Comprehensive RemoteIoT Device SSH Tutorial: Your Ultimate Guide
RemoteIoT devices have become an essential part of modern technology, enabling seamless connectivity and control over various systems from anywhere in the world. Whether you're a beginner or an advanced user, understanding how to securely access and manage these devices through SSH is crucial. This tutorial will walk you through everything you need to know about setting up and managing remote IoT devices using SSH.
In today's interconnected world, remote IoT device management has transformed industries, from manufacturing to healthcare. SSH (Secure Shell) plays a pivotal role in ensuring secure communication between devices and users. By mastering this technology, you can significantly enhance the security and efficiency of your IoT setup.
As technology continues to evolve, learning how to use SSH for remote IoT devices is more important than ever. This guide will provide you with step-by-step instructions, expert tips, and essential best practices to ensure a smooth and secure experience. Let's dive in!
- Valerie Curtin
- Georgia Man 1 4 Million Speeding Ticket
- Who Is Kathleen Turners Partner
- Christine White Ludacris
Table of Contents
Introduction to RemoteIoT Devices and SSH
Setting Up Your RemoteIoT Device
Common Issues and Troubleshooting
Best Practices for RemoteIoT Device Management
Introduction to RemoteIoT Devices and SSH
RemoteIoT devices refer to internet-connected devices that can be accessed and controlled remotely. These devices are widely used in various applications, such as home automation, industrial monitoring, and smart agriculture. SSH (Secure Shell) is a protocol designed to provide secure access to these devices, ensuring data integrity and confidentiality.
SSH has become the go-to method for remote device management due to its robust encryption and authentication mechanisms. Whether you're configuring a Raspberry Pi or managing a fleet of industrial sensors, SSH offers a reliable and secure solution. This section will provide an overview of SSH and its importance in the context of remote IoT devices.
Why Use SSH for RemoteIoT Devices?
SSH offers several advantages over other remote access methods, including:
- Strong encryption to protect data during transmission.
- Reliable authentication mechanisms to prevent unauthorized access.
- Compatibility with a wide range of devices and operating systems.
- Support for scripting and automation, making it ideal for large-scale deployments.
Setting Up Your RemoteIoT Device
Before diving into SSH, it's essential to properly configure your remote IoT device. This includes installing the necessary software, setting up network connectivity, and ensuring basic security measures are in place.
Step-by-Step Setup Guide
- Install an Operating System: Choose a lightweight OS like Raspbian for Raspberry Pi or Ubuntu for more powerful devices.
- Enable SSH Service: Most modern operating systems come with SSH pre-installed. However, you may need to enable it manually.
- Configure Network Settings: Ensure your device is connected to a stable network and has a static IP address if possible.
- Test Basic Connectivity: Ping your device from another computer to confirm network accessibility.
Understanding SSH Basics
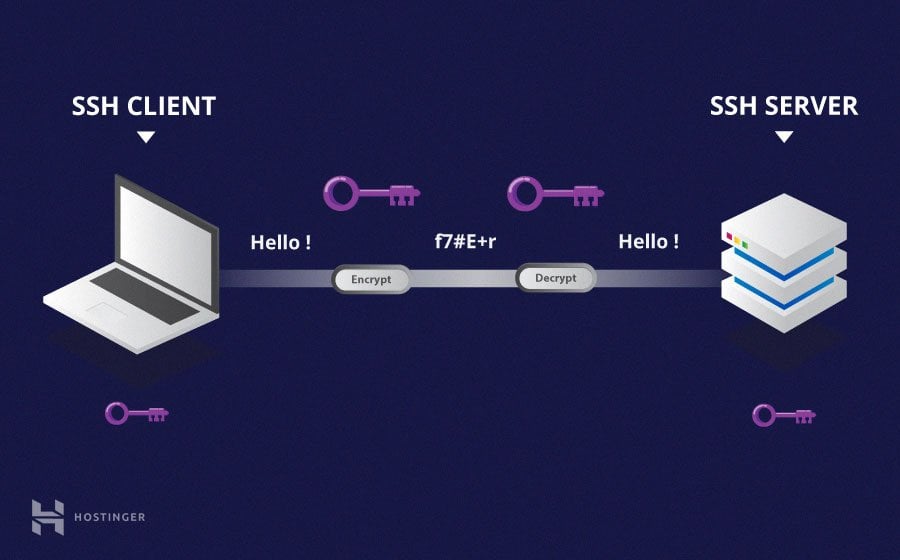
SSH, or Secure Shell, is a cryptographic network protocol that facilitates secure communication between devices. It operates on port 22 by default and uses public-key cryptography for authentication.
Key Components of SSH
- Client and Server: The SSH client initiates the connection, while the SSH server listens for incoming requests.
- Public and Private Keys: These keys are used to authenticate users without requiring passwords, enhancing security.
- Encryption: SSH encrypts all data transmitted between the client and server, preventing eavesdropping and tampering.
How to Connect via SSH
Connecting to your RemoteIoT device via SSH is straightforward once the setup is complete. Below is a step-by-step guide to help you establish a secure connection.
Connecting from a Terminal
To connect via SSH, open a terminal window and use the following command:
ssh username@remote_device_ip
Replace username with your device's login name and remote_device_ip with the IP address of your IoT device.
Using SSH Clients
If you're using Windows or prefer a graphical interface, tools like PuTTY or MobaXterm can simplify the connection process. Simply enter the IP address and port number, and you're ready to go!
Enhancing SSH Security
While SSH is inherently secure, there are additional steps you can take to further protect your RemoteIoT device.
Best Security Practices
- Change Default Port: Modify the default SSH port (22) to a non-standard number to reduce automated attacks.
- Use Key-Based Authentication: Disable password-based logins and rely solely on public-private key pairs.
- Limit Access: Restrict SSH access to specific IP addresses or ranges using firewall rules.
- Keep Software Updated: Regularly update your device's OS and SSH server to patch known vulnerabilities.
Common Issues and Troubleshooting
Even with proper setup, issues may arise when using SSH with RemoteIoT devices. Here are some common problems and their solutions:
Connection Refused
If you receive a "Connection refused" error, check the following:
- Ensure the SSH service is running on the device.
- Verify the IP address and port number are correct.
- Check firewall settings to ensure they allow SSH traffic.
Authentication Failed
If authentication fails, try the following:
- Double-check your username and password.
- Ensure your public key is correctly added to the authorized_keys file.
- Verify the SSH configuration file for any misconfigurations.
Automating SSH Connections
For large-scale deployments, automating SSH connections can save time and reduce errors. This section will cover some popular tools and techniques for automating SSH tasks.
Using SSH Config Files
Create an SSH config file to store connection details, such as hostnames, usernames, and keys. This simplifies the connection process and improves consistency.
Scripting with Bash
Bash scripts can automate repetitive SSH tasks, such as running commands or transferring files. Below is an example script to execute a command on a remote device:
ssh user@remote_device "command_to_execute"
Real-World Use Cases
SSH is widely used in various industries for managing RemoteIoT devices. Here are a few examples:
Home Automation
SSH enables users to remotely control smart home devices, such as lighting, thermostats, and security systems, ensuring convenience and safety.
Industrial Monitoring
In manufacturing, SSH is used to monitor and control machinery, collect sensor data, and perform preventive maintenance, improving operational efficiency.
Environmental Monitoring
SSH facilitates the management of remote weather stations and environmental sensors, providing critical data for research and decision-making.
Best Practices for RemoteIoT Device Management
To ensure the smooth and secure operation of your RemoteIoT devices, follow these best practices:
Regular Backups
Create regular backups of your device's configuration and data to prevent data loss in case of hardware failure or cyberattacks.
Monitor Logs
Regularly review SSH logs to detect and respond to suspicious activities promptly.
Update Firmware
Keep your device's firmware up to date to benefit from the latest features and security patches.
Conclusion and Next Steps
This comprehensive guide has covered everything you need to know about managing RemoteIoT devices using SSH. From setup and connection to security and automation, you now have the tools and knowledge to take full control of your IoT setup.
We encourage you to apply what you've learned and explore additional resources to deepen your understanding. Feel free to leave a comment below with any questions or share this article with others who may find it useful. Happy tinkering!
For further reading, consider exploring advanced topics such as SSH tunneling, port forwarding, and containerization for IoT devices. Together, these technologies can revolutionize the way you interact with your connected world.
Data sources: [1] SSH Official Documentation, [2] Microsoft Docs, [3] Raspberry Pi Documentation.
SSH Tutorial What is SSH, Encryptions and Ports
RemoteIoT Device SSH Tutorial A Comprehensive Guide For Secure Remote

SSH RemoteIoT Device Tutorial A Comprehensive Guide To Secure Remote