Securely Connect Raspberry Pi: A Comprehensive Guide
Connecting your Raspberry Pi securely is essential for maintaining the integrity of your network and protecting sensitive data. Whether you're using Raspberry Pi for home automation, IoT projects, or as a server, ensuring secure connections is a top priority. This guide will walk you through everything you need to know about securely connecting your Raspberry Pi, including best practices, tools, and configurations.
In this digital age, cybersecurity threats are increasingly common, and securing your Raspberry Pi should be a fundamental part of your project setup. Understanding how to protect your device from unauthorized access and potential breaches is critical for both personal and professional use.
This article is designed for users of all skill levels, from beginners to advanced developers. We will cover various aspects of securely connecting Raspberry Pi, including setting up secure SSH connections, configuring firewalls, and implementing encryption protocols. Let's dive in and ensure your Raspberry Pi remains safe and secure.
Table of Contents
- Introduction to Raspberry Pi Security
- Setting Up Secure SSH Connections
- Configuring Firewalls for Raspberry Pi
- Implementing Encryption Protocols
- Securing Network Connections
- Regularly Updating Raspberry Pi
- Using Strong Passwords and Authentication
- Securing Wireless Connections
- Recommended Security Tools
- Troubleshooting Common Security Issues
- Conclusion and Call to Action
Introduction to Raspberry Pi Security
Raspberry Pi has become a popular choice for developers and hobbyists due to its affordability and versatility. However, with its increasing adoption, the importance of securing your Raspberry Pi cannot be overstated. A securely connected Raspberry Pi ensures that your projects remain protected from potential cyber threats.
Securing your Raspberry Pi involves multiple layers of protection, starting from physical security to advanced software configurations. By following best practices and staying informed about the latest security trends, you can minimize risks and enhance the safety of your device.
Below, we will explore key areas of focus when it comes to securing your Raspberry Pi, including SSH connections, firewalls, encryption, and more. These steps are crucial for maintaining a secure and reliable setup.
Setting Up Secure SSH Connections
Understanding SSH
SSH (Secure Shell) is a cryptographic network protocol used to securely connect to remote devices. It is one of the most important tools for managing Raspberry Pi remotely. By default, SSH is disabled on newer versions of Raspberry Pi OS, so enabling it is the first step toward secure connections.
Enabling SSH on Raspberry Pi
To enable SSH on your Raspberry Pi, follow these steps:
- Insert the SD card containing Raspberry Pi OS into your computer.
- Create an empty file named "ssh" (without any file extension) in the boot partition.
- Eject the SD card and insert it back into your Raspberry Pi.
Once SSH is enabled, you can connect to your Raspberry Pi using an SSH client like PuTTY (Windows) or the terminal (Linux/Mac).
Securing SSH Connections
While SSH is inherently secure, there are additional steps you can take to enhance its security:
- Change the default SSH port (22) to a non-standard port to reduce automated attacks.
- Disable password-based authentication and use SSH keys instead.
- Limit SSH access to specific IP addresses using firewall rules.
By implementing these measures, you can significantly reduce the risk of unauthorized access through SSH.
Configuring Firewalls for Raspberry Pi
What is a Firewall?
A firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. Configuring a firewall on your Raspberry Pi is essential for protecting it from unauthorized access.
Using UFW (Uncomplicated Firewall)
UFW is a user-friendly firewall management tool available on Raspberry Pi OS. To install and configure UFW, follow these steps:
- Install UFW by running the command:
sudo apt install ufw. - Allow specific ports, such as SSH, by running:
sudo ufw allow 22. - Enable UFW with the command:
sudo ufw enable.
UFW simplifies the process of setting up firewall rules, making it an ideal choice for beginners.
Implementing Encryption Protocols
Why Encryption Matters
Encryption is the process of converting plain text into a coded format to prevent unauthorized access. Implementing encryption protocols on your Raspberry Pi ensures that sensitive data remains protected during transmission.
Using HTTPS for Web Servers
If you're running a web server on your Raspberry Pi, enabling HTTPS is crucial. HTTPS encrypts data between the server and clients, preventing eavesdropping and data tampering. To set up HTTPS:
- Install Certbot to obtain an SSL certificate:
sudo apt install certbot python3-certbot-apache. - Run Certbot to configure HTTPS:
sudo certbot --apache.
With HTTPS enabled, your Raspberry Pi web server will provide secure connections to users.
Securing Network Connections
Understanding Network Security
Network security involves protecting the usability and integrity of your network and data. Securing network connections on your Raspberry Pi is vital, especially if it's connected to the internet.
Configuring Static IP Addresses
Using static IP addresses for your Raspberry Pi can improve security by making it easier to monitor and control network traffic. To configure a static IP:
- Edit the
/etc/dhcpcd.conffile using a text editor. - Add the following lines to assign a static IP:
interface eth0
static ip_address=192.168.1.100/24
static routers=192.168.1.1
static domain_name_servers=192.168.1.1
By assigning a static IP, you can ensure consistent network access while maintaining security.
Regularly Updating Raspberry Pi
Importance of Updates
Regularly updating your Raspberry Pi ensures that you have the latest security patches and bug fixes. Updates are critical for maintaining the stability and security of your device.
Updating Raspberry Pi OS
To update your Raspberry Pi, run the following commands:
- Update the package list:
sudo apt update. - Upgrade installed packages:
sudo apt full-upgrade. - Reboot your Raspberry Pi:
sudo reboot.
Staying up-to-date with the latest software versions is one of the easiest ways to enhance the security of your Raspberry Pi.
Using Strong Passwords and Authentication
Creating Strong Passwords
A strong password is the first line of defense against unauthorized access. When setting up your Raspberry Pi, ensure that you use a complex password that includes a mix of uppercase and lowercase letters, numbers, and symbols.
Implementing Two-Factor Authentication
Two-factor authentication (2FA) adds an extra layer of security by requiring a second form of verification in addition to a password. To implement 2FA on your Raspberry Pi:
- Install Google Authenticator:
sudo apt install libpam-google-authenticator. - Run the Google Authenticator setup:
google-authenticator. - Follow the prompts to configure 2FA.
With 2FA enabled, even if someone guesses your password, they won't be able to access your Raspberry Pi without the second factor.
Securing Wireless Connections
Understanding Wi-Fi Security
Securing wireless connections is crucial when using Raspberry Pi as a Wi-Fi client or access point. By default, Raspberry Pi uses WPA2 encryption for Wi-Fi connections, which is considered secure. However, additional measures can further enhance security.
Changing Wi-Fi Passwords Regularly
Regularly changing your Wi-Fi password prevents unauthorized access and ensures long-term security. To change your Wi-Fi password:
- Edit the
/etc/wpa_supplicant/wpa_supplicant.conffile. - Update the password in the network configuration section.
- Restart the networking service:
sudo systemctl restart networking.
By keeping your Wi-Fi password secure and up-to-date, you can protect your Raspberry Pi from potential threats.
Recommended Security Tools
Top Tools for Raspberry Pi Security
Several tools can help you secure your Raspberry Pi effectively:
- Fail2Ban: Prevents brute-force attacks by blocking IP addresses after multiple failed login attempts.
- ClamAV: A free antivirus software that detects and removes malware from your Raspberry Pi.
- Rkhunter: Scans your system for rootkits and other malicious software.
Using these tools can significantly enhance the security of your Raspberry Pi and protect it from various threats.
Troubleshooting Common Security Issues
Identifying Security Breaches
Knowing how to identify potential security breaches is essential for maintaining the integrity of your Raspberry Pi. Common signs of a breach include:
- Unusual network activity or increased bandwidth usage.
- Unexpected changes to system files or configurations.
- Unauthorized login attempts or failed authentication logs.
Steps to Take After a Breach
If you suspect a security breach, follow these steps:
- Disconnect your Raspberry Pi from the network immediately.
- Perform a full system scan using antivirus tools like ClamAV.
- Change all passwords and enable two-factor authentication.
- Review and update firewall rules to prevent future breaches.
By acting quickly and decisively, you can minimize the damage caused by a security breach and restore your Raspberry Pi to a secure state.
Conclusion and Call to Action
Securing your Raspberry Pi is a multi-faceted process that requires attention to detail and a proactive approach. By following the steps outlined in this guide, you can ensure that your device remains protected from potential threats and vulnerabilities.
Remember, cybersecurity is an ongoing effort. Stay informed about the latest security trends and regularly update your Raspberry Pi to maintain its security. We encourage you to share this article with others and leave a comment below if you have any questions or feedback.
For more information on Raspberry Pi security, explore our other articles or visit trusted resources like the official Raspberry Pi website and reputable tech blogs. Together, we can build a safer and more secure digital environment.

How to Connect the Raspberry Pi’s Port (2 ways) RaspberryTips
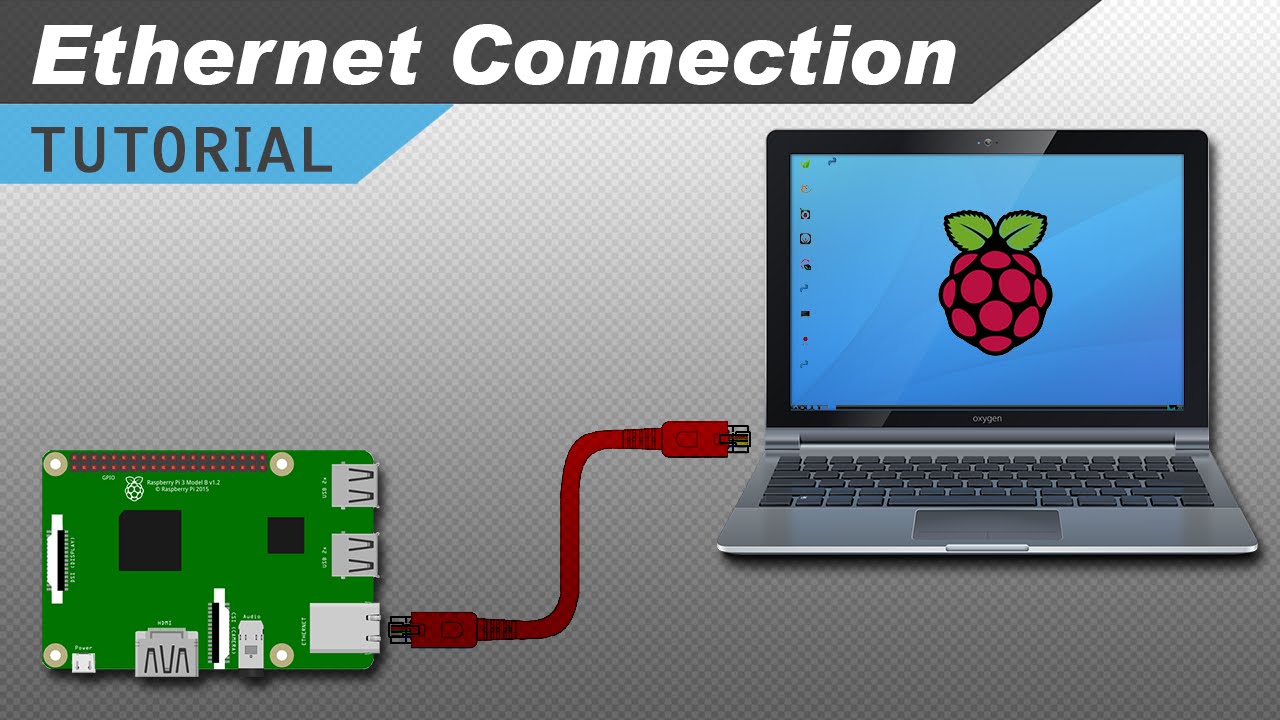
How to Connect to a Raspberry Pi with an Cable ElectronicsLab
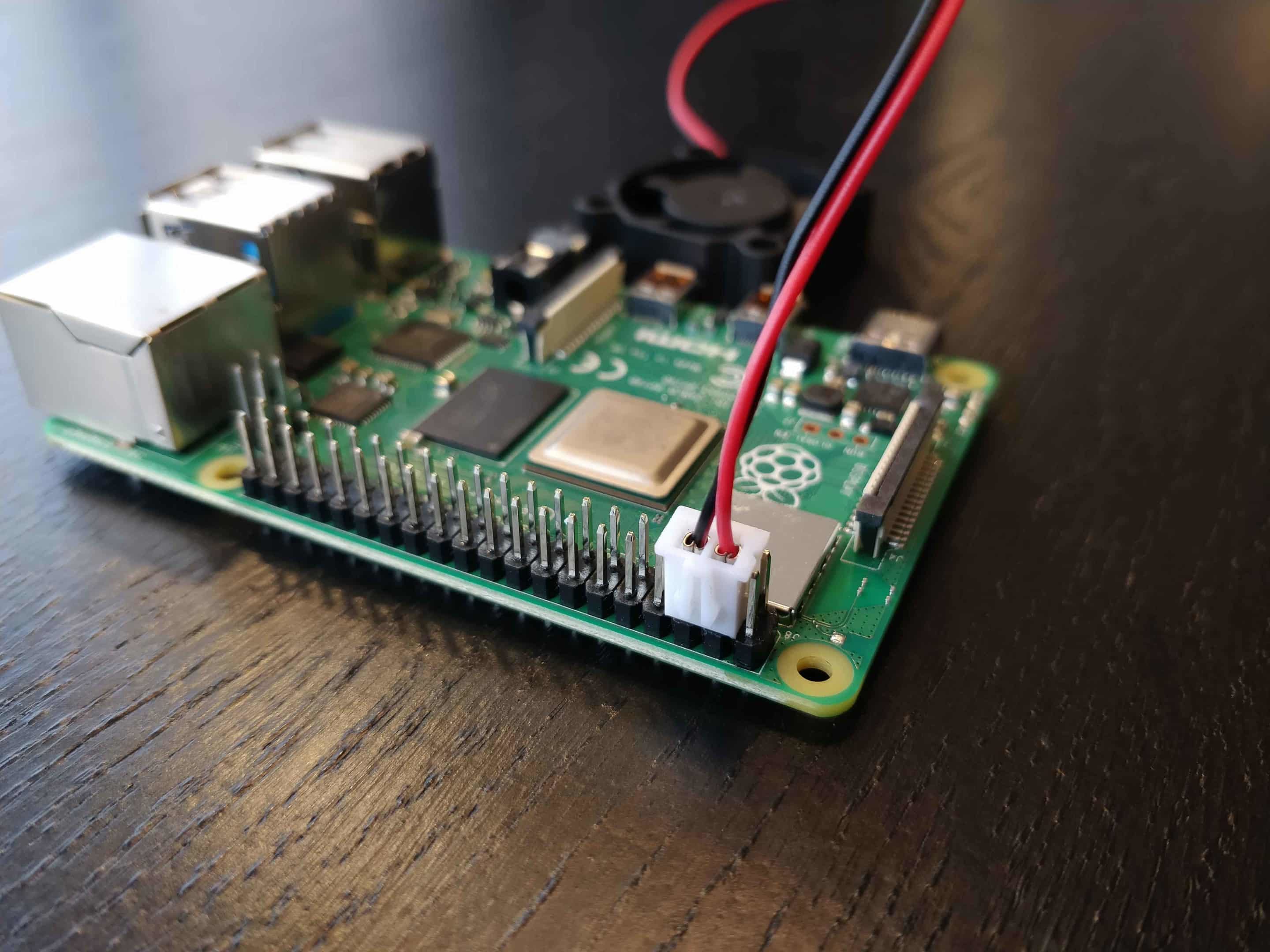
Udalosť plodný umelec raspberry pi 4 connect fan tajne vegetarián