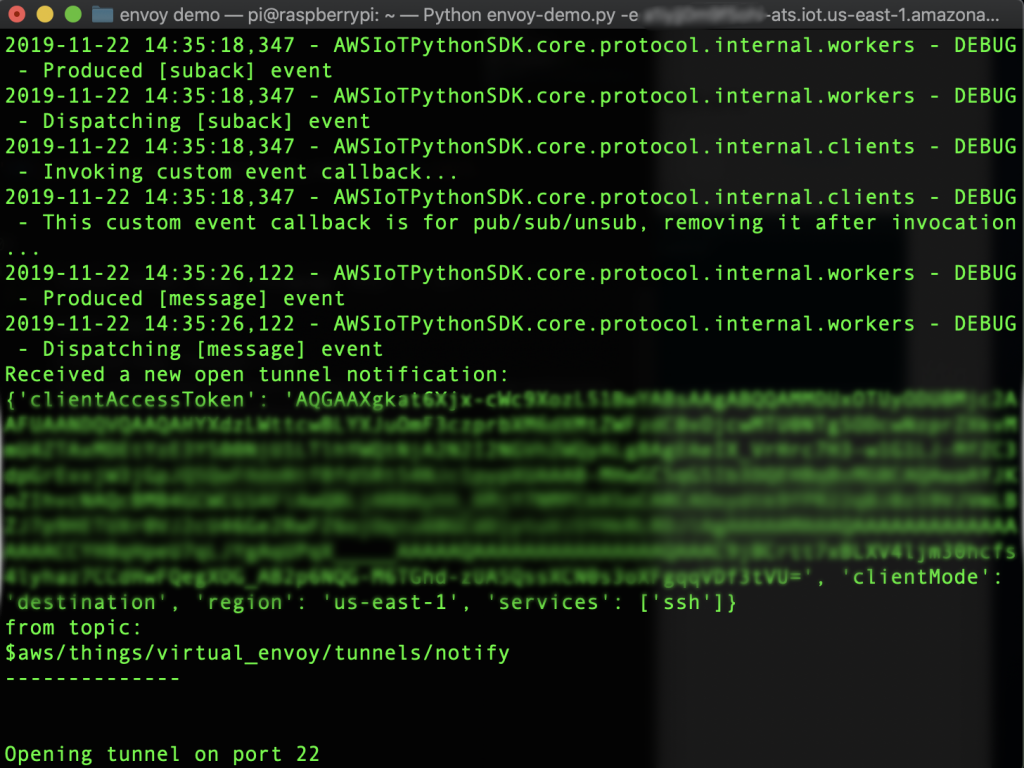
Implementing secure tunneling in AWS IoT Device Management involves several steps, including setting up the necessary infrastructure, configuring devices, and establishing secure connections. Below is a step-by-step guide to help you get started:
Step 1: Set Up AWS IoT Core
Begin by setting up AWS IoT Core, the foundational service for AWS IoT Device Management. This involves creating an AWS account, configuring IAM roles, and setting up policies to control access to IoT resources.
Step 2: Configure Devices
Next, configure your IoT devices to communicate with AWS IoT Core. This includes installing the necessary software, generating certificates, and configuring network settings.
Step 3: Establish Secure Connections
Finally, establish secure connections between devices and the cloud using secure tunneling. This involves configuring the secure tunneling service and testing the connection to ensure it is functioning correctly.
Key Security Features of Secure Tunneling
Secure tunneling for AWS IoT Device Management includes several key security features that ensure the protection of IoT devices and data. These features include:
Encryption
Data transmitted through secure tunneling is encrypted using industry-standard cryptographic protocols, ensuring that it remains confidential and secure.
Authentication
Both endpoints in a secure tunnel are authenticated using certificates, preventing unauthorized access and ensuring that only trusted devices can communicate with the cloud.
Access Control
AWS IoT Device Management provides fine-grained access control, allowing organizations to define who can access specific devices and resources.
Best Practices for Secure Tunneling
To ensure the successful implementation of secure tunneling in AWS IoT Device Management, it is essential to follow best practices. These include:
Use Strong Passwords and Certificates
Ensure that all devices and users are authenticated using strong passwords and certificates to prevent unauthorized access.
Regularly Update Software and Firmware
Keep all devices and software up to date to address security vulnerabilities and ensure optimal performance.
Monitor and Audit Connections
Regularly monitor and audit secure tunnel connections to identify and address any potential security issues.
Real-World Applications of Secure Tunneling
Secure tunneling for AWS IoT Device Management has numerous real-world applications across various industries. Some examples include:
Industrial IoT
In industrial settings, secure tunneling enables remote monitoring and control of machinery, improving efficiency and reducing downtime.
Smart Cities
Secure tunneling facilitates the management of smart city infrastructure, such as traffic lights and public transportation systems, ensuring they remain operational and secure.
Healthcare
In healthcare, secure tunneling allows for the remote monitoring of medical devices, enabling healthcare providers to deliver high-quality care while maintaining patient privacy.
Troubleshooting Common Issues
While secure tunneling for AWS IoT Device Management is a robust solution, issues may arise during implementation. Below are some common issues and their solutions:
Connection Issues
If you encounter connection issues, verify that all devices are properly configured and that network settings are correct. Additionally, check for any firewall or NAT restrictions that may be blocking the connection.
Authentication Failures
Authentication failures can occur if certificates or passwords are incorrect. Ensure that all credentials are valid and that devices are properly authenticated before attempting to establish a connection.
Future Trends in Secure Tunneling
As IoT technology continues to evolve, secure tunneling will play an increasingly important role in ensuring the security and reliability of IoT devices. Future trends in secure tunneling include:
Quantum-Resistant Cryptography
With the advent of quantum computing, there is a growing need for quantum-resistant cryptographic protocols to protect IoT devices and data from future threats.
Artificial Intelligence and Machine Learning
AI and machine learning will enhance secure tunneling by enabling predictive maintenance and anomaly detection, improving the overall security and performance of IoT systems.
Conclusion
Secure tunneling for AWS IoT Device Management is a vital technology that ensures the secure and reliable communication of IoT devices. By implementing secure tunneling, organizations can protect their IoT infrastructure from cyber threats, facilitate remote access to devices, and manage IoT devices at scale.
We encourage readers to explore the capabilities of secure tunneling further and consider integrating it into their IoT solutions. For more information, please leave a comment below or share this article with your network. Additionally, feel free to explore other articles on our site to learn more about AWS IoT and related technologies.

Introducing Secure Tunneling for AWS IoT Device Management, a new
Introducing Secure Tunneling for AWS IoT Device Management, a new

Introducing Secure Tunneling for AWS IoT Device Management, a new