Unlock The Power Of RemoteIoT Web SSH For Seamless Remote Access
In today's digital landscape, remote IoT (Internet of Things) management has become a crucial aspect of modern technology. RemoteIoT Web SSH offers a secure and efficient solution for managing IoT devices from anywhere in the world. Whether you're a developer, system administrator, or IT professional, understanding how RemoteIoT Web SSH works can significantly enhance your ability to manage connected devices effectively.
The increasing number of IoT devices in homes, businesses, and industries demands robust solutions for remote management. RemoteIoT Web SSH bridges the gap by providing a secure platform to access and control IoT devices via web-based SSH (Secure Shell) protocols. This technology ensures that users can manage their devices without compromising security or performance.
As we delve deeper into this topic, you'll discover how RemoteIoT Web SSH revolutionizes remote device management, its benefits, potential challenges, and best practices for implementation. Let's explore how this technology can transform the way you interact with IoT devices.
What is RemoteIoT Web SSH?
RemoteIoT Web SSH is a cutting-edge solution that combines the power of IoT with secure shell (SSH) protocols to provide seamless remote access to connected devices. This technology allows users to manage IoT devices through a web interface, eliminating the need for physical access or complex configurations. By leveraging SSH encryption, RemoteIoT Web SSH ensures secure communication between devices and users.
The growing demand for remote device management has led to the development of innovative solutions like RemoteIoT Web SSH. According to a report by Statista, the global IoT market is projected to reach $1.1 trillion by 2026, highlighting the importance of secure and efficient remote management tools.
How Does RemoteIoT Web SSH Work?
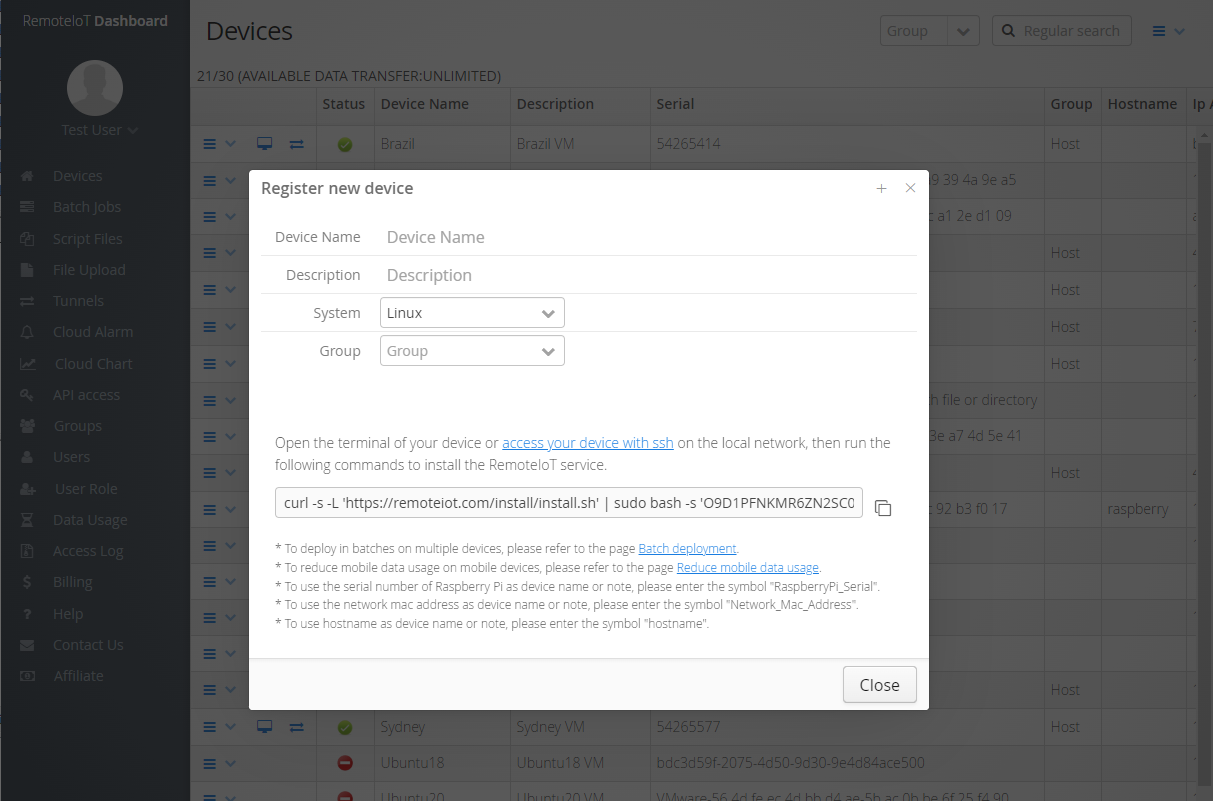
RemoteIoT Web SSH operates by establishing a secure connection between the user's web browser and the target IoT device. This connection is facilitated through SSH protocols, which encrypt data transmissions and protect sensitive information from unauthorized access. The process involves the following steps:
- Dave Portnoy Wife
- Heineken De Botella De Vidrio Sabe Mejor
- Austin Butler And Kaia Gerber
- Where Iynthia Rhodes Today
- User accesses the RemoteIoT Web SSH interface through a web browser
- The system authenticates the user using secure credentials
- A secure SSH tunnel is established between the user and the target device
- Users can now manage and control the IoT device remotely
Benefits of Using RemoteIoT Web SSH
Implementing RemoteIoT Web SSH offers numerous advantages for individuals and organizations managing IoT devices. Below are some key benefits:
Enhanced Security
RemoteIoT Web SSH utilizes advanced encryption techniques to protect data transmissions, ensuring that sensitive information remains secure during remote sessions. This level of security is crucial in today's threat landscape, where cyberattacks on IoT devices are becoming increasingly common.
Improved Accessibility
With RemoteIoT Web SSH, users can access and manage IoT devices from anywhere in the world using a standard web browser. This eliminates the need for specialized software or hardware, making it easier for teams to collaborate and manage devices remotely.
Cost-Effective Solution
RemoteIoT Web SSH reduces the need for on-site visits and maintenance, resulting in significant cost savings for businesses. Additionally, the platform's scalability allows organizations to manage a growing number of IoT devices without incurring additional expenses.
Challenges and Considerations
While RemoteIoT Web SSH offers many benefits, there are some challenges and considerations to keep in mind when implementing this technology:
Network Latency
RemoteIoT Web SSH performance can be affected by network latency, especially when managing devices across long distances. To mitigate this issue, users should ensure they have a stable and high-speed internet connection.
Authentication and Authorization
Implementing robust authentication and authorization mechanisms is crucial to prevent unauthorized access to IoT devices. RemoteIoT Web SSH supports various authentication methods, including multi-factor authentication (MFA) and public key infrastructure (PKI).
Best Practices for Implementing RemoteIoT Web SSH
To maximize the benefits of RemoteIoT Web SSH, consider the following best practices:
- Regularly update firmware and software to ensure devices are protected against vulnerabilities
- Use strong passwords and enable multi-factor authentication for added security
- Monitor device activity and set up alerts for suspicious behavior
- Implement network segmentation to isolate IoT devices from critical systems
RemoteIoT Web SSH Use Cases
RemoteIoT Web SSH finds applications in various industries, including:
Smart Homes
Homeowners can use RemoteIoT Web SSH to manage smart home devices, such as thermostats, security cameras, and lighting systems, from anywhere in the world.
Industrial IoT
In the industrial sector, RemoteIoT Web SSH enables engineers and technicians to monitor and control machinery and equipment remotely, improving efficiency and reducing downtime.
Comparison with Other Remote Access Solutions
When evaluating remote access solutions for IoT devices, it's essential to compare RemoteIoT Web SSH with other technologies. Some popular alternatives include:
VPN (Virtual Private Network)
VPNs provide secure remote access to networks but can be complex to set up and maintain. RemoteIoT Web SSH offers a simpler and more user-friendly solution for managing IoT devices.
SSH Clients
Traditional SSH clients require users to install software on their devices, whereas RemoteIoT Web SSH operates through a web browser, eliminating the need for additional software.
Future Trends in RemoteIoT Web SSH
The evolution of IoT technology will continue to drive innovation in remote access solutions like RemoteIoT Web SSH. Some emerging trends include:
Edge Computing
Edge computing enables data processing closer to the source, reducing latency and improving performance for remote IoT device management.
Artificial Intelligence and Machine Learning
Integrating AI and machine learning into RemoteIoT Web SSH can enhance predictive maintenance capabilities and improve overall system efficiency.
Daftar Isi
- What is RemoteIoT Web SSH?
- How Does RemoteIoT Web SSH Work?
- Benefits of Using RemoteIoT Web SSH
- Challenges and Considerations
- Best Practices for Implementing RemoteIoT Web SSH
- RemoteIoT Web SSH Use Cases
- Comparison with Other Remote Access Solutions
- Future Trends in RemoteIoT Web SSH
- Conclusion
Conclusion
RemoteIoT Web SSH represents a significant advancement in remote IoT device management, offering enhanced security, improved accessibility, and cost-effective solutions for individuals and organizations. By understanding the benefits, challenges, and best practices associated with this technology, you can effectively implement RemoteIoT Web SSH to manage your IoT devices.
We encourage you to share your thoughts and experiences with RemoteIoT Web SSH in the comments section below. Additionally, feel free to explore other articles on our website to learn more about IoT technology and its applications.
Data Sources:
- Statista - Global IoT Market Projection
- NIST - IoT Security Guidelines
- IEEE - Remote Access Solutions for IoT Devices
How to remotely ssh iot device in web browser

RemoteIoT Web SSH Raspberry Pi Unlocking Remote Access And Management
RemoteIoT Web SSH Download A Comprehensive Guide To Secure Remote Access