Best SSH Remote IoT Raspberry Pi: A Comprehensive Guide
SSH (Secure Shell) is a powerful tool for managing IoT devices, especially when using a Raspberry Pi as the central hub for remote operations. Whether you're a hobbyist, developer, or professional working on IoT projects, understanding how to leverage SSH for remote access can significantly enhance your workflow. This guide will walk you through everything you need to know about setting up and managing the best SSH remote IoT Raspberry Pi configurations.
As IoT continues to grow in popularity, more and more devices are being connected to networks, requiring robust remote management solutions. SSH provides a secure and reliable way to control these devices from anywhere in the world. In this article, we'll explore the key aspects of SSH, including setup, security, and optimization for IoT projects using Raspberry Pi.
By the end of this guide, you'll have a solid understanding of how to implement the best SSH remote IoT Raspberry Pi setup for your projects. Whether you're a beginner or an experienced user, this article will provide valuable insights and actionable tips to help you get started.
Table of Contents
- Introduction to SSH
- Raspberry Pi Overview
- Setting Up SSH on Raspberry Pi
- Securing Your SSH Connection
- Remote Access Techniques
- Best Practices for SSH IoT
- Troubleshooting Common Issues
- Optimizing Performance
- Advanced Features
- Conclusion
Introduction to SSH
SSH, or Secure Shell, is a cryptographic network protocol used for secure communication over unsecured networks. It allows users to access remote systems and execute commands securely. When it comes to IoT devices, SSH plays a crucial role in enabling remote management and monitoring.
Why Use SSH for IoT?
- Secure communication between devices
- Remote access to IoT devices without physical presence
- Encryption of data during transmission
- Support for various authentication methods
For Raspberry Pi users, SSH is a default feature that can be enabled with minimal configuration. This makes it an ideal choice for managing IoT projects remotely.
Raspberry Pi Overview
The Raspberry Pi is a versatile single-board computer that has become a staple in the world of IoT. Its affordability, compact size, and ease of use make it an excellent platform for developing and deploying IoT solutions.
Key Features of Raspberry Pi
- Support for multiple operating systems
- Low power consumption
- Wide range of GPIO pins for sensor integration
- Compatibility with various programming languages
When combined with SSH, the Raspberry Pi becomes a powerful tool for managing IoT devices remotely. This setup allows users to monitor and control their devices from anywhere in the world.
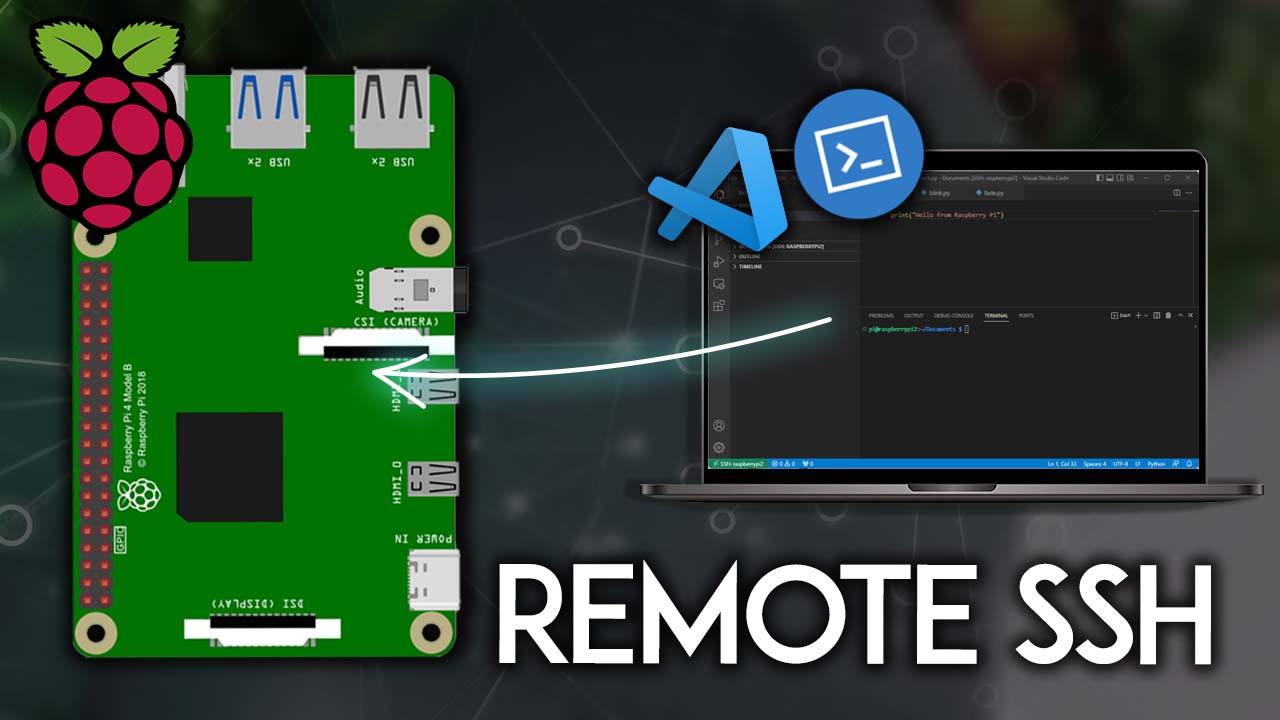
Setting Up SSH on Raspberry Pi
Setting up SSH on a Raspberry Pi is a straightforward process. Follow these steps to enable SSH on your device:
Step 1: Enable SSH
To enable SSH on your Raspberry Pi, you can use the Raspberry Pi Configuration tool or edit the configuration file directly.
- Open the Raspberry Pi Configuration tool from the main menu.
- Navigate to the "Interfaces" tab.
- Select "SSH" and enable it.
Step 2: Connect to Your Raspberry Pi
Once SSH is enabled, you can connect to your Raspberry Pi using an SSH client. Popular SSH clients include:
- PuTTY (for Windows)
- Terminal (for macOS and Linux)
Use the following command to connect:
ssh pi@raspberrypi.local
Securing Your SSH Connection
Security is a critical consideration when using SSH for remote access. Here are some best practices to ensure your SSH connection is secure:
Use Strong Passwords
Ensure that all user accounts on your Raspberry Pi have strong, unique passwords. Avoid using default passwords like "raspberry" for the pi user.
Disable Root Login
Disabling root login via SSH adds an extra layer of security. Edit the SSH configuration file to disable root login:
sudo nano /etc/ssh/sshd_config
Find the line "PermitRootLogin" and set it to "no".
Use Key-Based Authentication
Key-based authentication is a more secure alternative to password-based authentication. Generate an SSH key pair and add the public key to your Raspberry Pi's authorized_keys file.
Remote Access Techniques
There are several techniques you can use to enhance remote access to your Raspberry Pi:
Port Forwarding
Port forwarding allows you to access your Raspberry Pi from outside your local network. Configure your router to forward traffic from a specific port to your Raspberry Pi's IP address.
Dynamic DNS
Dynamic DNS services can help you access your Raspberry Pi using a domain name instead of an IP address. This is especially useful if your ISP assigns dynamic IP addresses.
Best Practices for SSH IoT
When using SSH for IoT projects, it's important to follow best practices to ensure smooth operation and security:
Regular Updates
Keep your Raspberry Pi's operating system and software up to date to protect against vulnerabilities.
Monitor Network Traffic
Use tools like Wireshark to monitor network traffic and detect any suspicious activity.
Limit User Access
Restrict SSH access to only the users who need it. Use the "AllowUsers" directive in the SSH configuration file to specify which users can log in.
Troubleshooting Common Issues
Even with proper setup, issues can arise when using SSH for IoT projects. Here are some common problems and their solutions:
Connection Refused
If you receive a "Connection refused" error, ensure that SSH is enabled on your Raspberry Pi and that the correct IP address or hostname is being used.
Authentication Failed
Check that the username and password are correct. If using key-based authentication, ensure that the public key is correctly added to the authorized_keys file.
Optimizing Performance
Optimizing the performance of your SSH connection can improve the efficiency of your IoT projects:
Compression
Enable compression in the SSH configuration file to reduce the amount of data transmitted over the network.
Limit Bandwidth
Set a bandwidth limit for SSH connections to prevent them from consuming too much network resources.
Advanced Features
SSH offers several advanced features that can enhance your IoT projects:
Tunneling
SSH tunneling allows you to securely transfer data between devices. This is particularly useful for transferring sensitive information.
Port Forwarding
Use SSH port forwarding to access services running on your Raspberry Pi from remote locations.
Conclusion
In conclusion, setting up the best SSH remote IoT Raspberry Pi configuration involves a combination of proper setup, security measures, and optimization techniques. By following the guidelines outlined in this article, you can create a robust and secure environment for managing your IoT devices remotely.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, don't forget to explore other articles on our site for more tips and tricks on IoT and Raspberry Pi projects.
References:
Programming Raspberry Pi Remotely using VS Code (RemoteSSH) Random

Best RemoteIoT VPC SSH Raspberry Pi Free A Comprehensive Guide

Best SSH RemoteIoT Device Raspberry Pi For Secure And Efficient Remote