IoT SSH Download AWS: A Comprehensive Guide To Secure Your Connected Devices
IoT SSH download AWS has become an increasingly essential topic as the Internet of Things (IoT) continues to grow in popularity. With billions of devices now connected globally, ensuring secure communication and management is crucial for both individuals and businesses. AWS provides robust tools and services to help users implement secure shell (SSH) connections for their IoT devices, making it easier than ever to manage and protect them.
The integration of SSH in IoT through AWS ensures that your devices remain secure and protected from unauthorized access. This article will provide a detailed overview of the process, including step-by-step instructions, best practices, and expert tips to help you effectively download and configure SSH on AWS for IoT devices.
As cybersecurity threats continue to evolve, understanding how to secure your IoT devices using SSH and AWS is more important than ever. This guide will equip you with the knowledge and tools necessary to protect your data and ensure seamless communication between devices.
Table of Contents
- Introduction to IoT
- Understanding SSH
- Why Use AWS for IoT
- IoT SSH Download AWS Process
- Security Best Practices
- Common Issues and Troubleshooting
- Advanced Features
- Cost Considerations
- Future Trends
- Conclusion
Introduction to IoT
The Internet of Things (IoT) refers to the network of physical devices, vehicles, home appliances, and other items embedded with sensors, software, and connectivity that enable them to exchange data. According to a report by Statista, the number of IoT devices is expected to surpass 25 billion by 2025. This exponential growth highlights the importance of secure communication and management solutions.
Key Characteristics of IoT
- Interconnectivity: Devices communicate seamlessly with each other.
- Automation: Many IoT devices operate autonomously, reducing the need for manual intervention.
- Data Collection: IoT devices gather vast amounts of data, which can be analyzed to improve efficiency and decision-making.
Understanding SSH
Secure Shell (SSH) is a cryptographic protocol used to secure communication between devices over an unsecured network. It provides encryption for data transmission, authentication, and integrity checks, making it an essential tool for managing IoT devices securely.
Benefits of Using SSH
- Encryption: Protects data from eavesdropping and interception.
- Authentication: Ensures that only authorized users can access the devices.
- Integrity: Verifies that the data transmitted has not been altered during transit.
Why Use AWS for IoT
Amazon Web Services (AWS) offers a comprehensive suite of tools and services specifically designed for IoT applications. AWS IoT Core, for example, allows users to connect devices easily, manage them at scale, and interact with cloud applications securely.
Key advantages of using AWS for IoT include:
- Scalability: AWS can handle millions of devices and trillions of messages.
- Security: Built-in security features ensure that devices and data remain protected.
- Integration: AWS IoT integrates seamlessly with other AWS services, such as Lambda, S3, and DynamoDB.
IoT SSH Download AWS Process
Downloading and configuring SSH on AWS for IoT devices involves several steps. Below is a detailed guide to help you through the process:
Step 1: Set Up an AWS Account
Create an AWS account if you don't already have one. This will give you access to all AWS services, including those needed for IoT.
Step 2: Install AWS CLI
Install the AWS Command Line Interface (CLI) on your local machine. This tool allows you to interact with AWS services from the command line.
Step 3: Configure AWS IoT Core
Set up AWS IoT Core to manage your devices. This involves creating certificates, policies, and rules to ensure secure communication.
Step 4: Download and Install SSH
Download and install an SSH client on your device. Popular options include PuTTY for Windows and OpenSSH for Linux and macOS.
Step 5: Connect to Your IoT Device
Use the SSH client to connect to your IoT device via its IP address or hostname. Ensure that the necessary ports are open and configured correctly.
Security Best Practices
Implementing strong security measures is crucial when managing IoT devices with SSH on AWS. Below are some best practices to consider:
- Use strong, unique passwords for all devices and accounts.
- Enable two-factor authentication (2FA) wherever possible.
- Regularly update firmware and software to patch vulnerabilities.
- Monitor device activity for any suspicious behavior.
Common Issues and Troubleshooting
Despite careful planning, issues may arise during the IoT SSH download AWS process. Here are some common problems and their solutions:
Connection Errors
If you encounter connection errors, verify that the device's IP address and port are correct. Check firewalls and network settings to ensure they allow SSH traffic.
Authentication Failures
Authentication failures can occur due to incorrect credentials or misconfigured policies. Double-check your certificates and ensure that the correct permissions are set.
Advanced Features
AWS offers several advanced features to enhance the management and security of IoT devices. These include:
- Device Shadowing: Allows you to synchronize device state information between the cloud and the device.
- Rules Engine: Enables automated actions based on device data and events.
- Over-the-Air Updates: Facilitates the deployment of updates to devices without manual intervention.
Cost Considerations
While AWS provides a free tier for many of its services, costs can add up as usage increases. It's important to monitor your usage and adjust settings accordingly to avoid unexpected expenses. AWS offers detailed billing reports and cost management tools to help you stay within budget.
Future Trends
The future of IoT SSH download AWS looks promising, with advancements in technology driving innovation. Some trends to watch include:
- Increased adoption of edge computing to reduce latency and improve performance.
- Enhanced security measures to combat rising cyber threats.
- Integration with artificial intelligence (AI) and machine learning (ML) for smarter decision-making.
Conclusion
In conclusion, securing IoT devices using SSH on AWS is a critical step in ensuring their safe and efficient operation. By following the steps outlined in this guide and implementing best practices, you can protect your devices and data from potential threats. We encourage you to share your thoughts and experiences in the comments section below and explore other articles on our site for more valuable insights.
Remember, staying informed and proactive is key to keeping your IoT ecosystem secure and thriving. Don't hesitate to reach out if you have any questions or need further assistance.
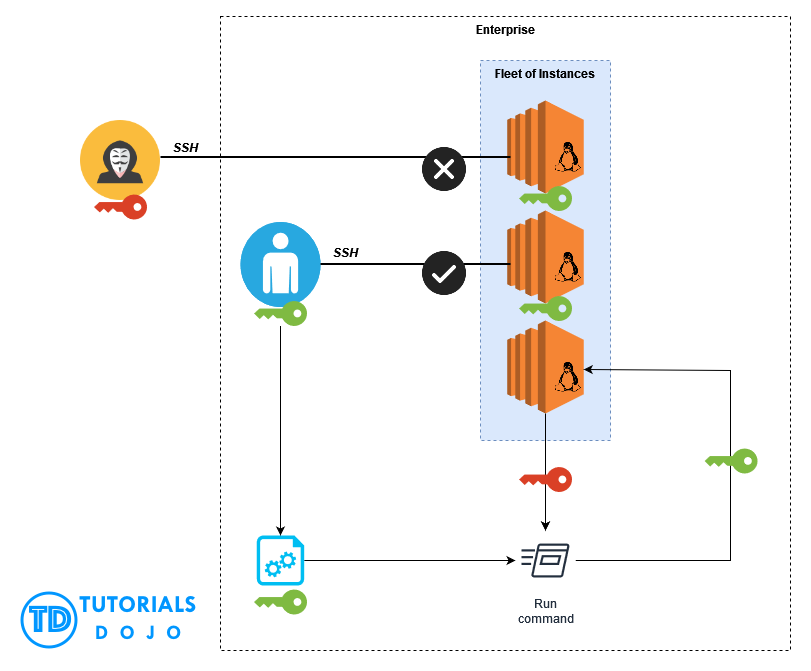
Automatic SSH Key Pair Rotation via AWS Systems Manager Fleet Manager

AWS IoT Services Serverless IoT App Development

Automating AWS IoT Greengrass Setup With AWS CloudFormation The