Raspberry Pi Secure SSH: A Comprehensive Guide For Enhanced Security
In the digital age, securing your devices has become more critical than ever. If you're using a Raspberry Pi, ensuring secure remote access through SSH (Secure Shell) is paramount. This article delves into the best practices for securing SSH on your Raspberry Pi, offering actionable tips and expert guidance to protect your system from potential threats.
Raspberry Pi has revolutionized the way we interact with technology, offering versatile applications ranging from home automation to server hosting. However, with its widespread adoption, the importance of securing SSH connections cannot be overstated. SSH serves as the gateway for remote access, and its security directly impacts the integrity of your projects.
By following the strategies outlined in this article, you can safeguard your Raspberry Pi from unauthorized access and potential cyber threats. Whether you're a beginner or an advanced user, this guide will provide the tools and knowledge necessary to enhance your system's security effectively.
Table of Contents
- Introduction to Raspberry Pi SSH
- Understanding Default SSH Settings
- Why Securing SSH is Essential
- Updating Your Raspberry Pi System
- Disabling Password Authentication
- Implementing Key-Based Authentication
- Changing the Default SSH Port
- Configuring Firewall Settings
- Monitoring SSH Logs for Suspicious Activity
- Advanced Security Measures
- Conclusion and Call to Action
Introduction to Raspberry Pi SSH
SSH, or Secure Shell, is a network protocol that allows users to securely connect to and manage remote devices over an unsecured network. For Raspberry Pi users, SSH is often used to manage the device without physical access, making it a powerful yet potentially vulnerable tool if not properly secured.
By default, SSH is disabled on modern Raspberry Pi operating systems. Users must explicitly enable it to use the feature. This deliberate design choice reflects the growing emphasis on security in IoT devices. Understanding how SSH works and how to configure it securely is essential for anyone leveraging Raspberry Pi's capabilities.
Key features of SSH include encrypted communication, authentication mechanisms, and the ability to execute commands remotely. However, these features also make SSH a prime target for attackers looking to gain unauthorized access to systems. This section will explore the basics of SSH and why securing it is crucial for Raspberry Pi users.
Understanding Default SSH Settings
Default SSH Configuration
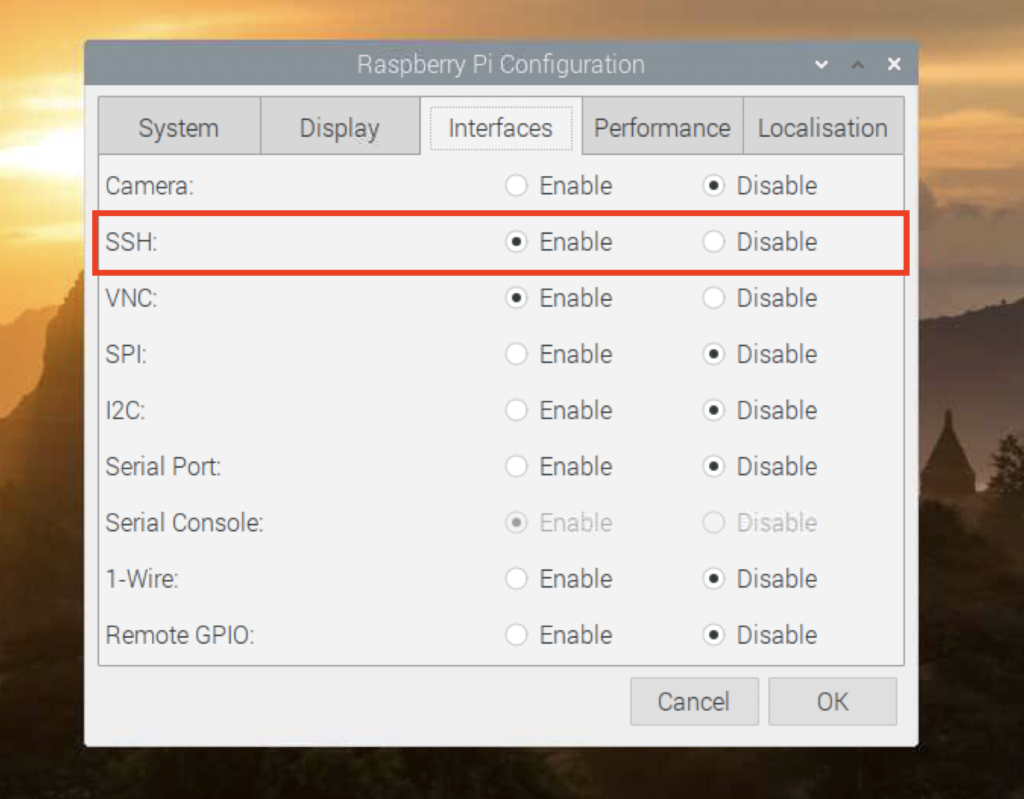
When you first set up your Raspberry Pi, SSH is disabled by default. This default setting is part of the security-hardening efforts implemented in recent versions of Raspberry Pi OS. To enable SSH, you can either:
- Use the Raspberry Pi Configuration tool in the desktop environment.
- Create an empty file named "ssh" on the boot partition of your SD card.
Once enabled, SSH uses port 22 by default, which is widely recognized as the standard SSH port. However, this default configuration can make your Raspberry Pi an easy target for automated attacks. Understanding these default settings is the first step toward securing your SSH setup.
Security Risks with Default Settings
Using default SSH settings poses several security risks:
- Port Scanning: Attackers can easily identify devices with open port 22.
- Brute Force Attacks: Default configurations often rely on weak passwords, making them susceptible to brute force attempts.
- Lack of Encryption: While SSH itself is encrypted, default settings may not include additional layers of security.
By modifying these default settings, you can significantly reduce the risk of unauthorized access and enhance the overall security of your Raspberry Pi.
Why Securing SSH is Essential
SSH provides a secure channel for remote access, but its security depends heavily on how it is configured. For Raspberry Pi users, securing SSH is essential for several reasons:
Firstly, Raspberry Pi devices are often deployed in environments where they are exposed to the internet. This exposure increases the likelihood of attacks from malicious actors. By securing SSH, you can prevent unauthorized access and protect sensitive data stored on your device.
Secondly, SSH is a critical component of many Raspberry Pi projects, including home servers, automation systems, and IoT devices. A compromised SSH connection can disrupt these projects and lead to data breaches or system failures. Implementing robust security measures ensures the integrity and reliability of your projects.
Lastly, securing SSH aligns with best practices in cybersecurity, demonstrating a commitment to protecting your digital assets. This section will explore specific strategies to enhance SSH security on your Raspberry Pi.
Updating Your Raspberry Pi System
Importance of System Updates
Keeping your Raspberry Pi system up to date is one of the most effective ways to enhance SSH security. Updates often include critical security patches that address vulnerabilities in the operating system and its components.
To update your Raspberry Pi, open a terminal and run the following commands:
sudo apt update
sudo apt upgrade
Regular Maintenance
In addition to updating the system, regular maintenance is essential. This includes:
- Checking for and installing firmware updates.
- Removing unnecessary software and services.
- Monitoring system logs for suspicious activity.
By maintaining an updated and well-maintained system, you create a solid foundation for securing SSH and other network services.
Disabling Password Authentication
Password-based authentication is one of the weakest links in SSH security. Attackers can exploit weak passwords through brute force attacks, making it essential to disable this feature and switch to more secure alternatives.
Steps to Disable Password Authentication
To disable password authentication on your Raspberry Pi:
- Open the SSH configuration file using a text editor:
- sudo nano /etc/ssh/sshd_config
- Locate the line that reads "PasswordAuthentication yes" and change it to "PasswordAuthentication no".
- Save the file and restart the SSH service:
- sudo systemctl restart ssh
By disabling password authentication, you eliminate a significant attack vector and enhance the security of your SSH setup.
Implementing Key-Based Authentication
Key-based authentication is a more secure alternative to password-based authentication. It uses cryptographic keys to verify the identity of users, making it much harder for attackers to gain unauthorized access.
Creating SSH Keys
To implement key-based authentication, follow these steps:
- Generate a key pair on your local machine:
- ssh-keygen -t rsa -b 4096
- Copy the public key to your Raspberry Pi:
- ssh-copy-id pi@your-raspberry-pi-ip
Once the keys are set up, you can log in to your Raspberry Pi without entering a password, relying instead on the security of your private key.
Best Practices for Key Management
When using key-based authentication, it's important to follow best practices:
- Use strong, unique keys.
- Protect your private key with a passphrase.
- Regularly review and rotate keys as needed.
Implementing key-based authentication significantly enhances the security of your SSH connections while maintaining ease of access for authorized users.
Changing the Default SSH Port
Changing the default SSH port is a simple yet effective way to reduce the risk of automated attacks. Most attackers target port 22, the default SSH port, making it an easy target for port scanning and brute force attempts.
Steps to Change the SSH Port
To change the SSH port on your Raspberry Pi:
- Open the SSH configuration file:
- sudo nano /etc/ssh/sshd_config
- Locate the line that reads "Port 22" and change it to a different port number (e.g., 2222).
- Save the file and restart the SSH service:
- sudo systemctl restart ssh
By changing the default port, you reduce the visibility of your SSH service and make it harder for attackers to identify your device.
Configuring Firewall Settings
A firewall acts as a barrier between your Raspberry Pi and the outside world, controlling which traffic is allowed to reach your device. Configuring firewall settings is an essential step in securing SSH.
Using UFW for Firewall Management
UFW (Uncomplicated Firewall) is a user-friendly tool for managing firewall rules on your Raspberry Pi. To set it up:
- Install UFW if it's not already installed:
- sudo apt install ufw
- Allow SSH traffic on your chosen port:
- sudo ufw allow 2222/tcp
- Enable the firewall:
- sudo ufw enable
Configuring a firewall limits access to your SSH service, reducing the risk of unauthorized access and enhancing overall security.
Monitoring SSH Logs for Suspicious Activity
Regularly monitoring SSH logs is crucial for identifying and responding to potential security threats. Logs provide valuable insights into access attempts, both successful and failed, allowing you to take proactive measures to protect your system.
Locating SSH Logs
SSH logs are typically stored in the following file:
/var/log/auth.log
You can view these logs using a text editor or command-line tools like "tail" or "grep". For example, to monitor recent login attempts:
sudo tail -f /var/log/auth.log
Responding to Suspicious Activity
If you detect suspicious activity in your SSH logs, take immediate action:
- Review and update firewall rules.
- Change SSH port if necessary.
- Investigate and block malicious IP addresses.
By staying vigilant and responding promptly to threats, you can maintain the security of your SSH connections and protect your Raspberry Pi from potential attacks.
Advanced Security Measures
Implementing Two-Factor Authentication
Two-factor authentication (2FA) adds an extra layer of security to your SSH setup. By requiring a second form of verification, such as a one-time password, you significantly reduce the risk of unauthorized access.
Using Fail2Ban for Intrusion Prevention
Fail2Ban is a popular tool for preventing brute force attacks. It monitors log files for suspicious activity and blocks IP addresses that exhibit malicious behavior. To install and configure Fail2Ban:
- Install Fail2Ban:
- sudo apt install fail2ban
- Copy the default configuration file:
- sudo cp /etc/fail2ban/jail.conf /etc/fail2ban/jail.local
- Start and enable Fail2Ban:
- sudo systemctl start fail2ban
- sudo systemctl enable fail2ban
Advanced security measures like these provide additional protection for your SSH connections, ensuring the highest level of security for your Raspberry Pi.
Conclusion and Call to Action
Securing SSH on your Raspberry Pi is a critical step in protecting your device and its data from potential threats. By following the strategies outlined in this article, including disabling password authentication, implementing key-based authentication, changing the default SSH port, configuring firewall settings, and monitoring logs, you can significantly enhance the security of your SSH connections.
We encourage you to take action by implementing these security measures on your Raspberry Pi. Share your experiences and insights in the comments below, and explore other articles on our site for more tips and tricks to secure your digital world. Together, we can create a safer and more secure environment for all Raspberry Pi users.
How to SSH Into Your Raspberry Pi in Under 3 Minutes

How to Connect via SSH to a Raspberry Pi Tony Teaches Tech
How to Enable SSH on Raspberry Pi? TechSphinx