Best SSH RemoteIoT: Unlocking Secure And Efficient IoT Connectivity
In the rapidly evolving world of technology, the concept of Best SSH RemoteIoT has become a focal point for both professionals and enthusiasts. Secure Shell (SSH) provides unparalleled security and reliability when managing remote devices, especially in the Internet of Things (IoT) landscape. As IoT continues to grow, understanding and implementing the best SSH practices for remote connectivity is essential for ensuring data integrity and system performance.
SSH RemoteIoT allows users to connect securely to IoT devices from anywhere in the world. This technology ensures encrypted communication, which is critical in protecting sensitive data. Whether you're a network administrator or a developer working on IoT projects, knowing the best practices and tools for SSH RemoteIoT can significantly enhance your operational efficiency.
This article aims to provide a comprehensive guide on Best SSH RemoteIoT, covering everything from its fundamental principles to advanced implementation strategies. By the end of this article, you'll have a clear understanding of how to leverage SSH for secure IoT management and connectivity.
Table of Contents
- Introduction to SSH RemoteIoT
- Why SSH is Important for IoT
- Best SSH RemoteIoT Tools
- Setting Up SSH for IoT Devices
- Securing SSH Connections
- Common SSH RemoteIoT Issues
- Best Practices for SSH RemoteIoT
- Advanced SSH RemoteIoT Configurations
- SSH RemoteIoT Use Cases
- Future of SSH in IoT
- Conclusion
Introduction to SSH RemoteIoT
Secure Shell (SSH) has long been the go-to protocol for secure remote access. When combined with IoT, SSH RemoteIoT becomes an indispensable tool for managing connected devices. This section provides an overview of what SSH RemoteIoT entails and why it is crucial in today's interconnected world.
SSH RemoteIoT allows administrators to connect to IoT devices securely, ensuring that data transmitted between devices remains encrypted and protected from unauthorized access. With billions of IoT devices expected to be online in the coming years, the importance of secure remote management cannot be overstated.
Why SSH is Important for IoT
The Internet of Things (IoT) brings with it a host of security challenges. Devices are often deployed in remote locations, making physical access impractical. SSH addresses this issue by providing a secure channel for remote management. Here are some reasons why SSH is vital for IoT:
- Encryption: SSH encrypts all data transmitted between devices, preventing eavesdropping and data theft.
- Authentication: SSH ensures that only authorized users can access IoT devices, reducing the risk of unauthorized access.
- Reliability: SSH is a robust protocol that works seamlessly across different platforms and environments.
Best SSH RemoteIoT Tools
Several tools are available for implementing SSH RemoteIoT. Below are two popular options that cater to different user needs:
Tool 1: PuTTY
PuTTY is a widely used SSH client that is both free and open-source. It supports various protocols, including SSH, and is compatible with Windows, Linux, and macOS. PuTTY's user-friendly interface makes it an excellent choice for beginners and experienced users alike.
Tool 2: SSH Client
Built-in SSH clients are available on most modern operating systems, including Linux and macOS. These clients provide a command-line interface for connecting to remote IoT devices. For users who prefer a more hands-on approach, these clients offer flexibility and customization options.
Setting Up SSH for IoT Devices
Setting up SSH for IoT devices involves several steps, including installing the necessary software, configuring security settings, and testing the connection. Below is a step-by-step guide:
- Install an SSH server on the IoT device.
- Configure the server to listen on the appropriate port (default is 22).
- Set up user authentication using passwords or public key cryptography.
- Test the connection using an SSH client.
Securing SSH Connections
While SSH provides a secure connection, additional measures can further enhance its security. These include:
- Disabling password authentication and using public key cryptography instead.
- Changing the default SSH port to a non-standard port.
- Implementing firewall rules to restrict access to the SSH server.
- Regularly updating the SSH server software to patch vulnerabilities.
Common SSH RemoteIoT Issues
Despite its robustness, SSH RemoteIoT can encounter issues. Some common problems include:
- Connection timeouts due to network instability.
- Authentication failures caused by incorrect credentials or misconfigured settings.
- Performance issues arising from high network latency.
Addressing these issues often involves troubleshooting the network configuration and ensuring that all components are properly set up.
Best Practices for SSH RemoteIoT
To maximize the effectiveness of SSH RemoteIoT, it's essential to follow best practices. These include:
- Regularly monitoring SSH connections for suspicious activity.
- Implementing role-based access control to limit user privileges.
- Documenting all SSH configurations and settings for easy reference.
Advanced SSH RemoteIoT Configurations
For users seeking more advanced configurations, SSH offers several options. These include:
- Setting up SSH tunnels for secure data transfer.
- Configuring SSH to use specific cipher suites for enhanced security.
- Implementing SSH key rotation policies to ensure long-term security.
SSH RemoteIoT Use Cases
SSH RemoteIoT finds applications in various industries, including:
- Smart homes: Managing connected devices such as smart thermostats and security systems.
- Industrial automation: Monitoring and controlling industrial equipment remotely.
- Healthcare: Ensuring secure communication between medical devices and healthcare providers.
Future of SSH in IoT
As IoT continues to expand, the role of SSH in securing remote connections will only grow. Future developments in SSH technology may include:
- Improved performance for low-power devices.
- Enhanced encryption algorithms to counter emerging threats.
- Integration with emerging technologies such as blockchain for added security.
Conclusion
In conclusion, Best SSH RemoteIoT is a powerful tool for managing IoT devices securely and efficiently. By understanding its principles and implementing best practices, users can ensure that their IoT deployments remain secure and reliable. We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and related technologies.
Data Source: SSH Official Website, IoT For All
The 7 Best SSH Clients for Linux
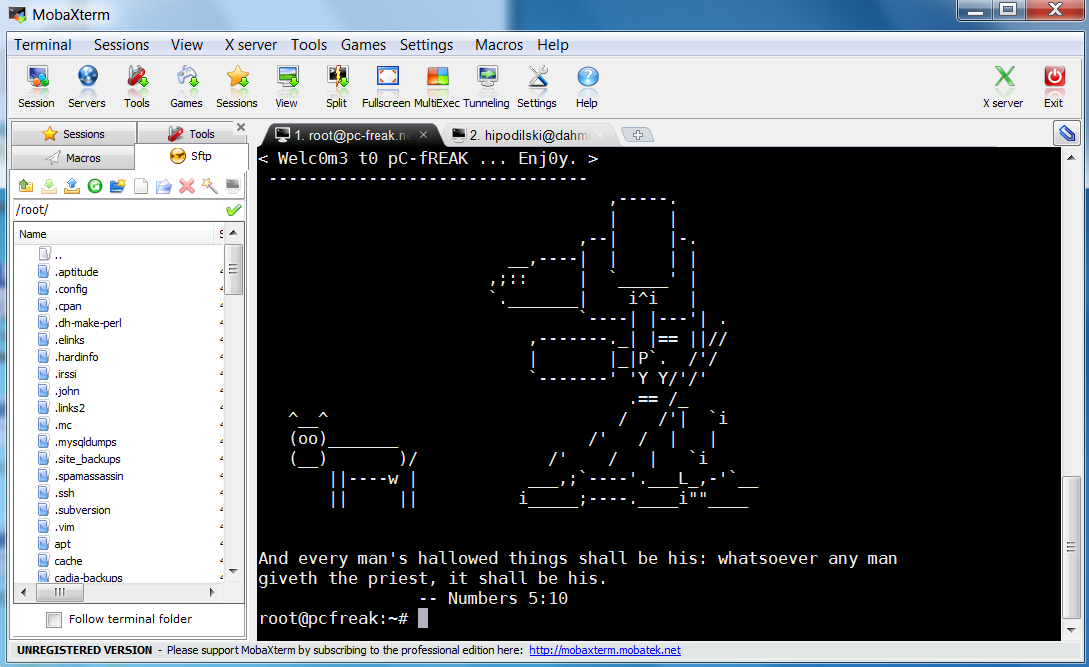
Best Ssh Client For Windows
10 best ssh clients for windows lasopamybest