Best SSH IoT Device Remotely Android: The Ultimate Guide
In today's digital age, managing IoT devices remotely via SSH on Android has become increasingly popular among tech enthusiasts and professionals alike. Whether you're a developer, network administrator, or simply someone looking to enhance their remote connectivity, understanding the best SSH IoT device options for Android is crucial. This guide will delve into everything you need to know about setting up, securing, and optimizing your IoT devices using SSH on Android.
With the rapid advancement of technology, the Internet of Things (IoT) has transformed the way we interact with devices. From smart homes to industrial automation, IoT devices have become an integral part of our daily lives. However, managing these devices remotely can be challenging without the right tools and knowledge.
This article aims to provide a comprehensive overview of the best SSH IoT device options for Android users. We'll explore the tools, techniques, and best practices to ensure seamless remote management while maintaining security and efficiency. Let's dive in!
Table of Contents
- Introduction to SSH
- IoT Device Remote Management
- Best SSH Clients for Android
- Securing SSH Connections
- Configuring SSH on IoT Devices
- Troubleshooting SSH Connections
- Benefits of Using SSH for IoT
- Common Mistakes to Avoid
- Future Trends in SSH and IoT
- Conclusion
- SSH Client Recommendations
- SSH Security Best Practices
- IoT Device Configuration
- SSH Performance Optimization
- SSH Automation Techniques
- IoT Security Tips
Introduction to SSH
SSH, or Secure Shell, is a cryptographic network protocol designed for secure data communication, remote command execution, and file transfer between devices over an unsecured network. It provides a secure channel over which data can be encrypted and transmitted safely, making it an ideal choice for managing IoT devices remotely.
The primary purpose of SSH is to ensure secure communication by encrypting all data transmitted between the client and server. This includes credentials, commands, and sensitive information, reducing the risk of unauthorized access and data breaches.
For Android users, SSH offers a powerful solution for managing IoT devices remotely. With the right tools and configurations, you can access and control your IoT devices from anywhere, ensuring seamless connectivity and management.
IoT Device Remote Management
Managing IoT devices remotely is essential for maintaining efficiency and security in modern networks. Whether you're monitoring smart home devices, industrial sensors, or network infrastructure, having remote access capabilities is crucial.
SSH plays a vital role in remote management by providing a secure and reliable connection between the user and the IoT device. Unlike traditional methods that rely on unencrypted protocols, SSH ensures that all communication is encrypted and secure, reducing the risk of cyberattacks.
Some of the key benefits of using SSH for IoT device remote management include:
- Enhanced security through encryption
- Reliable and stable connections
- Support for multiple authentication methods
- Compatibility with various operating systems and devices
Best SSH Clients for Android
When it comes to managing IoT devices remotely via SSH on Android, choosing the right client is essential. Here are some of the best SSH clients available for Android users:
SSH Client Recommendations
- Termius: A popular SSH client for Android that offers a user-friendly interface and robust features, including support for multiple connections, key management, and session synchronization.
- ConnectBot: An open-source SSH client that provides advanced features such as port forwarding, key generation, and support for multiple sessions.
- Serverauditor: A comprehensive SSH client that includes additional tools for server monitoring and management, making it ideal for professionals.
Each of these clients has its own strengths and features, so choosing the right one depends on your specific needs and preferences. Consider factors such as ease of use, feature set, and compatibility with your IoT devices when making your decision.
Securing SSH Connections
Security is a top priority when managing IoT devices remotely via SSH. Ensuring that your connections are secure is essential to protect sensitive data and prevent unauthorized access.
SSH Security Best Practices
Here are some best practices for securing your SSH connections:
- Use strong passwords: Avoid using weak or easily guessable passwords. Consider using a password manager to generate and store complex passwords.
- Enable public key authentication: Public key authentication provides a more secure alternative to password-based authentication by using cryptographic keys.
- Disable root login: Restricting root access reduces the risk of unauthorized access to critical system components.
- Use a non-standard port: Changing the default SSH port (22) can help deter automated attacks and reduce the risk of brute-force attacks.
Implementing these security measures will significantly enhance the security of your SSH connections, ensuring that your IoT devices remain protected from potential threats.
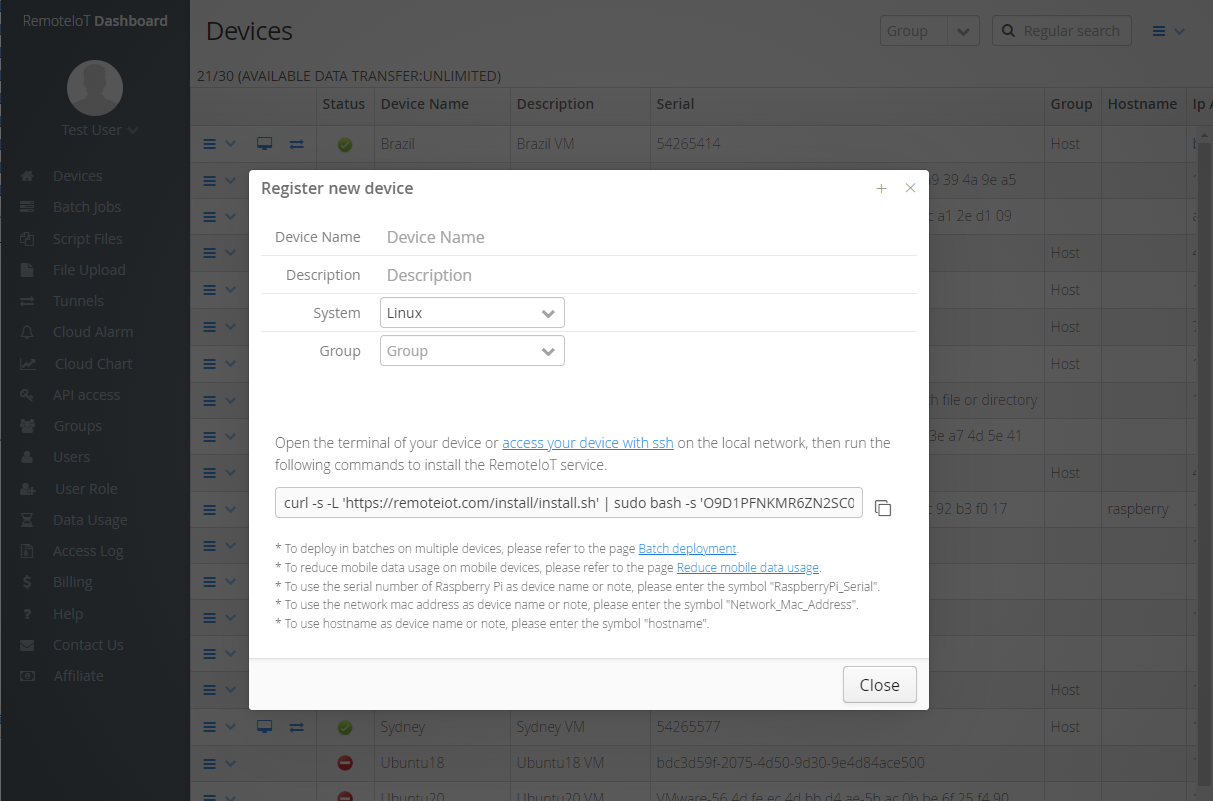
Configuring SSH on IoT Devices
Configuring SSH on your IoT devices is a critical step in enabling remote management. Proper configuration ensures that your devices are accessible and secure.
IoT Device Configuration
Here are the steps to configure SSH on your IoT devices:
- Install SSH server software: Depending on the operating system of your IoT device, you may need to install an SSH server application, such as OpenSSH.
- Generate SSH keys: Create a pair of public and private keys for authentication purposes. This step is crucial for enabling public key authentication.
- Configure SSH settings: Adjust the SSH configuration file (usually located at /etc/ssh/sshd_config) to include your desired settings, such as disabling password authentication and enabling public key authentication.
- Restart the SSH service: After making changes to the configuration file, restart the SSH service to apply the new settings.
By following these steps, you can ensure that your IoT devices are properly configured for secure remote access via SSH.
Troubleshooting SSH Connections
Even with proper configuration, issues can arise when establishing SSH connections to your IoT devices. Here are some common troubleshooting tips:
- Check network connectivity: Ensure that your device is connected to the network and accessible from your Android device.
- Verify SSH service status: Confirm that the SSH service is running on your IoT device and listening on the correct port.
- Test firewall settings: Ensure that your firewall allows incoming SSH connections on the specified port.
- Review logs for errors: Check the system logs for any errors or warnings related to SSH connections.
Addressing these issues promptly can help resolve connection problems and ensure smooth remote access to your IoT devices.
Benefits of Using SSH for IoT
Using SSH for IoT device management offers numerous benefits, including:
- Enhanced security: SSH provides a secure channel for communication, protecting sensitive data and credentials.
- Efficient remote management: With SSH, you can manage your IoT devices from anywhere, streamlining your workflow and reducing downtime.
- Compatibility with diverse devices: SSH supports a wide range of devices and operating systems, making it a versatile solution for IoT management.
- Automation capabilities: SSH enables automation of repetitive tasks, saving time and increasing efficiency.
These benefits make SSH an ideal choice for managing IoT devices remotely, ensuring both security and convenience.
Common Mistakes to Avoid
While SSH is a powerful tool for IoT device management, there are common mistakes that users should avoid:
- Using weak passwords: Weak passwords can compromise the security of your SSH connections, making your devices vulnerable to attacks.
- Ignoring software updates: Failing to update your SSH client and server software can leave your devices exposed to known vulnerabilities.
- Not securing private keys: Storing private keys insecurely can lead to unauthorized access if they fall into the wrong hands.
- Using default configurations: Default settings often lack the necessary security features, so it's important to customize them to meet your specific needs.
Avoiding these mistakes will help ensure that your SSH connections remain secure and reliable.
Future Trends in SSH and IoT
As technology continues to evolve, the future of SSH and IoT holds exciting possibilities. Some emerging trends include:
- Quantum-resistant encryption: With the rise of quantum computing, new encryption methods are being developed to ensure the security of SSH connections in the future.
- AI-driven automation: Artificial intelligence is being integrated into SSH management tools to automate tasks and improve efficiency.
- Edge computing integration: Combining SSH with edge computing can enhance the performance and security of IoT devices, reducing latency and improving data processing capabilities.
Staying informed about these trends will help you adapt to the changing landscape of IoT and SSH technology, ensuring that your devices remain secure and efficient.
Conclusion
In conclusion, managing IoT devices remotely via SSH on Android offers numerous benefits, including enhanced security, efficient remote management, and compatibility with diverse devices. By choosing the right SSH client, securing your connections, and following best practices, you can ensure seamless and secure access to your IoT devices.
We encourage you to take action by exploring the tools and techniques discussed in this article. Share your thoughts and experiences in the comments section below, and don't forget to check out our other articles for more insights into IoT and SSH technology.
Thank you for reading, and happy managing!
How to remotely ssh iot device in web browser
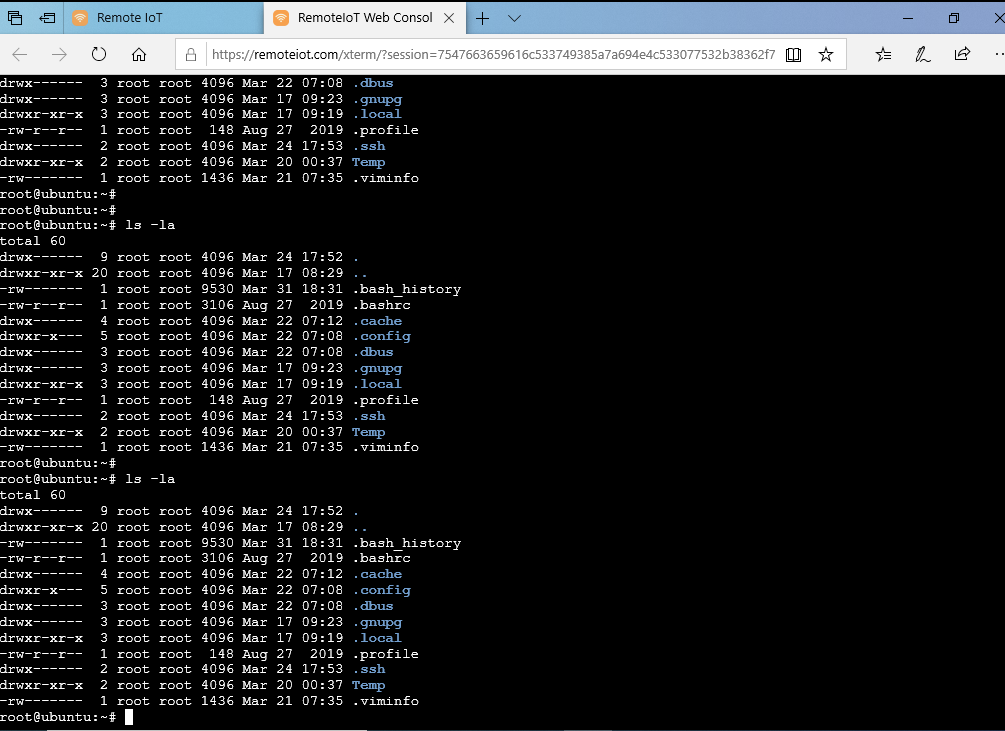
How to remotely ssh iot device in web browser

Best SSH Client For Android Mobiles And Tablets TechPanga