Comprehensive SSH Remote IoT Device Tutorial: A Step-by-Step Guide
SSH (Secure Shell) is an essential tool for managing remote IoT devices securely and efficiently. As the Internet of Things (IoT) continues to expand, understanding how to use SSH for remote access becomes increasingly important for developers, administrators, and hobbyists alike. This tutorial will walk you through the process of setting up and managing SSH connections to IoT devices.
In today's interconnected world, IoT devices play a critical role in various industries, from smart homes to industrial automation. However, managing these devices remotely can be challenging without the right tools. SSH provides a secure and reliable way to access and control IoT devices from anywhere in the world.
This comprehensive tutorial is designed for beginners and experienced users alike. Whether you're setting up your first IoT device or looking to enhance your remote management skills, this guide will provide you with the knowledge and tools you need to succeed.
Table of Contents
- Introduction to SSH
- Why Use SSH for IoT Devices?
- Prerequisites
- Setting Up an SSH Server
- Connecting to an IoT Device
- Securing Your SSH Connection
- Common SSH Commands
- Troubleshooting Tips
- Advanced SSH Features
- Conclusion
Introduction to SSH
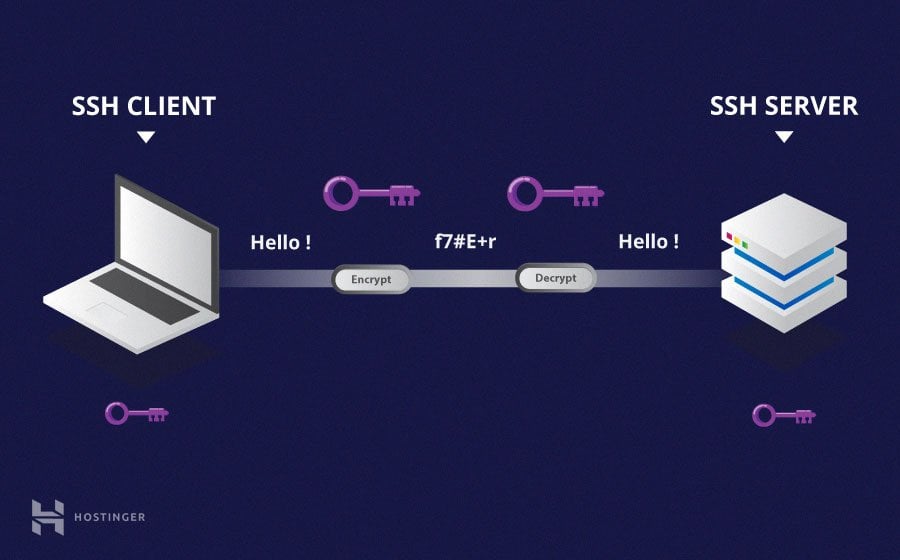
SSH, or Secure Shell, is a network protocol that allows users to securely access remote computers and servers. It encrypts all data transmitted between the client and server, ensuring that sensitive information remains private and secure. For IoT devices, SSH is particularly useful because it provides a secure channel for managing and monitoring devices over the internet.
SSH operates on port 22 by default and supports various authentication methods, including password-based and public-key authentication. This flexibility makes SSH suitable for a wide range of applications, from simple remote access to complex automation tasks.
Why Use SSH for IoT Devices?
Using SSH for IoT devices offers several advantages:
- Security: SSH encrypts all communication, protecting your data from unauthorized access.
- Reliability: SSH connections are stable and can be configured to handle network interruptions gracefully.
- Flexibility: SSH supports a wide range of commands and tools, making it suitable for both basic and advanced tasks.
- Compatibility: SSH is supported by virtually all modern operating systems, including Linux, macOS, and Windows.
Prerequisites
Before proceeding with this tutorial, ensure you have the following:
- A computer or laptop with SSH client installed (most modern systems include SSH by default).
- An IoT device running a Linux-based operating system (e.g., Raspberry Pi with Raspbian).
- A stable internet connection for both your local machine and the IoT device.
- Basic knowledge of Linux commands and terminal usage.
Setting Up an SSH Server
Installing SSH Server on Your IoT Device
To enable SSH on your IoT device, you need to install and configure an SSH server. Most Linux-based IoT devices come with OpenSSH pre-installed. If not, you can install it using the following command:
sudo apt-get update && sudo apt-get install openssh-server
Configuring SSH Server
Once installed, you can configure the SSH server by editing the configuration file:
sudo nano /etc/ssh/sshd_config
Some important settings to consider include:
- Port: Change the default port (22) to enhance security.
- PasswordAuthentication: Disable password-based authentication to improve security.
- PermitRootLogin: Restrict root login to prevent unauthorized access.
Connecting to an IoT Device
Using SSH Client
Connecting to your IoT device using SSH is straightforward. Open a terminal on your local machine and type the following command:
ssh username@ip_address
Replace "username" with the actual username on your IoT device and "ip_address" with the device's IP address.
Verifying Connection
Once connected, you can verify the connection by running a simple command, such as:
uname -a
This command displays the kernel version and system information, confirming that you are connected to the correct device.
Securing Your SSH Connection
Using Public-Key Authentication
Public-key authentication is a more secure alternative to password-based authentication. To set it up:
- Generate a key pair on your local machine:
ssh-keygen -t rsa - Copy the public key to your IoT device:
ssh-copy-id username@ip_address - Disable password authentication in the SSH configuration file.
Implementing Firewall Rules
Configure your firewall to restrict SSH access to trusted IP addresses. For example, using ufw on a Linux system:
sudo ufw allow from trusted_ip/32 to any port ssh
Common SSH Commands
Here are some commonly used SSH commands:
- ssh username@ip_address: Connect to a remote device.
- scp file_name username@ip_address:/destination: Copy files securely.
- ssh-keygen: Generate SSH keys for public-key authentication.
- ssh-copy-id: Copy public key to a remote server.
Troubleshooting Tips
Here are some tips to help you troubleshoot common SSH issues:
- Check if the SSH service is running on the IoT device:
sudo systemctl status ssh. - Verify the IP address and port number in your SSH command.
- Ensure that the firewall allows SSH traffic on the specified port.
- Review the SSH configuration file for any errors or misconfigurations.
Advanced SSH Features
Tunneling
SSH tunneling allows you to securely forward traffic between your local machine and a remote server. This is particularly useful for accessing services that are not publicly accessible.
SSH Multiplexing
SSH multiplexing enables you to reuse existing connections, reducing the overhead of establishing new connections. To enable multiplexing, add the following lines to your SSH configuration file:
ControlMaster auto
ControlPath ~/.ssh/controlmasters/%r@%h:%p
Conclusion
In this tutorial, we explored the basics of SSH and its application in managing remote IoT devices. We covered everything from setting up an SSH server to securing your connections and troubleshooting common issues. By following the steps outlined in this guide, you can effectively manage your IoT devices from anywhere in the world.
We encourage you to experiment with the advanced features of SSH and share your experiences in the comments below. Additionally, don't forget to explore other tutorials on our website for more insights into IoT and network management.
Thank you for reading, and happy coding!
SSH Tutorial What is SSH, Encryptions and Ports
RemoteIoT Device SSH Tutorial A Comprehensive Guide For Secure Remote

SSH RemoteIoT Device Tutorial A Comprehensive Guide To Secure Remote