Securing Remote Access Raspberry Pi: A Comprehensive Guide
Securing remote access Raspberry Pi is essential for maintaining the privacy and security of your data and network. As more people rely on remote access for their Raspberry Pi projects, ensuring proper security measures becomes increasingly important. This guide will provide you with a detailed understanding of the best practices and tools to secure your Raspberry Pi when accessed remotely.
Whether you're a hobbyist or a professional developer, remote access to your Raspberry Pi can significantly enhance productivity. However, without proper security, your device could become vulnerable to cyberattacks. This article will walk you through the steps needed to protect your Raspberry Pi while maintaining seamless remote access.
In this guide, you'll learn about various methods, tools, and configurations that can help secure your Raspberry Pi. From setting up firewalls to using secure protocols, we will cover everything you need to know to safeguard your device. Let's dive in and explore how you can protect your Raspberry Pi from potential threats.
- What Happened Toarah Goldberg American Idol
- Megan Ketch Actress
- Tony Hinchcliffeating
- Aunt Becky Full House
Table of Contents
- Introduction to Securing Remote Access Raspberry Pi
- Understanding the Risks of Unsecured Remote Access
- Setting Up SSH for Secure Remote Access
- Configuring a Firewall for Raspberry Pi
- Using Strong Passwords and Key Authentication
- Securing SSH Ports
- Essential Tools for Securing Remote Access
- Regularly Updating Your Raspberry Pi
- Securing Your Network
- Troubleshooting Common Security Issues
- Conclusion and Next Steps
Introduction to Securing Remote Access Raspberry Pi
Remote access to Raspberry Pi offers flexibility and convenience, allowing users to manage their devices from anywhere in the world. However, securing remote access Raspberry Pi is crucial to prevent unauthorized access and potential cyberattacks. In this section, we'll discuss the importance of security in remote access and provide an overview of the methods we'll explore in this guide.
Why Security Matters
Without proper security measures, your Raspberry Pi could become a target for hackers. Unauthorized access can lead to data breaches, system corruption, and even financial loss. By implementing the right security protocols, you can protect your device and maintain its integrity.
Understanding the Risks of Unsecured Remote Access
Unsecured remote access to Raspberry Pi can expose your device to several risks. These risks include unauthorized access, malware infections, and data theft. In this section, we'll delve into the potential threats and explain why securing remote access Raspberry Pi is a necessity.
Common Threats
- Brute-force attacks
- Malware and viruses
- Data breaches
- Network intrusions
By understanding these risks, you can take proactive steps to secure your Raspberry Pi and protect your data.
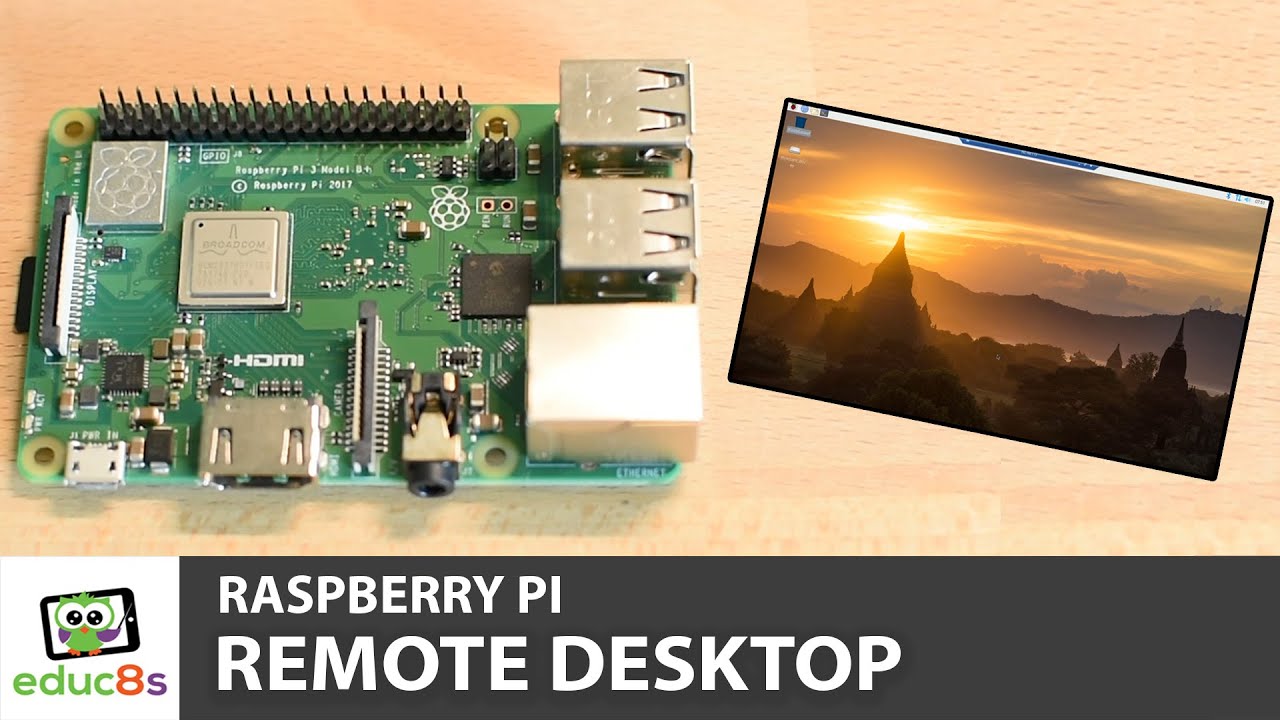
Setting Up SSH for Secure Remote Access
SSH (Secure Shell) is one of the most popular methods for securing remote access Raspberry Pi. It provides encrypted communication between your device and the remote client, ensuring that your data remains private and secure.
Steps to Set Up SSH
- Enable SSH on your Raspberry Pi
- Configure SSH settings in the terminal
- Test the connection using an SSH client
SSH is a powerful tool for securing remote access, and by following these steps, you can ensure that your Raspberry Pi remains protected.
Configuring a Firewall for Raspberry Pi
A firewall acts as a barrier between your Raspberry Pi and potential threats on the internet. By configuring a firewall, you can control incoming and outgoing traffic, further enhancing the security of your device.
Using UFW (Uncomplicated Firewall)
UFW is a user-friendly firewall management tool that simplifies the process of setting up a firewall on your Raspberry Pi. Here's how you can use UFW:
- Install UFW on your Raspberry Pi
- Allow necessary ports for SSH and other services
- Deny all other incoming connections
With UFW, you can easily configure a robust firewall that protects your Raspberry Pi from unauthorized access.
Using Strong Passwords and Key Authentication
Using strong passwords and key authentication is a fundamental step in securing remote access Raspberry Pi. Weak passwords can be easily guessed or cracked, making your device vulnerable to attacks.
Best Practices for Passwords
- Use a combination of letters, numbers, and symbols
- Avoid using common words or phrases
- Change passwords regularly
Key Authentication
Key authentication provides an additional layer of security by requiring a private key for access. This method eliminates the need for passwords and reduces the risk of brute-force attacks.
Securing SSH Ports
By default, SSH uses port 22 for communication. However, this port is commonly targeted by attackers. To enhance security, you can change the default SSH port and implement additional measures.
Steps to Change SSH Port
- Edit the SSH configuration file
- Change the port number to a non-standard value
- Restart the SSH service
Changing the SSH port can significantly reduce the risk of unauthorized access and improve the overall security of your Raspberry Pi.
Essential Tools for Securing Remote Access
There are several tools available that can help you secure remote access Raspberry Pi. These tools provide additional layers of protection and make it easier to manage your device's security.
Popular Security Tools
- Fail2Ban: Prevents brute-force attacks by banning IP addresses
- Fail2Ban: Monitors log files and blocks suspicious activity
- Log2Ram: Reduces wear on the SD card by storing logs in RAM
By utilizing these tools, you can further enhance the security of your Raspberry Pi and protect it from potential threats.
Regularly Updating Your Raspberry Pi
Keeping your Raspberry Pi up to date is crucial for maintaining its security. Software updates often include important security patches that address known vulnerabilities.
Steps to Update Your Raspberry Pi
- Run the update command in the terminal
- Install the latest packages and dependencies
- Reboot your Raspberry Pi to apply the changes
Regular updates ensure that your Raspberry Pi remains secure and protected from emerging threats.
Securing Your Network
Your Raspberry Pi's security is closely tied to the security of your network. By securing your network, you can further protect your device from potential threats.
Network Security Tips
- Use a strong Wi-Fi password
- Disable remote management on your router
- Enable network encryption (WPA3 if available)
A secure network is an essential component of securing remote access Raspberry Pi. By following these tips, you can create a safe environment for your device.
Troubleshooting Common Security Issues
Despite taking all necessary precautions, you may encounter security issues when securing remote access Raspberry Pi. In this section, we'll address common problems and provide solutions to help you resolve them.
Common Issues and Solutions
- SSH connection errors: Check firewall settings and ensure the correct port is open
- Failed login attempts: Verify your username and password, and ensure key authentication is properly configured
- Network connectivity problems: Restart your router and check network settings
By addressing these issues promptly, you can maintain the security of your Raspberry Pi and ensure uninterrupted remote access.
Conclusion and Next Steps
Securing remote access Raspberry Pi is a critical step in protecting your device and maintaining its integrity. By implementing the methods and tools discussed in this guide, you can significantly enhance the security of your Raspberry Pi and prevent unauthorized access.
We encourage you to take action by reviewing your current security setup and making the necessary improvements. Share your thoughts and experiences in the comments section below, and don't forget to explore other articles on our site for more valuable insights.
Stay safe and secure with your Raspberry Pi!

Remote Access Raspberry Pi Terminal
Raspberry Pi Libreelec Remote Access
Raspberry Pi remote access using Hexabitz Geeky Gadgets