IoT SSH Tunnel AWS: The Ultimate Guide To Secure And Scalable IoT Connections
In today's interconnected world, IoT SSH tunnel AWS has become a critical solution for secure communication between devices and cloud infrastructure. The Internet of Things (IoT) continues to expand, bringing billions of connected devices into our daily lives. However, with this growth comes the challenge of ensuring secure and reliable data transmission. This article dives deep into how SSH tunnels on AWS can be leveraged to enhance IoT security and scalability.
As IoT deployments grow in complexity, organizations are increasingly relying on cloud platforms like AWS to manage their connected ecosystems. The integration of SSH tunnels within AWS provides an additional layer of security, protecting sensitive data from unauthorized access. This article explores the technical aspects, benefits, and best practices for implementing IoT SSH tunnel solutions on AWS.
Whether you're a developer, system administrator, or IT professional, understanding the role of SSH tunnels in securing IoT communications is essential. By the end of this guide, you'll have a comprehensive understanding of how to implement and optimize IoT SSH tunnels on AWS to meet modern security standards.
Table of Contents
- Introduction to IoT SSH Tunnel AWS
- Understanding SSH Tunnel Basics
- AWS Architecture for IoT SSH Tunnels
- Security Considerations in IoT SSH Tunnel AWS
- Step-by-Step Implementation of IoT SSH Tunnel on AWS
- Performance Optimization Techniques
- Common Issues and Troubleshooting
- Real-World Applications of IoT SSH Tunnel AWS
- Future Trends in IoT SSH Tunnel AWS
- Conclusion and Call to Action
Introduction to IoT SSH Tunnel AWS
The Internet of Things (IoT) has revolutionized the way we interact with technology, enabling seamless communication between devices and systems. However, as the number of connected devices increases, so does the risk of data breaches and cyberattacks. This is where IoT SSH tunnel AWS plays a pivotal role. By leveraging Secure Shell (SSH) tunnels, organizations can establish encrypted connections between IoT devices and AWS cloud services, ensuring data integrity and confidentiality.
Why Choose AWS for IoT SSH Tunnels?
AWS offers a robust and scalable infrastructure that supports the unique requirements of IoT deployments. With features like AWS IoT Core, EC2 instances, and managed security services, AWS provides everything needed to build a secure IoT ecosystem. The integration of SSH tunnels further enhances security by encrypting data in transit, protecting it from unauthorized interception.
Additionally, AWS's global network of data centers ensures low-latency connections, making it an ideal choice for real-time IoT applications. Whether you're managing a small-scale IoT project or a large enterprise deployment, AWS provides the tools and resources needed to succeed.
Understanding SSH Tunnel Basics
Before diving into IoT SSH tunnel AWS, it's important to understand the fundamentals of SSH tunnels. An SSH tunnel is a method of securely transmitting data between two systems by encrypting it within an SSH connection. This ensures that even if the data is intercepted, it remains unreadable to unauthorized parties.
Key Features of SSH Tunnels
- End-to-end encryption
- Support for multiple protocols
- Ability to bypass firewalls
- Flexible configuration options
SSH tunnels are widely used in various industries, including healthcare, finance, and manufacturing, to secure sensitive data transmissions. When combined with AWS's IoT services, they provide a powerful solution for protecting IoT communications.
AWS Architecture for IoT SSH Tunnels
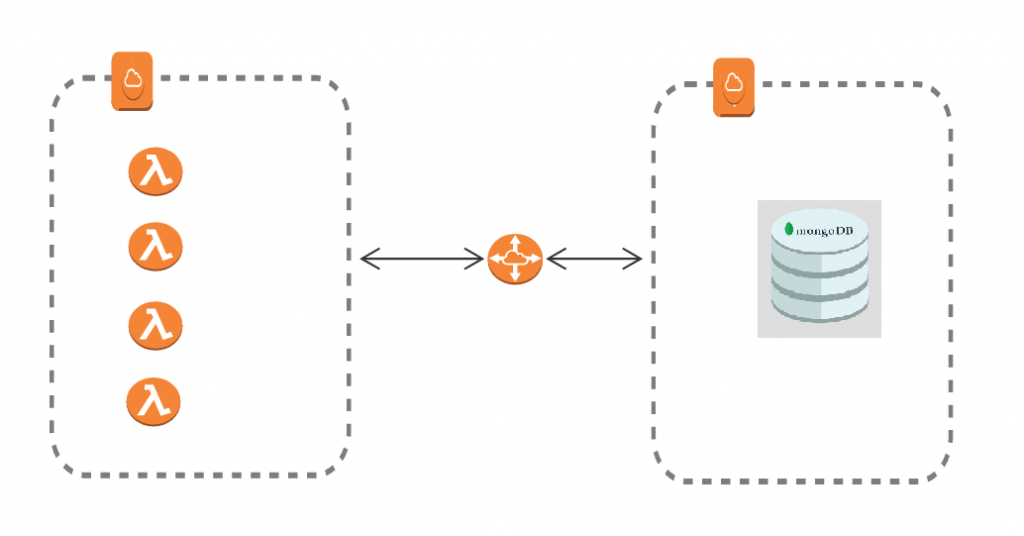
Implementing IoT SSH tunnel AWS requires a well-designed architecture that balances security, scalability, and performance. AWS provides several services that can be integrated to create a secure IoT ecosystem:
Key Components of AWS IoT SSH Tunnel Architecture
- AWS IoT Core: Manages communication between IoT devices and AWS services.
- EC2 Instances: Hosts SSH servers for tunneling connections.
- VPC: Ensures secure network isolation for IoT devices.
- CloudWatch: Monitors and logs SSH tunnel activity for auditing purposes.
By combining these components, organizations can create a secure and scalable IoT infrastructure that meets modern security standards. AWS also offers managed security services, such as AWS Shield and AWS WAF, to protect against DDoS attacks and other threats.
Security Considerations in IoT SSH Tunnel AWS
While IoT SSH tunnel AWS enhances security, it's important to address potential vulnerabilities and implement best practices. Here are some key security considerations:
Best Practices for Securing IoT SSH Tunnels
- Use strong SSH key pairs for authentication.
- Regularly update SSH server software to patch vulnerabilities.
- Implement network segmentation to isolate IoT devices.
- Enable two-factor authentication (2FA) for additional security.
According to a report by Gartner, organizations that fail to implement proper security measures for IoT deployments are at a higher risk of data breaches. By following these best practices, you can significantly reduce the risk of cyberattacks and protect your IoT ecosystem.
Step-by-Step Implementation of IoT SSH Tunnel on AWS
Implementing IoT SSH tunnel AWS involves several steps, from setting up the infrastructure to configuring SSH tunnels. Here's a step-by-step guide:
Step 1: Set Up AWS IoT Core
Create an AWS IoT Core account and configure it to manage your IoT devices. This involves registering devices, creating policies, and setting up communication protocols.
Step 2: Launch EC2 Instances
Launch EC2 instances to host SSH servers. Configure security groups to allow SSH traffic and restrict access to authorized IP addresses.
Step 3: Configure SSH Tunnels
Set up SSH tunnels between IoT devices and EC2 instances. Use SSH key pairs for authentication and enable encryption for all data transmissions.
Step 4: Monitor and Optimize
Use AWS CloudWatch to monitor SSH tunnel activity and optimize performance. Regularly review logs for suspicious activity and update security settings as needed.
Performance Optimization Techniques
To ensure optimal performance of IoT SSH tunnel AWS, consider the following techniques:
Optimize Network Latency
Choose AWS regions that are geographically close to your IoT devices to minimize latency. Use AWS Global Accelerator to improve connection speeds and reliability.
Compress Data Transmissions
Enable data compression on SSH tunnels to reduce bandwidth usage and improve transmission speeds. This is especially important for large-scale IoT deployments.
Scale Resources Dynamically
Use AWS Auto Scaling to dynamically adjust resources based on demand. This ensures that your IoT ecosystem remains performant even during peak usage periods.
Common Issues and Troubleshooting
While IoT SSH tunnel AWS is a powerful solution, it's not without its challenges. Here are some common issues and troubleshooting tips:
Issue 1: Connection Failures
Solution: Verify SSH server configurations and ensure that security groups allow SSH traffic. Check for network connectivity issues and restart EC2 instances if necessary.
Issue 2: Slow Performance
Solution: Optimize SSH tunnel settings and enable data compression. Consider upgrading EC2 instance types for improved performance.
Issue 3: Security Alerts
Solution: Review CloudWatch logs for suspicious activity and update security settings as needed. Enable additional security measures, such as 2FA, to enhance protection.
Real-World Applications of IoT SSH Tunnel AWS
IoT SSH tunnel AWS is being used in various industries to secure IoT communications. Here are some real-world applications:
Healthcare
Hospitals use IoT SSH tunnels to securely transmit patient data between medical devices and cloud systems. This ensures compliance with regulations like HIPAA and protects sensitive health information.
Manufacturing
Manufacturers leverage IoT SSH tunnels to monitor and control industrial equipment in real-time. This improves operational efficiency and reduces downtime.
Smart Cities
Smart city initiatives use IoT SSH tunnels to secure communications between sensors, cameras, and other connected devices. This ensures the reliability of critical infrastructure systems.
Future Trends in IoT SSH Tunnel AWS
As IoT continues to evolve, so will the technologies used to secure its communications. Here are some future trends in IoT SSH tunnel AWS:
Quantum-Safe Encryption
With the advent of quantum computing, organizations are exploring quantum-safe encryption methods to protect IoT communications against future threats.
AI-Driven Security
Artificial intelligence (AI) is being integrated into IoT security systems to detect and respond to threats in real-time. This enhances the effectiveness of SSH tunnels and other security measures.
Edge Computing
Edge computing is becoming increasingly popular in IoT deployments, allowing data processing to occur closer to the source. This reduces latency and improves performance, making it an ideal complement to IoT SSH tunnels.
Conclusion and Call to Action
In conclusion, IoT SSH tunnel AWS is a powerful solution for securing IoT communications. By leveraging SSH tunnels and AWS's robust infrastructure, organizations can protect sensitive data and ensure reliable connections between devices and cloud services. As IoT continues to grow, the importance of secure communication will only increase, making IoT SSH tunnel AWS an essential tool for modern deployments.
We invite you to take action by implementing the strategies outlined in this guide. Share your thoughts and experiences in the comments section below, and don't forget to explore our other articles for more insights into IoT and cloud technologies. Together, we can build a safer and more connected future.
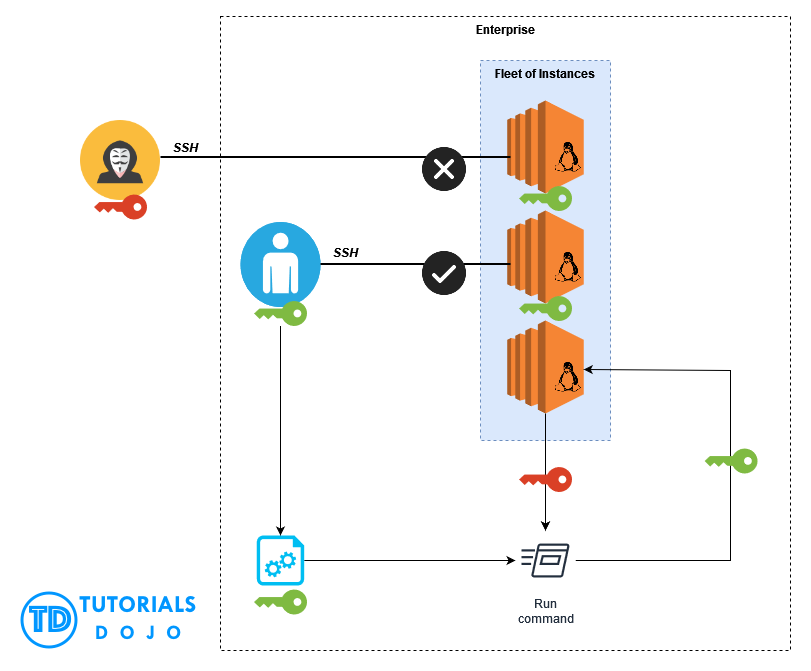
Automatic SSH Key Pair Rotation via AWS Systems Manager Fleet Manager

Iot ssh tunnel guyslopi
Aws ssh tunnel milomini