Mastering RemoteIoT VPC SSH: A Comprehensive Guide To Secure And Efficient Access
In today's interconnected world, remote access to IoT devices through Virtual Private Cloud (VPC) using SSH has become an essential skill for IT professionals and system administrators. RemoteIoT VPC SSH allows secure communication between devices and networks, ensuring data privacy and system integrity. This article will delve deep into the concept, implementation, and best practices of RemoteIoT VPC SSH.
As businesses increasingly rely on IoT devices for operations, managing these devices remotely becomes crucial. Understanding how to set up and maintain a secure connection via RemoteIoT VPC SSH is vital for ensuring optimal performance and security. This guide aims to provide actionable insights for both beginners and advanced users alike.
By the end of this article, you will have a comprehensive understanding of RemoteIoT VPC SSH, its significance in modern IT infrastructure, and how to implement it effectively. Let’s get started!
Table of Contents
- Introduction to RemoteIoT VPC SSH
- Understanding VPC and SSH
- RemoteIoT VPC SSH Setup
- Security Best Practices
- Troubleshooting Common Issues
- Performance Optimization
- Use Cases of RemoteIoT VPC SSH
- Compliance and Regulations
- Tools and Resources
- Conclusion and Next Steps
Introduction to RemoteIoT VPC SSH
RemoteIoT VPC SSH is a powerful combination of technologies that enables secure access to IoT devices within a Virtual Private Cloud. This setup allows administrators to manage devices remotely while maintaining high levels of security and privacy. By leveraging SSH (Secure Shell), communication between devices and the cloud is encrypted, reducing the risk of unauthorized access.
Why RemoteIoT VPC SSH Matters
In an era where cyber threats are on the rise, securing IoT devices is no longer optional. RemoteIoT VPC SSH ensures that sensitive data transmitted between devices and the cloud remains protected. It also provides a centralized management system, simplifying operations for IT teams.
Key Benefits of Using RemoteIoT VPC SSH
- Enhanced security through encryption
- Centralized control over IoT devices
- Scalability to accommodate growing networks
- Reduced risk of data breaches
Understanding VPC and SSH
Before diving into RemoteIoT VPC SSH, it’s essential to understand the components that make it work: Virtual Private Cloud (VPC) and SSH.
What is a Virtual Private Cloud (VPC)?
A Virtual Private Cloud is a private network within a public cloud environment. It allows users to create isolated environments for their applications and devices, ensuring that they are not exposed to the public internet. VPCs provide features such as subnets, routing tables, and network gateways, enabling fine-grained control over network traffic.
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol that secures communication between devices over an unsecured network. It provides authentication and encryption, ensuring that data transmitted between devices cannot be intercepted or tampered with. SSH is widely used for remote access and command execution.
RemoteIoT VPC SSH Setup
Setting up RemoteIoT VPC SSH involves several steps, from configuring the VPC to establishing SSH connections. Below is a step-by-step guide:
Step 1: Create a VPC
Begin by creating a VPC in your preferred cloud provider. Define subnets, routing tables, and security groups to ensure proper isolation and access control.
Step 2: Configure IoT Devices
Provision your IoT devices with the necessary credentials and settings to connect to the VPC. Ensure that they are configured to use SSH for communication.
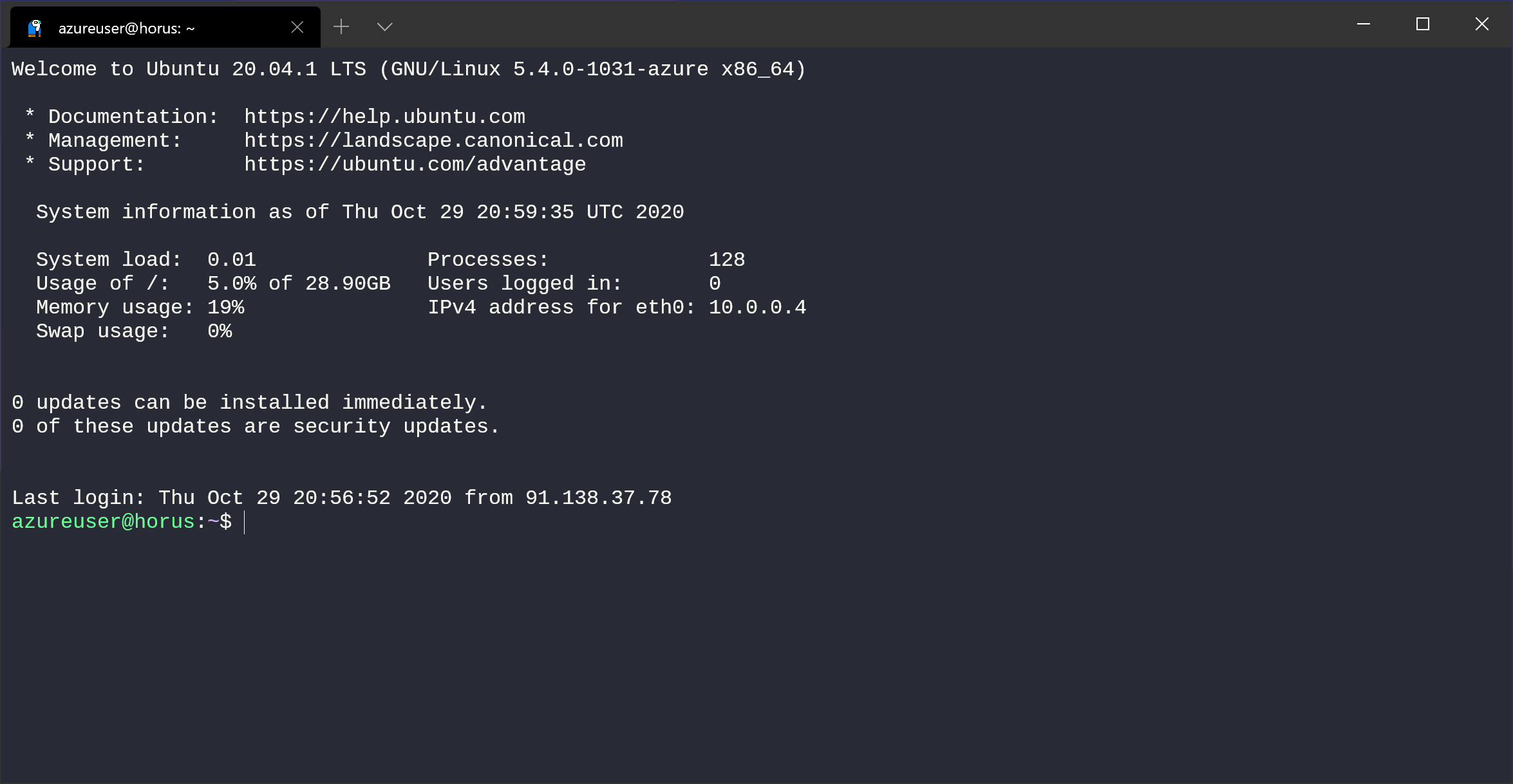
Step 3: Establish SSH Connections
Use SSH clients or tools to establish secure connections between your devices and the VPC. Test the connection to ensure that data is transmitted securely.
Security Best Practices
While RemoteIoT VPC SSH offers robust security, adhering to best practices is crucial to maximize protection. Here are some recommendations:
- Use strong, unique passwords for SSH access
- Enable two-factor authentication (2FA) for added security
- Regularly update and patch devices and software
- Monitor network traffic for suspicious activity
Common Security Threats
Understanding potential threats is the first step in mitigating them. Common threats include brute-force attacks, man-in-the-middle attacks, and unauthorized access. Implementing the above best practices can significantly reduce the risk of these threats.
Troubleshooting Common Issues
Even with careful setup, issues can arise when using RemoteIoT VPC SSH. Below are some common problems and their solutions:
Issue 1: Unable to Connect via SSH
Solution: Check your firewall settings and ensure that the correct ports are open. Verify that the SSH service is running on the target device.
Issue 2: Slow Connection Speeds
Solution: Optimize your VPC configuration and ensure that network latency is minimized. Consider using a Content Delivery Network (CDN) if applicable.
Performance Optimization
To ensure optimal performance of your RemoteIoT VPC SSH setup, consider the following strategies:
- Use compression to reduce data transfer times
- Implement load balancing for distributed workloads
- Regularly monitor and analyze performance metrics
Tools for Performance Monitoring
Several tools can help you monitor and optimize performance. Examples include:
- Prometheus
- Grafana
- CloudWatch
Use Cases of RemoteIoT VPC SSH
RemoteIoT VPC SSH has numerous applications across various industries. Below are some notable use cases:
- Remote monitoring of industrial equipment
- Secure access to healthcare devices
- Centralized management of smart home systems
Industry-Specific Applications
Each industry has unique requirements and challenges. Tailoring RemoteIoT VPC SSH solutions to specific needs can enhance efficiency and security.
Compliance and Regulations
When implementing RemoteIoT VPC SSH, compliance with relevant regulations is critical. Ensure that your setup adheres to standards such as:
- GDPR (General Data Protection Regulation)
- HIPAA (Health Insurance Portability and Accountability Act)
- ISO 27001
Importance of Compliance
Failing to comply with regulations can result in severe penalties and damage to reputation. Regular audits and updates to your security policies can help maintain compliance.
Tools and Resources
Several tools and resources can assist in implementing and managing RemoteIoT VPC SSH:
- AWS VPC: A comprehensive solution for creating and managing VPCs
- OpenSSH: A widely used SSH implementation
- Terraform: A tool for automating infrastructure deployment
Learning Resources
For those looking to deepen their knowledge, consider the following resources:
- Official documentation from cloud providers
- Online courses and tutorials
- Community forums and discussion boards
Conclusion and Next Steps
RemoteIoT VPC SSH is a vital technology for securing and managing IoT devices in today’s digital landscape. By understanding its components, implementing best practices, and leveraging available tools, you can ensure a secure and efficient setup.
Take Action: Share your thoughts and experiences in the comments below. Explore other articles on our site for more insights into IoT and cloud technologies. Together, let’s build a safer and more connected world!

RemoteIoT VPC SSH Raspberry Pi Download Free A Comprehensive Guide
Mastering RemoteIoT VPC SSH On Windows 10 Without Complications

Mastering RemoteIoT VPC SSH On Windows 10 Without Complications