Use RemoteIoT Web-Based SSH To Remotely Access IoT Devices
In the era of the Internet of Things (IoT), the ability to remotely access and manage devices is no longer a luxury but a necessity. RemoteIoT web-based SSH offers a powerful solution for securely connecting to IoT devices from anywhere in the world. Whether you're an IT professional, a hobbyist, or an enterprise managing a fleet of IoT devices, understanding and utilizing this technology can significantly enhance your operational efficiency.
As IoT continues to expand, the need for remote access solutions that are both secure and user-friendly has never been greater. RemoteIoT web-based SSH bridges the gap by providing a seamless way to interact with IoT devices without compromising on security or functionality. This article delves into the intricacies of RemoteIoT, its advantages, and best practices to ensure a smooth implementation in your projects.
By the end of this comprehensive guide, you'll have a clear understanding of how RemoteIoT web-based SSH works, its potential applications, and the steps required to integrate it into your IoT infrastructure. Let's explore how this cutting-edge technology can revolutionize the way you interact with IoT devices.
Table of Contents
- Introduction to RemoteIoT Web-Based SSH
- Benefits of Using RemoteIoT Web-Based SSH
- How RemoteIoT Web-Based SSH Works
- Security Features of RemoteIoT
- Setup Guide for RemoteIoT
- Common Issues and Troubleshooting
- Applications of RemoteIoT in IoT Projects
- Best Practices for Using RemoteIoT
- Comparison with Other Remote Access Solutions
- Future Trends in RemoteIoT Technology
Introduction to RemoteIoT Web-Based SSH
RemoteIoT web-based SSH is a groundbreaking solution designed specifically for remote access to IoT devices. This technology leverages the power of Secure Shell (SSH) to provide a secure and reliable connection between users and their IoT devices. By using a web-based interface, RemoteIoT eliminates the need for complex configurations and additional software installations, making it accessible to users of all skill levels.
One of the key advantages of RemoteIoT web-based SSH is its ability to work seamlessly across different platforms and devices. Whether you're using a desktop computer, laptop, tablet, or smartphone, you can easily connect to your IoT devices as long as you have an internet connection. This flexibility is crucial in today's fast-paced world, where mobility and accessibility are paramount.
What Makes RemoteIoT Stand Out?
- Web-based interface for easy access
- Supports multiple devices and platforms
- Highly secure with SSH encryption
- Simple setup process
- Cost-effective solution for IoT projects
Benefits of Using RemoteIoT Web-Based SSH
Adopting RemoteIoT web-based SSH offers numerous benefits that can enhance the efficiency and security of your IoT projects. Here are some of the most significant advantages:
Enhanced Security
Security is a top priority when dealing with IoT devices, and RemoteIoT web-based SSH provides robust protection through SSH encryption. This ensures that all data transmitted between your device and the remote server is secure from unauthorized access and potential cyber threats.
Improved Accessibility
With RemoteIoT, you can access your IoT devices from anywhere in the world. This level of accessibility is invaluable for businesses that need to monitor and manage their IoT infrastructure remotely. It also benefits hobbyists who want to experiment with their projects without being tied to a specific location.
Cost-Effectiveness
Implementing RemoteIoT web-based SSH is a cost-effective solution compared to traditional remote access methods. By eliminating the need for additional hardware or software, businesses can save significant resources while still achieving high performance and security.
How RemoteIoT Web-Based SSH Works
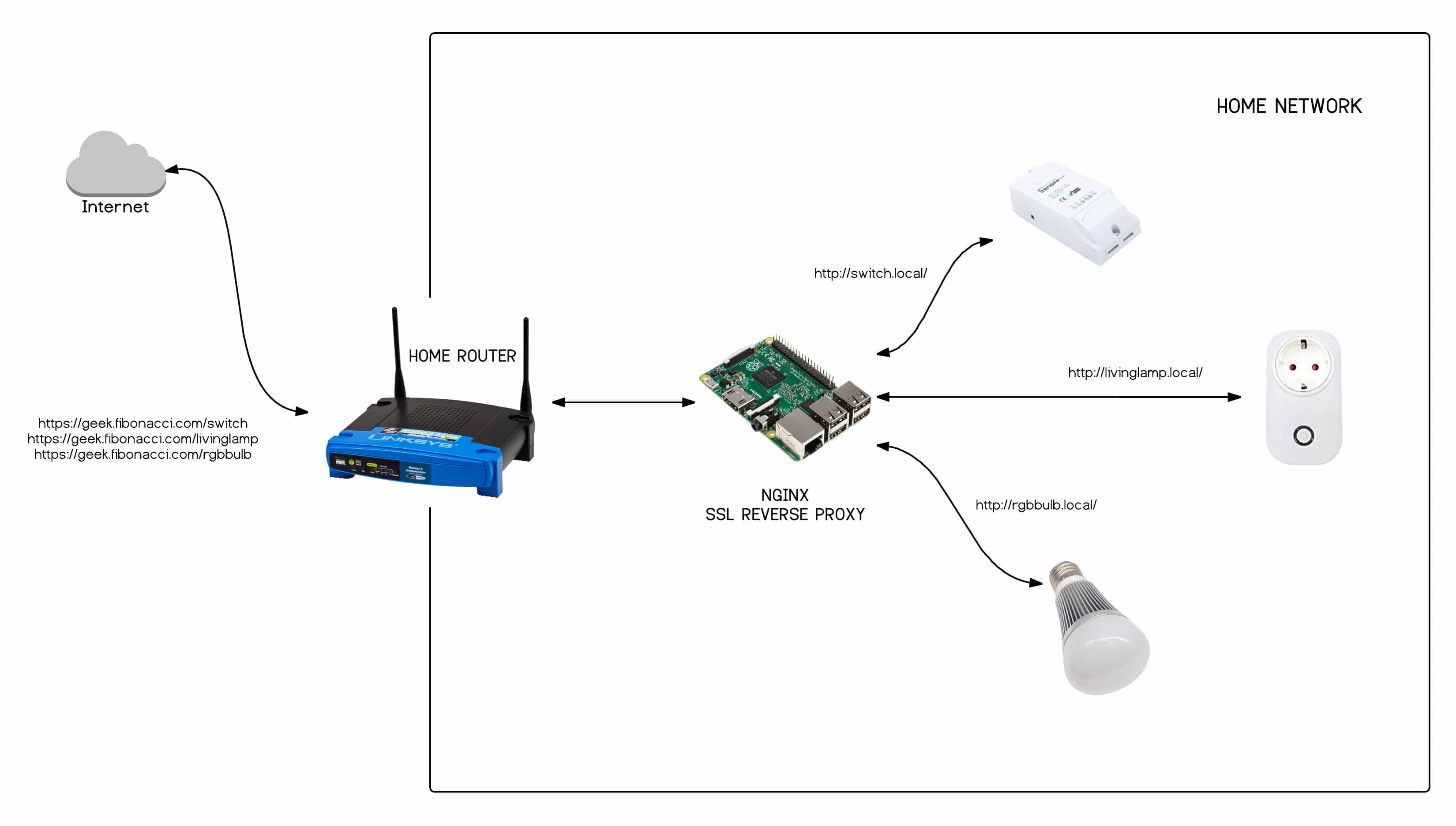
Understanding the inner workings of RemoteIoT web-based SSH is essential for effectively utilizing this technology. At its core, RemoteIoT uses Secure Shell (SSH) protocols to establish a secure connection between the user and the IoT device. Here's a step-by-step breakdown of how it operates:
- User accesses the RemoteIoT web interface through a browser.
- The web interface communicates with the RemoteIoT server, which acts as a bridge between the user and the IoT device.
- The RemoteIoT server establishes an SSH connection with the target IoT device.
- Data is transmitted securely between the user and the IoT device via the SSH tunnel.
Key Components of RemoteIoT
- Web Interface: Provides a user-friendly way to interact with IoT devices.
- RemoteIoT Server: Acts as a mediator between the user and the IoT device.
- SSH Protocol: Ensures secure communication through encryption.
Security Features of RemoteIoT
Security is a critical aspect of any remote access solution, and RemoteIoT web-based SSH excels in this area. Here are some of the key security features that make RemoteIoT a trusted choice for IoT projects:
SSH Encryption
RemoteIoT utilizes SSH encryption to protect data during transmission. This ensures that sensitive information remains secure and inaccessible to unauthorized parties.
Two-Factor Authentication
To further enhance security, RemoteIoT supports two-factor authentication (2FA). This adds an extra layer of protection by requiring users to provide two forms of identification before accessing their IoT devices.
Firewall Integration
RemoteIoT can be integrated with firewalls to filter and control incoming and outgoing traffic. This helps prevent unauthorized access and potential security breaches.
Setup Guide for RemoteIoT
Setting up RemoteIoT web-based SSH is a straightforward process that can be completed in a few simple steps. Follow the instructions below to get started:
Step 1: Install the RemoteIoT Server
Begin by installing the RemoteIoT server on your local network. This can be done using a dedicated server or a virtual machine.
Step 2: Configure SSH Settings
Once the server is installed, configure the SSH settings to ensure a secure connection. This includes setting up user accounts, enabling encryption, and configuring firewalls.
Step 3: Connect IoT Devices
Next, connect your IoT devices to the RemoteIoT server. This can be done by configuring the SSH client on each device to communicate with the server.
Step 4: Access Devices via Web Interface
Finally, access your IoT devices through the RemoteIoT web interface. Use your preferred browser to log in and start managing your devices remotely.
Common Issues and Troubleshooting
While RemoteIoT web-based SSH is a reliable solution, you may encounter some issues during setup or operation. Here are some common problems and their solutions:
Connection Errors
If you're unable to establish a connection, check the following:
- Ensure the RemoteIoT server is running and accessible.
- Verify the SSH settings and credentials.
- Check the firewall rules to ensure they allow SSH traffic.
Performance Issues
Slow performance can be caused by network congestion or insufficient server resources. To resolve this:
- Optimize network settings to reduce latency.
- Upgrade server hardware if necessary.
- Monitor server performance regularly and make adjustments as needed.
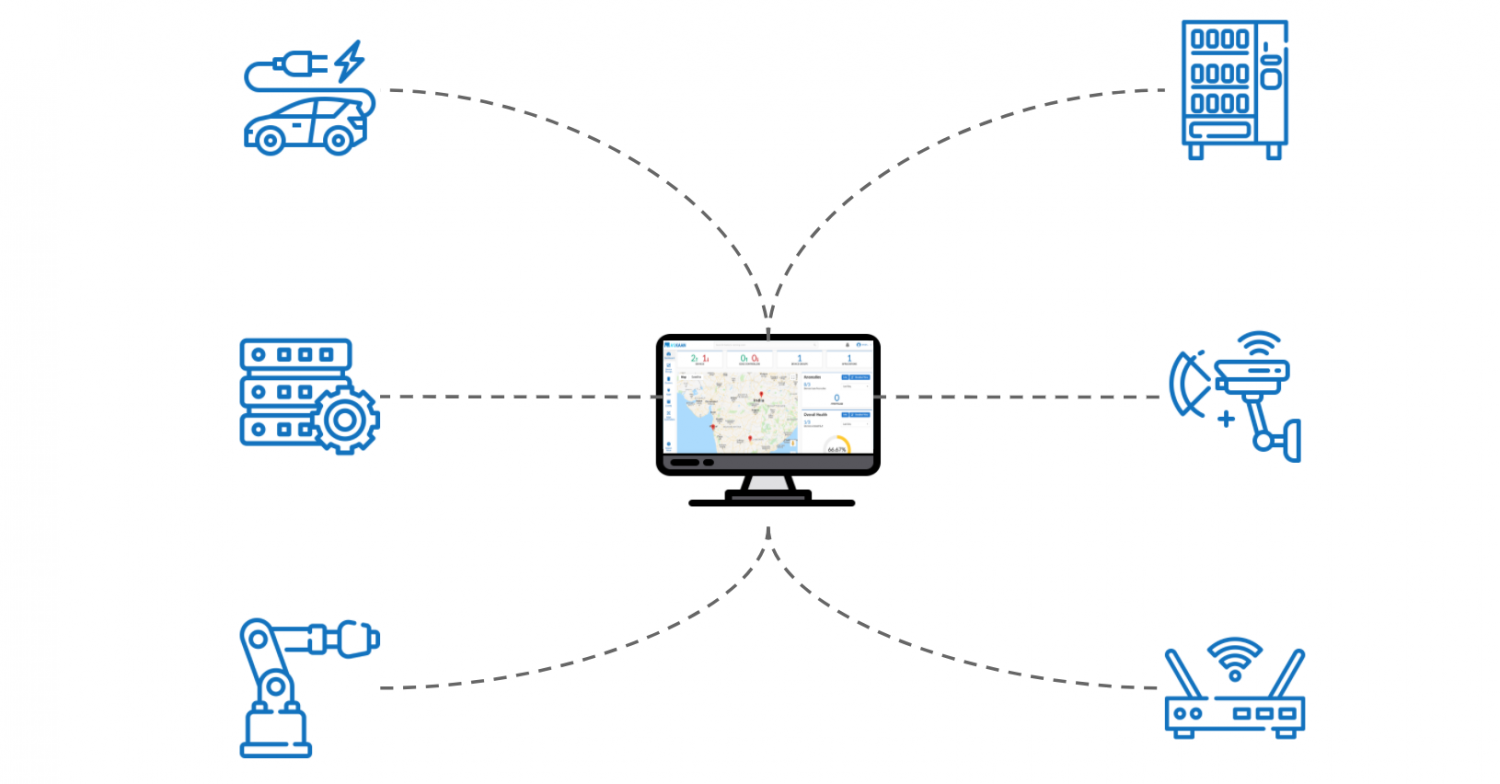
Applications of RemoteIoT in IoT Projects
RemoteIoT web-based SSH can be applied to a wide range of IoT projects, from smart homes to industrial automation. Here are some examples of how this technology can be utilized:
Smart Home Automation
Use RemoteIoT to control smart home devices such as lights, thermostats, and security systems from anywhere in the world. This enhances convenience and security for homeowners.
Industrial Automation
In industrial settings, RemoteIoT can be used to monitor and manage machinery and equipment remotely. This reduces downtime and improves overall efficiency.
Agricultural IoT
RemoteIoT enables farmers to monitor soil moisture, weather conditions, and other critical factors in real-time. This helps optimize resource usage and increase crop yields.
Best Practices for Using RemoteIoT
To maximize the benefits of RemoteIoT web-based SSH, follow these best practices:
Regular Updates
Keep the RemoteIoT server and all connected devices up to date with the latest software and security patches. This ensures optimal performance and protection against emerging threats.
Secure Credentials
Use strong, unique passwords for all user accounts and enable two-factor authentication whenever possible. This minimizes the risk of unauthorized access.
Monitor Activity
Regularly review server logs and activity reports to detect any suspicious behavior. This proactive approach helps identify and address potential security issues before they escalate.
Comparison with Other Remote Access Solutions
While there are several remote access solutions available, RemoteIoT web-based SSH stands out due to its simplicity, security, and versatility. Here's how it compares to other popular options:
VNC (Virtual Network Computing)
VNC is a widely used remote access tool, but it lacks the security features and ease of use offered by RemoteIoT. Additionally, VNC requires more resources and can be more complex to set up.
TeamViewer
TeamViewer is another popular remote access solution, but it often requires additional software installations and may not be as cost-effective as RemoteIoT for large-scale IoT projects.
Future Trends in RemoteIoT Technology
The future of RemoteIoT web-based SSH looks promising, with ongoing advancements in IoT technology and cybersecurity. Here are some trends to watch for:
Enhanced Security Protocols
As cyber threats continue to evolve, RemoteIoT will likely adopt even more advanced security protocols to protect against emerging risks.
Increased Integration
RemoteIoT is expected to become more integrated with other IoT platforms and technologies, enabling seamless interaction between various systems and devices.
AI and Machine Learning
The incorporation of AI and machine learning into RemoteIoT could lead to smarter, more autonomous remote access solutions that adapt to user needs and preferences.
Conclusion
In conclusion, RemoteIoT web-based SSH offers a secure, flexible, and cost-effective solution for remotely accessing IoT devices. By leveraging this technology, you can enhance the efficiency and security of your IoT projects while enjoying the convenience of web-based access. To get the most out of RemoteIoT, follow the best practices outlined in this guide and stay informed about future trends in the field.
We invite you to share your thoughts and experiences with RemoteIoT in the comments below. Additionally, feel free to explore other articles on our site for more insights into IoT technology and related topics.
- Nathan Fillion Modern Family
- Shailene Woodley Baby Daddy
- Morrissey And Jake Walters
- Johnny Manziel Josie Canseco
Remotely Access IoT Devices Aikaan

Use Remote WebBased SSH To Remotely Access IoT Devices
How To Use RemoteIoT WebBased SSH To Remotely Access IoT Devices Server