Comprehensive RemoteIoT Web SSH Tutorial: Your Ultimate Guide
In today's digital age, remote access to IoT devices via web SSH has become increasingly important for managing and maintaining devices from anywhere in the world. Whether you're a system administrator, a developer, or an IoT enthusiast, understanding how to set up and use web SSH for remote IoT devices is a crucial skill. This guide will walk you through everything you need to know to get started with remote IoT web SSH.
As the Internet of Things (IoT) continues to grow, the need for secure and efficient remote management solutions becomes more pressing. RemoteIoT web SSH allows users to access their devices securely over the internet without requiring complex configurations. This tutorial will provide a step-by-step guide to setting up and using web SSH for IoT devices.
Whether you're configuring a Raspberry Pi, monitoring a smart home system, or managing industrial IoT devices, this remote IoT web SSH tutorial will help you master the process. Let's dive in and explore the world of remote IoT management.
- Miguel Ngel Silvestre
- Patrick Kilpatrick
- Georgia Man 1 4 Million Speeding Ticket
- Caroline Stanbury Wealth
Table of Contents
- Introduction to Web SSH
- Why Choose RemoteIoT Web SSH?
- Requirements for Setting Up Web SSH
- Step-by-Step Guide to Setup RemoteIoT Web SSH
- Securing Your Web SSH Connection
- Troubleshooting Common Issues
- Best Practices for RemoteIoT Web SSH
- Alternative Web SSH Solutions
- Case Studies and Examples
- Future of Web SSH in IoT
Introduction to Web SSH
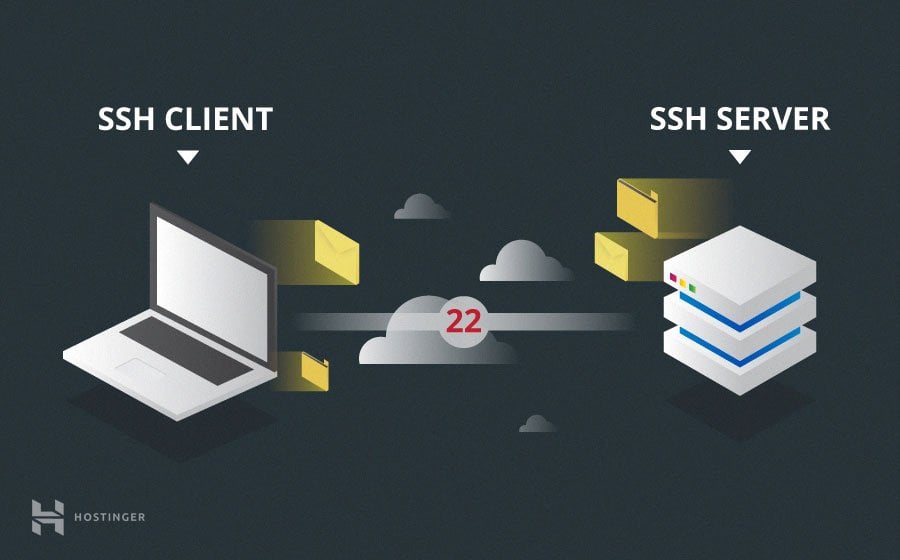
Web SSH is a browser-based solution that allows users to access remote devices securely over the internet using the SSH protocol. This eliminates the need for traditional SSH clients and simplifies the process of remote management. RemoteIoT web SSH, in particular, focuses on providing secure access to IoT devices.
Advantages of Web SSH
Web SSH offers several advantages over traditional SSH clients:
- Platform-independent access
- No need for additional software installation
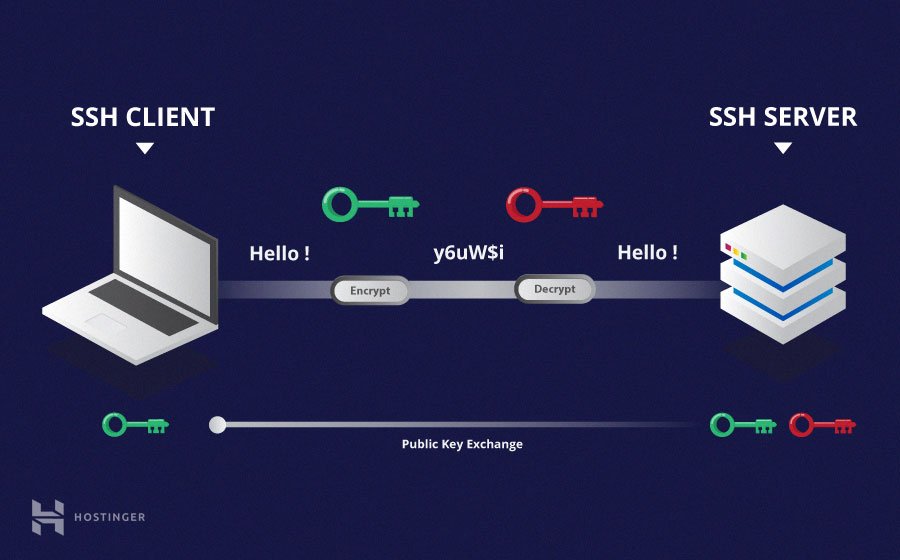
- Improved security with encrypted connections
- Easy integration with IoT devices
Why Choose RemoteIoT Web SSH?
RemoteIoT web SSH stands out due to its focus on IoT devices and its user-friendly interface. It provides a secure and reliable way to manage IoT devices remotely, ensuring that users can maintain and monitor their systems from anywhere in the world.
Key Features of RemoteIoT Web SSH
- Support for multiple IoT platforms
- Advanced encryption protocols
- Real-time monitoring capabilities
- Integration with cloud services
Requirements for Setting Up Web SSH
Before setting up RemoteIoT web SSH, ensure that you have the following requirements:
- An IoT device with SSH enabled
- A stable internet connection
- A modern web browser
- A valid SSH key pair
Having these prerequisites in place will make the setup process smoother and more efficient.
Step-by-Step Guide to Setup RemoteIoT Web SSH
This section will guide you through the process of setting up RemoteIoT web SSH on your IoT device.
Step 1: Enable SSH on Your IoT Device
Ensure that SSH is enabled on your IoT device. This can typically be done through the device's configuration menu or by running a command in the terminal.
Step 2: Generate SSH Key Pair
Create an SSH key pair using a tool like ssh-keygen. This will provide you with a public and private key for secure authentication.
Step 3: Configure Web SSH Access
Set up web SSH access by configuring your IoT device to accept connections over the web. This may involve modifying firewall settings and installing necessary software.
Step 4: Test the Connection
Once the setup is complete, test the connection by accessing your IoT device through a web browser. Ensure that the connection is secure and that you can execute commands successfully.
Securing Your Web SSH Connection
Security is a top priority when using web SSH for IoT devices. Follow these best practices to ensure that your connection remains secure:
- Use strong, unique passwords
- Enable two-factor authentication (2FA)
- Regularly update your device's firmware
- Limit access to trusted IP addresses
Troubleshooting Common Issues
While setting up RemoteIoT web SSH, you may encounter some common issues. Here are solutions to help you overcome them:
Issue 1: Connection Timeout
If you experience connection timeouts, check your network settings and ensure that the necessary ports are open.
Issue 2: Authentication Failure
If authentication fails, verify that your SSH key pair is correctly configured and that your credentials are accurate.
Best Practices for RemoteIoT Web SSH
To make the most of RemoteIoT web SSH, follow these best practices:
- Regularly monitor your device's activity logs
- Keep your software and firmware up to date
- Use encryption for all data transmissions
- Limit access to authorized users only
Alternative Web SSH Solutions
While RemoteIoT web SSH is a popular choice, there are other web SSH solutions available. Some alternatives include:
- GateOne
- WebSSH2
- Termius
Comparison of Web SSH Solutions
When choosing a web SSH solution, consider factors such as ease of use, security features, and compatibility with your IoT devices.
Case Studies and Examples
Here are some real-world examples of how RemoteIoT web SSH has been used successfully:
- A smart home system managed remotely using web SSH
- An industrial IoT network monitored and maintained via web SSH
- A fleet of IoT devices controlled through a centralized web SSH interface
Future of Web SSH in IoT
As IoT continues to evolve, the role of web SSH in remote device management will become even more critical. Future developments may include enhanced security protocols, improved user interfaces, and greater integration with AI-powered systems.
Emerging Trends in Web SSH
Keep an eye on emerging trends such as:
- Blockchain-based authentication
- Quantum-resistant encryption
- Cloud-native SSH solutions
Conclusion
In conclusion, mastering RemoteIoT web SSH is essential for anyone working with IoT devices. This tutorial has provided a comprehensive guide to setting up and using web SSH for remote device management. By following the steps outlined and adhering to best practices, you can ensure secure and efficient access to your IoT devices.
We encourage you to share your experiences and ask questions in the comments section below. Additionally, explore other articles on our site to deepen your knowledge of IoT and related technologies. Thank you for reading, and happy managing!
Data sources and references:

SSH tutorial understand SSH with this Secure Shell guide TSH.io
SSH Tutorial What is SSH, Encryptions and Ports
SSH Tutorial What is SSH, Encryptions and Ports