How To Effectively Manage IoT Devices Behind A Firewall In AWS
In today's rapidly evolving digital landscape, managing IoT devices behind a firewall in AWS has become a critical aspect for businesses aiming to enhance security and efficiency. As the Internet of Things (IoT) continues to grow, the challenge of securely integrating these devices into corporate networks while maintaining robust firewall policies is increasingly significant. Organizations are turning to AWS as a reliable platform to manage their IoT ecosystems, ensuring both performance and security.
This article will delve into the intricacies of managing IoT devices behind a firewall in AWS, providing a comprehensive guide tailored for IT professionals, system administrators, and decision-makers. By exploring the best practices, tools, and strategies available on AWS, we aim to equip you with the knowledge to secure and optimize your IoT infrastructure.
From understanding the importance of firewalls in IoT management to implementing advanced AWS features, this article will serve as your ultimate resource. Whether you are a beginner or an experienced professional, the insights provided here will help you navigate the complexities of IoT device management effectively.
Understanding IoT Device Management
IoT device management refers to the processes and technologies used to monitor, control, and secure IoT devices within a network. With the proliferation of IoT devices, managing them efficiently has become a necessity. In the context of AWS, managing IoT devices behind a firewall involves several key considerations:
- Ensuring secure communication between devices and the cloud.
- Implementing robust firewall rules to protect against unauthorized access.
- Utilizing AWS IoT Core and other services to streamline device management.
By leveraging AWS's comprehensive suite of tools, organizations can achieve seamless integration and management of their IoT devices, even when operating behind a firewall.
Importance of Firewalls in IoT Management
Firewalls play a crucial role in securing IoT devices by filtering incoming and outgoing network traffic based on predetermined security rules. When managing IoT devices behind a firewall in AWS, the following aspects are vital:
1. Enhanced Security: Firewalls act as a barrier between IoT devices and potential threats, ensuring that only authorized traffic is allowed to pass through.
2. Network Segmentation: By segmenting IoT devices into separate networks, firewalls help limit the attack surface and prevent lateral movement of threats.
3. Compliance and Regulation: Many industries have strict regulations regarding data privacy and security, making firewalls an essential component of IoT management.
Key AWS Services for IoT Device Management
AWS IoT Core
AWS IoT Core is a managed cloud service that allows connected devices to easily and securely interact with cloud applications and other devices. It supports billions of devices and trillions of messages, ensuring low latency and high availability. Key features include:
- Device Gateway: Facilitates secure communication between devices and AWS.
- Rules Engine: Enables routing of IoT data to other AWS services for further processing.
- Device Shadow: Maintains a virtual representation of device state, allowing for bidirectional communication.
AWS IoT Device Defender
AWS IoT Device Defender helps protect IoT devices by auditing security configurations and detecting anomalies in device behavior. By continuously monitoring device activity, it ensures compliance with security best practices and alerts administrators of potential threats.
Steps to Manage IoT Devices Behind a Firewall in AWS
1. Configure Firewall Rules
Setting up appropriate firewall rules is essential to ensure secure communication between IoT devices and AWS services. Consider the following best practices:
- Allow only necessary ports and protocols for IoT communication.
- Restrict access to specific IP addresses or CIDR ranges.
- Regularly review and update firewall rules to adapt to changing security requirements.
2. Use AWS IoT Core Endpoints
AWS IoT Core provides custom endpoints that can be used to route traffic through a corporate firewall. By configuring these endpoints, organizations can maintain control over their network traffic while ensuring secure communication with IoT devices.
3. Implement VPC and Subnets
Using Virtual Private Clouds (VPCs) and subnets in AWS allows for greater control over network traffic. By isolating IoT devices in dedicated subnets, organizations can enhance security and simplify firewall management.
Best Practices for IoT Device Management in AWS
To effectively manage IoT devices behind a firewall in AWS, consider implementing the following best practices:
- Regularly update device firmware and security patches.
- Use strong authentication mechanisms, such as AWS IoT Device Defender.
- Monitor device activity and generate alerts for suspicious behavior.
- Document and enforce security policies across all IoT devices.
By adhering to these practices, organizations can significantly reduce the risk of security breaches and ensure smooth operation of their IoT ecosystem.
Advanced Features for Enhanced Security
1. AWS PrivateLink
AWS PrivateLink enables private communication between IoT devices and AWS services without exposing data to the public internet. This feature is particularly useful for organizations with strict security requirements.
2. AWS WAF and Shield
AWS WAF and Shield provide additional layers of protection against web application attacks and Distributed Denial of Service (DDoS) attacks. By integrating these services, organizations can safeguard their IoT infrastructure from a wide range of threats.
Case Studies: Successful IoT Deployments in AWS
Several organizations have successfully implemented IoT solutions in AWS, demonstrating the platform's capabilities in managing devices behind a firewall. For instance:
- Company A: Achieved secure IoT device management by leveraging AWS IoT Core and custom firewall rules.
- Company B: Enhanced network security using AWS PrivateLink and VPCs.
- Company C: Improved operational efficiency through automated device updates and monitoring using AWS IoT Device Defender.
These case studies highlight the versatility and effectiveness of AWS in addressing the challenges of IoT device management.
Challenges and Solutions in IoT Device Management
While managing IoT devices behind a firewall in AWS offers numerous benefits, it also presents certain challenges. Some common issues include:
- Complexity in configuring firewall rules for large-scale deployments.
- Ensuring compatibility between different IoT devices and AWS services.
- Maintaining up-to-date security measures in a rapidly evolving threat landscape.
To overcome these challenges, organizations should invest in training, adopt standardized procedures, and leverage AWS's extensive documentation and support resources.
Conclusion and Call to Action
In conclusion, managing IoT devices behind a firewall in AWS requires a strategic approach that balances security, efficiency, and scalability. By understanding the importance of firewalls, utilizing AWS's robust services, and adhering to best practices, organizations can successfully navigate the complexities of IoT device management.
We encourage readers to implement the strategies outlined in this article and explore AWS's extensive resources for further guidance. To enhance your IoT management capabilities, consider:
- Subscribing to AWS newsletters and updates.
- Engaging with the AWS community for shared knowledge and experiences.
- Exploring additional AWS services that may complement your IoT infrastructure.
Feel free to leave your thoughts and questions in the comments section below, and don't hesitate to share this article with others who may find it valuable.
Table of Contents
- Understanding IoT Device Management
- Importance of Firewalls in IoT Management
- Key AWS Services for IoT Device Management
- Steps to Manage IoT Devices Behind a Firewall in AWS
- Best Practices for IoT Device Management in AWS
- Advanced Features for Enhanced Security
- Case Studies: Successful IoT Deployments in AWS
- Challenges and Solutions in IoT Device Management
- Conclusion and Call to Action
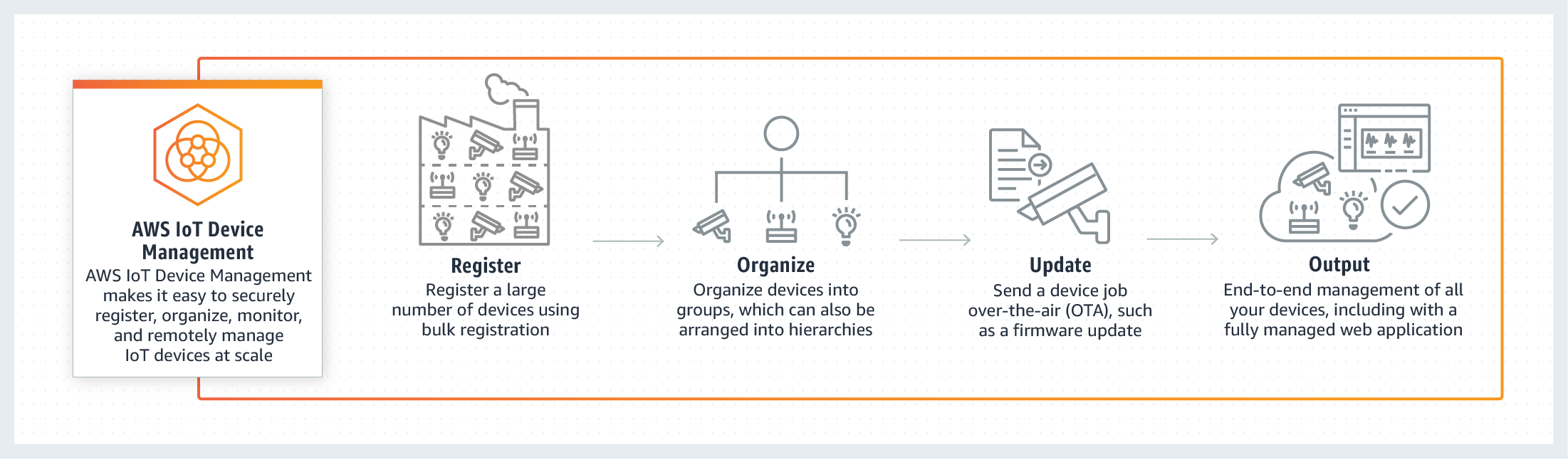
Monitoring IoT Devices AWS IoT Device Management AWS
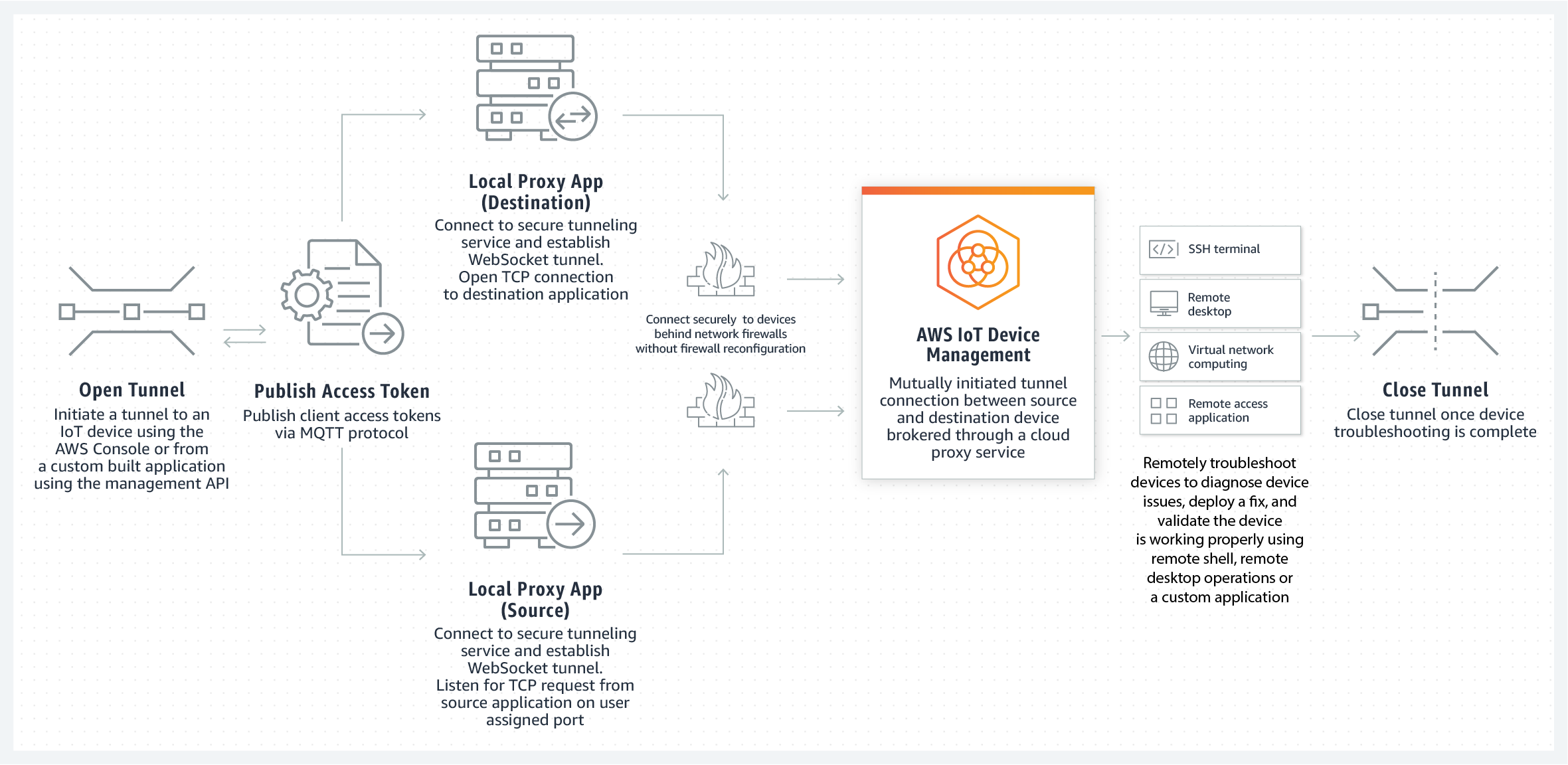
Monitoring IoT Devices AWS IoT Device Management AWS

Manage IoT device state anywhere using AWS IoT Device Shadow service