Securely Connect Remote IoT VPC: A Comprehensive Guide For Enhanced Network Security
As the Internet of Things (IoT) continues to revolutionize the way we interact with technology, securely connecting remote IoT devices within a Virtual Private Cloud (VPC) has become a critical priority for businesses and organizations. The increasing reliance on IoT devices for data collection, automation, and monitoring introduces new challenges in maintaining secure network connections. With remote IoT deployments becoming more common, ensuring robust security measures is essential to protect sensitive data and prevent unauthorized access.
Connecting remote IoT devices to a VPC requires a strategic approach that combines advanced security protocols, network segmentation, and encryption techniques. This article will explore the best practices for securely connecting remote IoT VPCs, providing actionable insights and expert advice to help you fortify your network infrastructure. Whether you're managing a small-scale IoT deployment or overseeing a large enterprise network, this guide will equip you with the knowledge needed to safeguard your digital assets.
By the end of this article, you'll have a deeper understanding of the challenges associated with remote IoT VPC connectivity and the tools available to address them. Let's dive into the world of IoT security and explore how you can build a resilient and secure network environment.
- Aishwarya Rajesh Father
- Michael Myers Live Wallapper
- Georgia Man 1 4 Million Speeding Ticket
- What Does Kiara Cabral Do For A Living
Table of Contents
- Introduction to Remote IoT VPC
- Importance of Secure Connections
- Understanding VPC Architecture
- Key Security Challenges
- Best Practices for Secure Connections
- Encryption Methods for IoT
- Network Segmentation
- Using VPN for Secure Connections
- Monitoring and Managing IoT Devices
- Conclusion and Next Steps
Introduction to Remote IoT VPC
A Virtual Private Cloud (VPC) is a secure and isolated environment within a cloud platform that allows organizations to deploy and manage their resources. When it comes to IoT, securely connect remote IoT VPC becomes a vital consideration due to the distributed nature of IoT devices. These devices often operate in remote locations, transmitting sensitive data that requires protection against cyber threats.
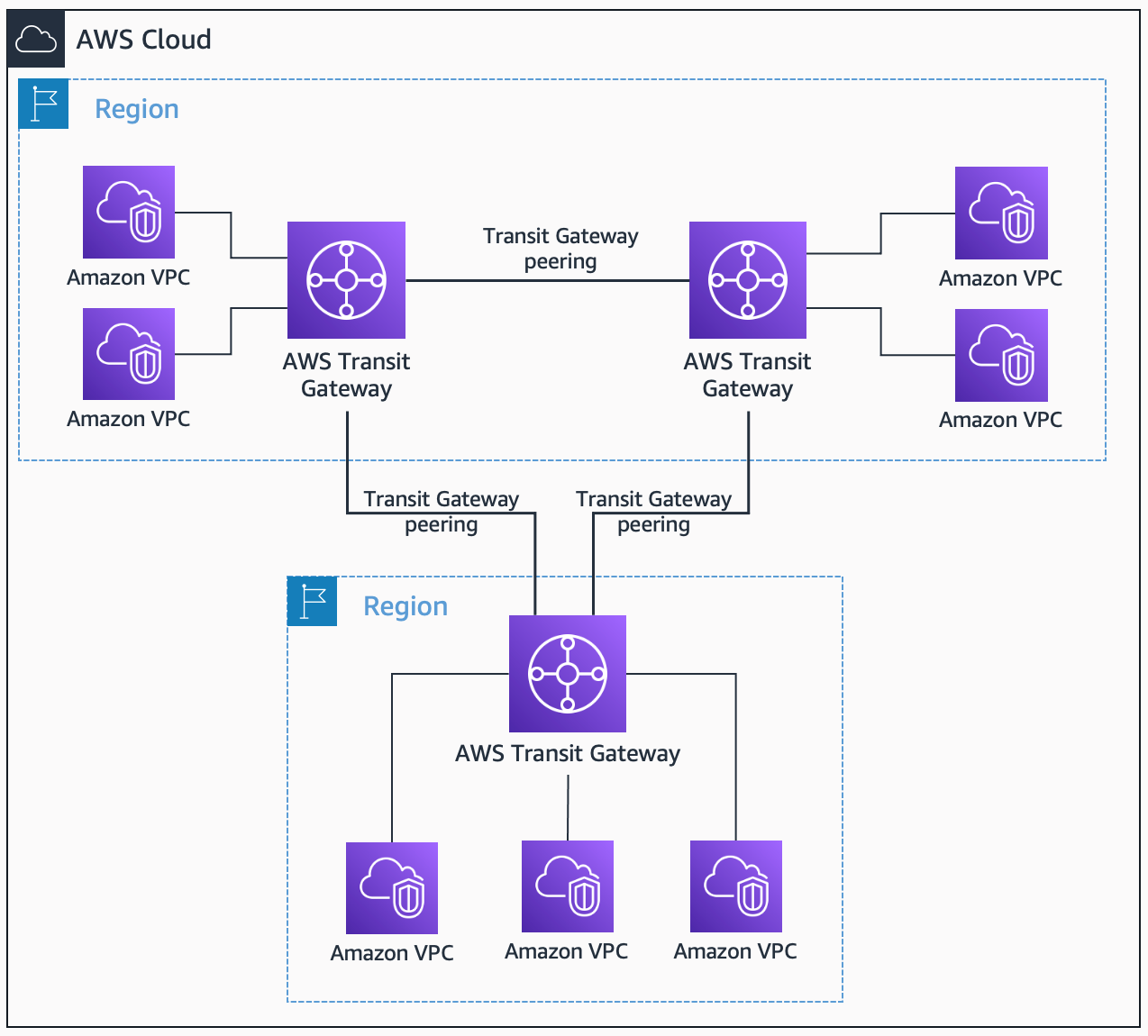
Understanding the basics of VPC architecture is the first step in ensuring secure connectivity. A VPC provides a private network where you can launch resources, such as IoT devices, in a virtual network that you define. This setup allows for greater control over network configurations, including IP address ranges, subnets, and security groups.
Why Secure IoT VPC Connectivity Matters
Securely connecting remote IoT devices to a VPC ensures that data transmission remains protected from unauthorized access. This is particularly important for industries handling sensitive information, such as healthcare, finance, and smart cities. By implementing robust security measures, organizations can minimize the risk of data breaches and ensure compliance with industry standards.
Importance of Secure Connections
Establishing secure connections for remote IoT VPC deployments is not just a best practice—it's a necessity. The interconnected nature of IoT devices makes them vulnerable to cyberattacks, which can compromise the integrity of the entire network. Secure connections safeguard against unauthorized access, data breaches, and malicious activities.
- Data Privacy: Protect sensitive data transmitted between IoT devices and the VPC.
- Network Integrity: Prevent unauthorized modifications to network configurations.
- Compliance: Meet regulatory requirements for data protection and cybersecurity.
Understanding VPC Architecture
A VPC architecture is designed to provide a secure and scalable environment for deploying IoT devices. It allows organizations to define their own network topology, including subnets, route tables, and security groups. By understanding the components of a VPC, you can better implement secure connectivity solutions.
Key Components of VPC Architecture
- Subnets: Logical partitions within a VPC that enable segmentation of network traffic.
- Security Groups: Act as virtual firewalls to control inbound and outbound traffic for instances.
- Route Tables: Define how traffic flows between subnets and external networks.
Key Security Challenges
Securing remote IoT VPC deployments comes with its own set of challenges. From device authentication to network monitoring, addressing these challenges requires a comprehensive approach. Below are some of the most common security challenges faced in IoT VPC environments:
- Device Authentication: Ensuring that only authorized devices can connect to the VPC.
- Data Encryption: Protecting data in transit and at rest from unauthorized access.
- Network Segmentation: Isolating IoT devices from other network resources to minimize risk.
Best Practices for Secure Connections
Implementing best practices for securely connecting remote IoT VPC deployments can significantly enhance network security. These practices include using strong authentication mechanisms, enforcing encryption protocols, and regularly monitoring network activity.
Implementing Strong Authentication
Device authentication is a critical component of IoT security. By using certificates, tokens, or biometric authentication, you can ensure that only legitimate devices gain access to the VPC. This reduces the risk of unauthorized access and helps maintain network integrity.
Enforcing Encryption Protocols
Encryption is essential for protecting data transmitted between IoT devices and the VPC. Protocols such as TLS and SSL provide secure communication channels, ensuring that sensitive information remains confidential during transmission.
Encryption Methods for IoT
Choosing the right encryption method for your IoT deployment depends on several factors, including the type of data being transmitted and the level of security required. Below are some commonly used encryption methods for IoT:
- TLS (Transport Layer Security): Provides secure communication over the internet.
- SSL (Secure Sockets Layer): An older encryption protocol still used in some IoT applications.
- IPSec (Internet Protocol Security): Secures IP communications by authenticating and encrypting packets.
Network Segmentation
Network segmentation is a powerful technique for enhancing IoT security. By isolating IoT devices into separate subnets, you can limit their access to critical network resources and reduce the attack surface. This approach minimizes the impact of a potential breach and helps maintain network stability.
Benefits of Network Segmentation
- Improved security by isolating IoT devices.
- Enhanced network performance through reduced traffic congestion.
- Simplified management of IoT devices and resources.
Using VPN for Secure Connections
A Virtual Private Network (VPN) can be used to establish secure connections between remote IoT devices and the VPC. By encrypting data transmitted over public networks, a VPN ensures that sensitive information remains protected from unauthorized access. This is particularly useful for IoT deployments in remote or untrusted environments.
Types of VPNs for IoT
- Site-to-Site VPN: Connects two or more networks securely over the internet.
- Remote Access VPN: Allows individual devices to connect securely to a network.
Monitoring and Managing IoT Devices
Continuous monitoring and management of IoT devices are essential for maintaining secure remote IoT VPC deployments. By implementing robust monitoring tools and processes, you can detect and respond to security threats in real-time, ensuring the integrity of your network.
Tools for IoT Device Management
- IoT Platforms: Provide centralized management and monitoring capabilities for IoT devices.
- Security Analytics Tools: Analyze network traffic to identify potential security threats.
Conclusion and Next Steps
Securing remote IoT VPC deployments requires a strategic approach that combines advanced security protocols, network segmentation, and encryption techniques. By following the best practices outlined in this article, you can significantly enhance the security of your IoT network and protect sensitive data from cyber threats.
We encourage you to take the next step by implementing these security measures in your own IoT deployment. Leave a comment below to share your thoughts or ask questions about securely connecting remote IoT VPC. Don't forget to explore other articles on our site for more insights into IoT security and network management.
For further reading, consider exploring authoritative sources such as the National Institute of Standards and Technology (NIST) and the International Organization for Standardization (ISO) for comprehensive guidelines on IoT security.
Securely Connect RemoteIoT VPC To AWS A Comprehensive Guide
Securely Connect RemoteIoT VPC A Comprehensive Guide For Enhanced
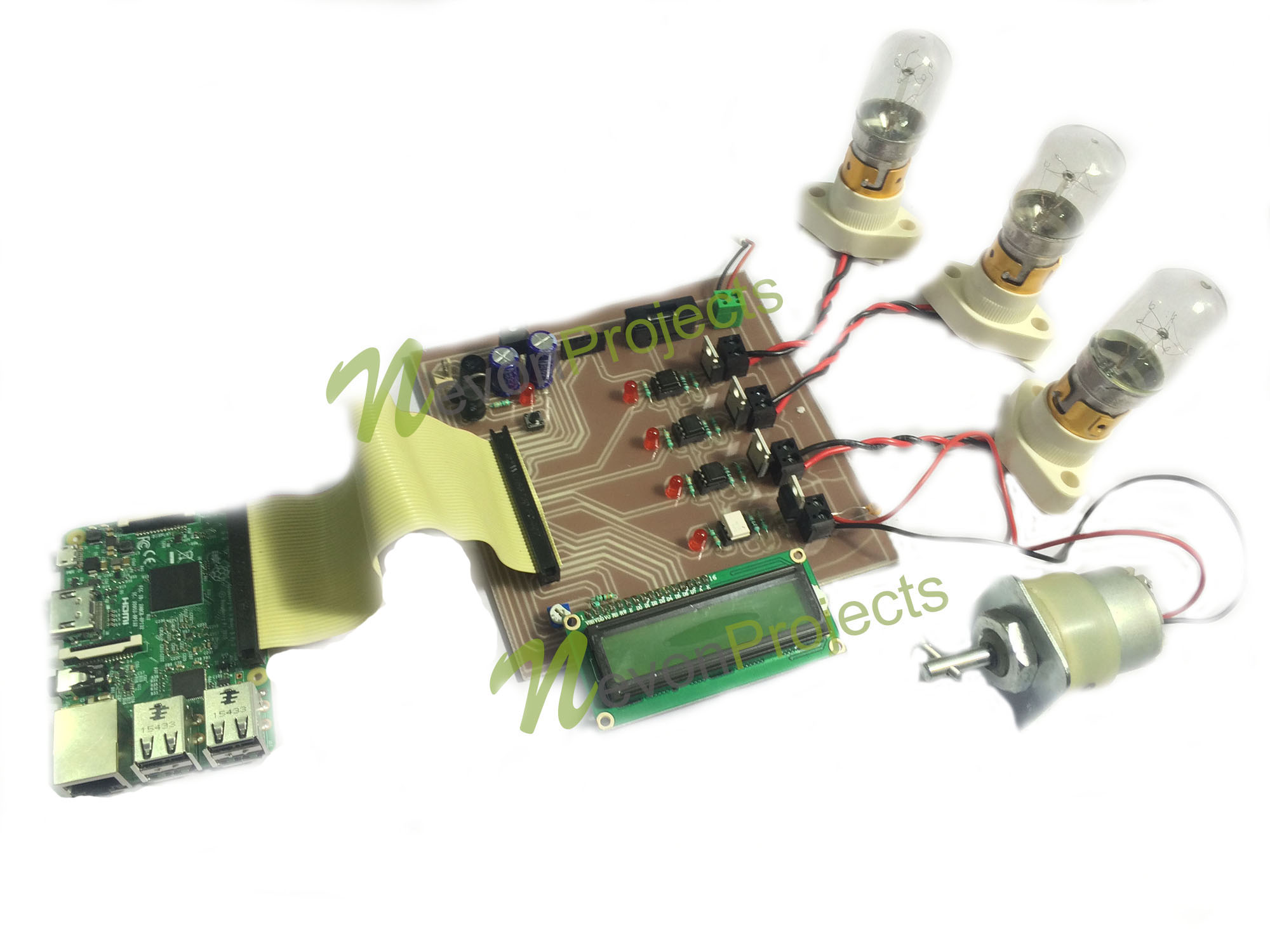
How To Securely Connect RemoteIoT VPC Raspberry Pi And Download Windows