Best RemoteIoT Firewall Examples: Securing Your IoT Network
In today's interconnected world, the Internet of Things (IoT) has revolutionized the way we interact with technology. However, with the growing number of IoT devices, security concerns have become more critical than ever. Implementing a reliable remoteIoT firewall is essential to protect your network from potential cyber threats.
The rise of remote work and distributed networks has made it imperative for businesses to adopt robust security measures. A remoteIoT firewall acts as a protective barrier, ensuring unauthorized access is blocked while safeguarding sensitive data. As cyberattacks become more sophisticated, understanding the best remoteIoT firewall examples can help organizations enhance their security posture.
This article will explore various remoteIoT firewall solutions, their features, and how they contribute to securing IoT networks. By the end of this guide, you'll have a clear understanding of the importance of firewalls in IoT ecosystems and the best options available in the market.
- Shawn Michaels Children
- Zac Brown Weight Loss F1
- Caroline Stanbury Wealth
- The Challenge Rise Of A New Champion
Table of Contents:
- Introduction to RemoteIoT Firewall
- Why RemoteIoT Firewall is Necessary
- Top RemoteIoT Firewall Examples
- Features of RemoteIoT Firewalls
- Benefits of Using a RemoteIoT Firewall
- How to Select the Right Firewall
- Common RemoteIoT Security Challenges
- Best Practices for RemoteIoT Security
- Future Trends in RemoteIoT Security
- Conclusion
Introduction to RemoteIoT Firewall
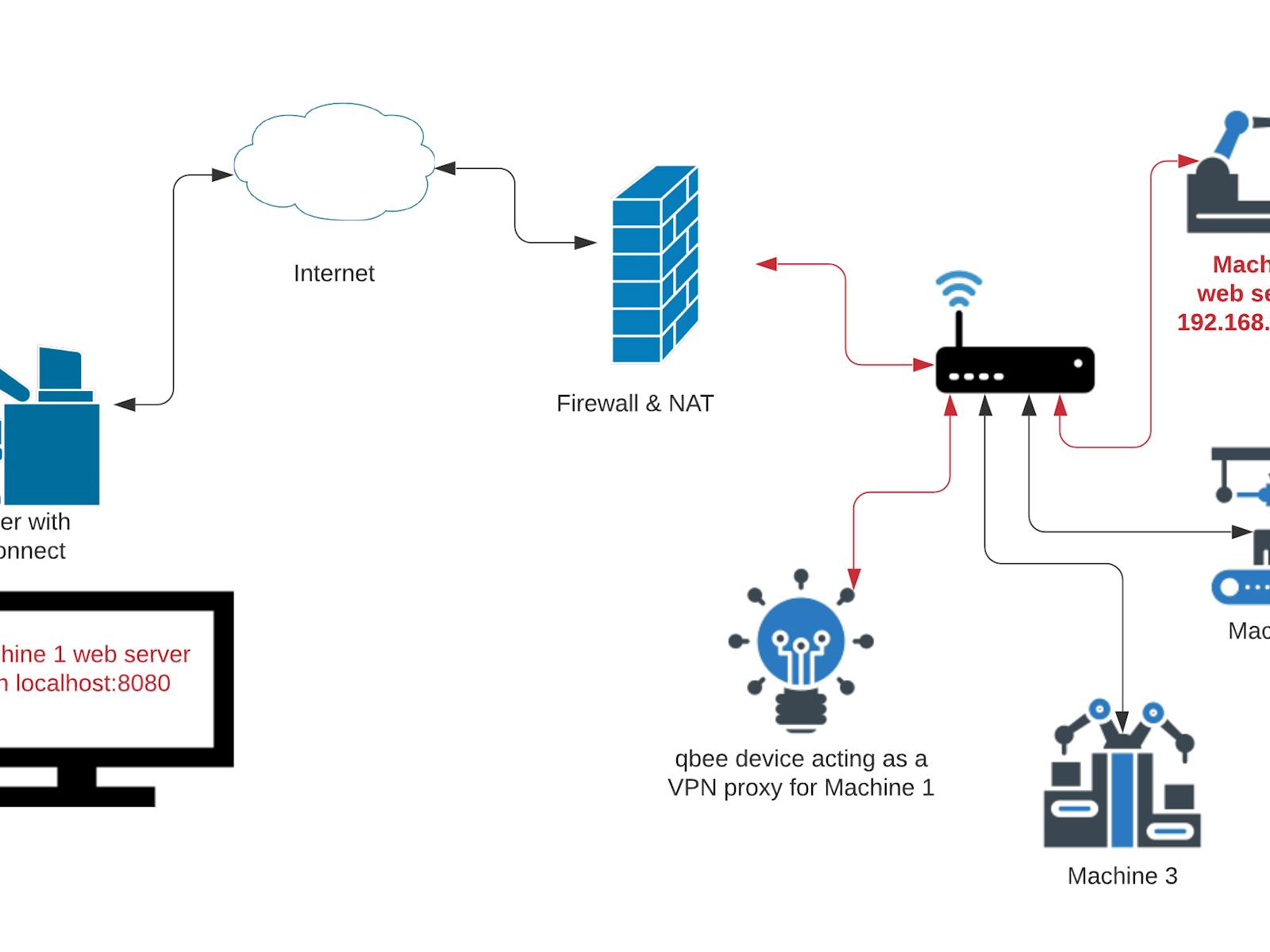
A remoteIoT firewall is a specialized security solution designed to protect IoT devices and networks from unauthorized access, malware, and other cyber threats. Unlike traditional firewalls, remoteIoT firewalls are tailored to address the unique challenges posed by IoT ecosystems. These firewalls provide an additional layer of security, ensuring that only trusted devices and users can access the network.
As IoT devices continue to proliferate, the need for robust security measures becomes increasingly important. RemoteIoT firewalls play a crucial role in safeguarding sensitive data and maintaining the integrity of IoT networks. By filtering incoming and outgoing traffic, these firewalls help prevent malicious activities and ensure secure communication between devices.
Understanding IoT Security
IoT security is a multifaceted challenge that requires a comprehensive approach. RemoteIoT firewalls are just one component of a broader security strategy. To effectively protect IoT networks, organizations must implement a combination of firewalls, encryption protocols, and regular security audits.
Why RemoteIoT Firewall is Necessary
IoT devices are often deployed in remote locations, making them vulnerable to cyberattacks. Without proper security measures, these devices can become entry points for hackers to infiltrate networks and access sensitive information. A remoteIoT firewall is essential for addressing these vulnerabilities and ensuring the security of IoT ecosystems.
Some of the key reasons why remoteIoT firewalls are necessary include:
- Protection against unauthorized access
- Prevention of malware and cyberattacks
- Monitoring and filtering network traffic
- Enhancing overall network security
Key Statistics on IoT Security
According to a recent report by Gartner, the global IoT security market is expected to reach $3.1 billion by 2023. This growth is driven by the increasing demand for secure IoT solutions, particularly in industries such as healthcare, manufacturing, and smart cities.
Top RemoteIoT Firewall Examples
Several remoteIoT firewall solutions are available in the market, each offering unique features and capabilities. Below are some of the best remoteIoT firewall examples:
1. Fortinet FortiGate
FortiGate is a leading remoteIoT firewall solution that provides comprehensive security for IoT networks. It offers advanced threat protection, application control, and real-time monitoring to ensure secure communication between devices.
2. Palo Alto Networks
Palo Alto Networks offers a robust remoteIoT firewall solution that combines next-generation firewall capabilities with IoT-specific security features. Its platform supports automated threat detection and response, making it ideal for large-scale IoT deployments.
3. Check Point IoT Protection
Check Point IoT Protection is a powerful remoteIoT firewall solution that provides end-to-end security for IoT devices. It includes features such as device profiling, threat prevention, and centralized management, ensuring seamless integration with existing security infrastructure.
Features of RemoteIoT Firewalls
RemoteIoT firewalls are equipped with a range of features designed to enhance IoT security. Some of the key features include:
- Real-time threat detection and response
- Advanced traffic filtering and monitoring
- Device profiling and classification
- Centralized management and reporting
- Integration with cloud-based security solutions
Advanced Threat Detection
One of the standout features of remoteIoT firewalls is their ability to detect and respond to threats in real-time. By leveraging machine learning and artificial intelligence, these firewalls can identify suspicious activities and take proactive measures to mitigate potential risks.
Benefits of Using a RemoteIoT Firewall
Implementing a remoteIoT firewall offers numerous benefits for organizations looking to enhance their IoT security. Some of the key advantages include:
- Improved network visibility and control
- Reduced risk of cyberattacks and data breaches
- Enhanced compliance with industry regulations
- Increased operational efficiency and reliability
Compliance with Industry Standards
RemoteIoT firewalls help organizations comply with industry standards and regulations such as GDPR, HIPAA, and ISO 27001. By ensuring secure communication and data protection, these firewalls play a vital role in maintaining regulatory compliance.
How to Select the Right Firewall
Choosing the right remoteIoT firewall requires careful consideration of several factors. Below are some key considerations to keep in mind:
- Scalability and flexibility to accommodate growing IoT deployments
- Compatibility with existing security infrastructure
- Support for advanced threat detection and response
- Cost-effectiveness and return on investment
Assessing Scalability
When selecting a remoteIoT firewall, it's important to assess its scalability to ensure it can handle future growth. Look for solutions that offer modular architecture and seamless integration with cloud-based platforms to support expanding IoT networks.
Common RemoteIoT Security Challenges
Securing remoteIoT networks presents several challenges, including:
- Limited device resources and processing power
- Inconsistent security protocols across devices
- Difficulty in monitoring and managing large-scale deployments
Device Resource Limitations
Many IoT devices have limited resources, making it challenging to implement robust security measures. RemoteIoT firewalls address this issue by offloading security tasks to centralized servers, ensuring efficient resource utilization.
Best Practices for RemoteIoT Security
To maximize the effectiveness of remoteIoT firewalls, organizations should adopt the following best practices:
- Regularly update firmware and security patches
- Implement strong authentication and access controls
- Conduct regular security audits and vulnerability assessments
- Educate employees about IoT security best practices
Regular Security Audits
Conducting regular security audits is essential for identifying vulnerabilities and addressing potential risks. By performing thorough assessments, organizations can ensure their remoteIoT firewalls are functioning optimally and providing adequate protection.
Future Trends in RemoteIoT Security
The future of remoteIoT security is shaped by emerging technologies and trends such as:
- Artificial intelligence and machine learning for threat detection
- Blockchain for secure device authentication
- Quantum cryptography for advanced encryption
Artificial Intelligence in IoT Security
AI-powered remoteIoT firewalls are becoming increasingly popular due to their ability to analyze vast amounts of data and detect anomalies in real-time. By leveraging AI, organizations can enhance their security posture and stay ahead of evolving cyber threats.
Conclusion
Implementing a reliable remoteIoT firewall is crucial for securing IoT networks and protecting sensitive data. By understanding the best remoteIoT firewall examples and adopting best practices, organizations can enhance their security posture and ensure the integrity of their IoT ecosystems.
We encourage readers to share their thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into IoT security and related topics. Together, we can build a safer and more secure digital future.
- Pittsburgh Steelers Playoff Appearances
- Whyoes Julian Mcmahon Walk Funny
- Mariana Hill
- Elizabeth Tayloroneath

RemoteIoT Behind Firewall Examples A Comprehensive Guide To Secure
RemoteIoT Behind Firewall Examples A Comprehensive Guide To Secure

Firewall Policy Design, Configuration, and Examples ENP