Remote SSH IoT Over Internet: Free Download And Setup Guide
Remote SSH IoT over the internet has become an essential tool for managing devices from anywhere in the world. As the Internet of Things (IoT) continues to expand, the ability to securely access and control IoT devices remotely is no longer a luxury but a necessity. Whether you're a tech enthusiast, a hobbyist, or a professional, understanding how to set up remote SSH for IoT devices can significantly enhance your project's functionality and efficiency.
In today's fast-paced world, the demand for remote connectivity solutions is skyrocketing. Remote SSH IoT over the internet allows users to access their devices securely without being physically present. This technology is particularly useful for monitoring sensors, controlling home automation systems, or managing industrial equipment. By leveraging free tools and platforms, even beginners can set up remote SSH connections with minimal effort.
This comprehensive guide will walk you through the process of setting up remote SSH for IoT devices over the internet, including free download options, security considerations, and best practices. Whether you're new to IoT or an experienced developer, this article will provide you with the knowledge and tools needed to get started.
Table of Contents
- Introduction to Remote SSH IoT
- Benefits of Using Remote SSH IoT
- How to Set Up Remote SSH IoT Over the Internet
- Free Tools for Remote SSH IoT
- Security Considerations for Remote SSH IoT
- Common Issues and Troubleshooting
- Best Practices for Remote SSH IoT
- Applications of Remote SSH IoT
- Statistics and Industry Trends
- The Future of Remote SSH IoT
Introduction to Remote SSH IoT
Remote SSH IoT refers to the process of accessing and controlling IoT devices remotely using the Secure Shell (SSH) protocol. SSH is a cryptographic network protocol designed to provide secure communication over an unsecured network. By enabling remote SSH connections, users can manage their IoT devices from anywhere in the world, provided they have internet access.
How Does SSH Work?
SSH works by creating an encrypted connection between a client and a server. This ensures that all data transmitted between the two parties remains secure and protected from unauthorized access. The protocol supports various authentication methods, including password-based authentication and public-key authentication, which adds an extra layer of security.
Why Choose Remote SSH for IoT?
Remote SSH is preferred for IoT applications due to its robust security features and ease of implementation. Unlike other remote access protocols, SSH is specifically designed to handle sensitive data securely, making it ideal for IoT devices that often transmit critical information.
Benefits of Using Remote SSH IoT
Implementing remote SSH for IoT offers numerous advantages that make it a popular choice among developers and businesses alike.
Enhanced Security
One of the primary benefits of using SSH for IoT is its strong encryption and authentication mechanisms. This ensures that your devices are protected from unauthorized access and cyber threats.
Cost-Effective Solution
Many SSH tools and platforms are available for free, making it an affordable option for individuals and organizations looking to implement remote connectivity solutions.
Flexibility and Scalability
SSH can be easily integrated into various IoT systems, regardless of their size or complexity. This flexibility allows users to scale their operations as needed without significant additional costs.
How to Set Up Remote SSH IoT Over the Internet
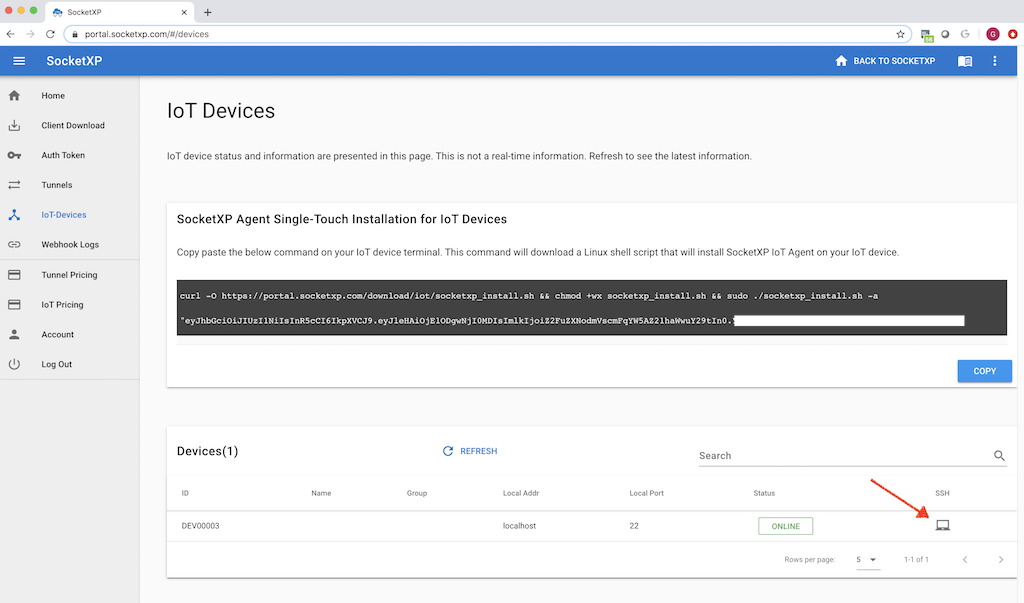
Setting up remote SSH for IoT devices involves several steps, from installing the necessary software to configuring your network settings. Below is a step-by-step guide to help you get started.
Step 1: Install SSH Server on Your IoT Device
The first step is to install an SSH server on your IoT device. Most Linux-based devices come with SSH pre-installed, but if not, you can install it using the package manager. For example, on a Raspberry Pi, you can enable SSH by running the following command:
sudo systemctl enable ssh
Step 2: Configure Your Router
To allow remote access, you need to configure your router to forward incoming SSH connections to your IoT device. This involves setting up port forwarding and assigning a static IP address to your device.
Step 3: Use a Dynamic DNS Service
Since most home internet connections use dynamic IP addresses, it's advisable to use a dynamic DNS (DDNS) service to maintain a consistent domain name for your device. Popular DDNS services include No-IP and DuckDNS, both of which offer free plans.
Free Tools for Remote SSH IoT
Several free tools are available to facilitate remote SSH IoT connections. Below are some of the most popular options:
- Putty: A widely-used SSH client for Windows that allows users to connect to remote devices easily.
- WinSCP: A free SFTP client and FTP client for Windows that supports file transfers over SSH.
- Termius: A cross-platform SSH client available for Windows, macOS, iOS, and Android, offering a user-friendly interface for managing SSH connections.
Security Considerations for Remote SSH IoT
While SSH provides a secure method for remote access, it's essential to follow best practices to minimize security risks.
Use Strong Passwords
Ensure that all SSH accounts have strong, unique passwords. Avoid using default credentials or easily guessable passwords.
Enable Public-Key Authentication
Public-key authentication is a more secure alternative to password-based authentication. It involves generating a pair of cryptographic keys (public and private) and using them to authenticate users.
Regularly Update Your System
Keep your IoT devices and SSH software up to date with the latest security patches and updates to protect against vulnerabilities.
Common Issues and Troubleshooting
Despite its reliability, SSH connections can sometimes encounter issues. Below are some common problems and their solutions:
- Connection Refused: Ensure that the SSH server is running and that the correct port is being used.
- Authentication Failed: Double-check your login credentials and ensure that public-key authentication is properly configured.
- Network Connectivity Issues: Verify that your router is correctly configured and that there are no firewall restrictions blocking SSH traffic.
Best Practices for Remote SSH IoT
To ensure a smooth and secure remote SSH IoT experience, follow these best practices:
Limit SSH Access
Restrict SSH access to trusted IP addresses or networks to reduce the risk of unauthorized access.
Monitor Activity Logs
Regularly review SSH activity logs to detect any suspicious activity or potential security breaches.
Disable Root Login
Disable root login to prevent attackers from gaining administrative access to your devices.
Applications of Remote SSH IoT
Remote SSH IoT has a wide range of applications across various industries. Some of the most common use cases include:
- Home Automation: Control smart home devices such as lights, thermostats, and security systems remotely.
- Industrial IoT: Monitor and manage industrial equipment and processes from a centralized location.
- Agriculture: Use IoT sensors to collect data on soil moisture, temperature, and other environmental factors, enabling farmers to make informed decisions.
Statistics and Industry Trends
The IoT market is expected to grow significantly in the coming years, with remote SSH playing a crucial role in enabling secure connectivity. According to a report by Statista, the global IoT market is projected to reach $1.6 trillion by 2025. This growth is driven by advancements in technology, increasing adoption of smart devices, and rising demand for remote monitoring solutions.
The Future of Remote SSH IoT
As IoT continues to evolve, remote SSH will remain a vital component of secure remote connectivity. Future developments may include enhanced encryption algorithms, improved user interfaces, and integration with emerging technologies such as 5G and edge computing.
Conclusion
Remote SSH IoT over the internet offers a secure and cost-effective solution for managing IoT devices remotely. By following the steps outlined in this guide, you can set up a reliable SSH connection and take full advantage of the benefits it provides. Remember to prioritize security and adhere to best practices to protect your devices and data.
We encourage you to share your thoughts and experiences in the comments section below. If you found this article helpful, consider sharing it with others who may benefit from the information. For more insightful content, explore our other articles on IoT and related topics.

How to Remote Access IoT SSH over the
How to Remote Access IoT SSH over the

How to Remote Access IoT SSH over the