Remote IoT Platform SSH Download For Raspberry Pi Without Hassle
Setting up a remote IoT platform using SSH on a Raspberry Pi can seem daunting, but it doesn't have to be. Whether you're a beginner or an experienced developer, this guide will walk you through the process seamlessly. In today's world of interconnected devices, having a robust remote IoT platform is essential for managing and monitoring systems efficiently.
As more businesses and individuals embrace IoT technology, the ability to control devices remotely has become a necessity. This is where SSH (Secure Shell) comes into play, offering a secure way to manage your Raspberry Pi remotely. By downloading and configuring the right tools, you can create a reliable IoT platform without unnecessary complications.
Throughout this article, we will explore the steps to set up a remote IoT platform using SSH on a Raspberry Pi. We'll cover everything from the basics of SSH to advanced configurations, ensuring you have all the information you need to get started. Let's dive in!
Table of Contents
- Introduction to SSH
- Raspberry Pi Setup
- Why Use SSH for IoT
- Downloading SSH
- Configuring SSH
- Remote Access
- Securing Your IoT Platform
- Troubleshooting
- Best Practices
- Conclusion
Introduction to SSH
SSH, or Secure Shell, is a cryptographic protocol used to secure communication between devices over a network. It provides a safe way to access remote servers, making it ideal for managing IoT platforms. With SSH, you can execute commands, transfer files, and manage configurations without compromising security.
One of the primary benefits of SSH is its encryption capabilities, which protect data from unauthorized access. This makes it an essential tool for anyone working with IoT devices, especially when managing them remotely. Understanding how SSH works and its key features will help you harness its full potential.
Key Features of SSH
- Encryption for secure communication.
- Authentication methods, such as passwords and public key authentication.
- Support for tunneling, allowing secure connections to other services.
Raspberry Pi Setup
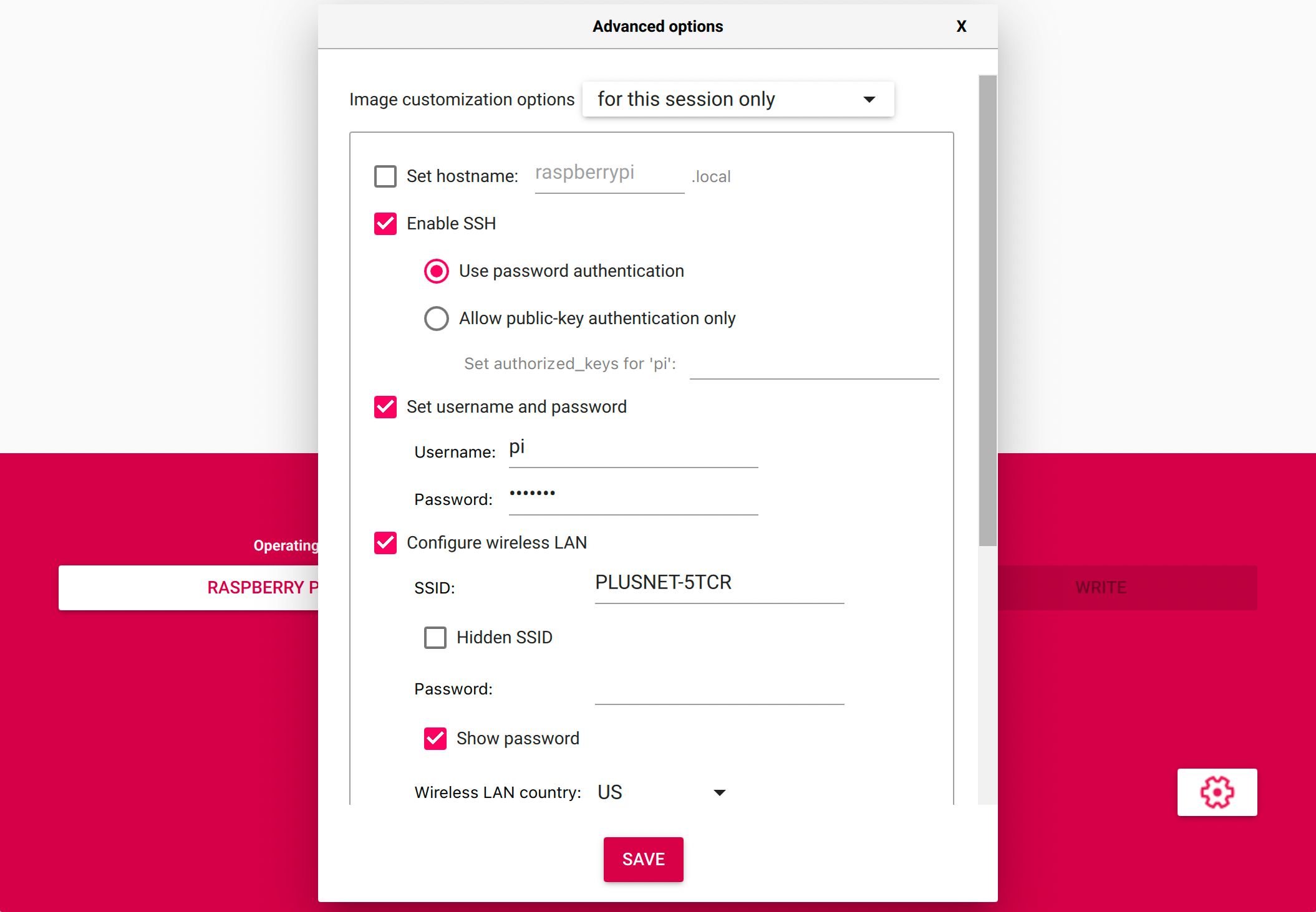
Before diving into SSH, it's crucial to ensure your Raspberry Pi is properly set up. This includes installing the operating system, configuring network settings, and updating the software. A well-prepared Raspberry Pi will serve as a solid foundation for your IoT platform.
Start by downloading the latest version of Raspberry Pi OS from the official website. Once installed, configure your network settings to ensure your Pi can connect to the internet. This step is vital for enabling remote access via SSH.
Steps for Raspberry Pi Setup
- Download Raspberry Pi OS.
- Flash the OS onto an SD card using a tool like Etcher.
- Insert the SD card into your Raspberry Pi and power it on.
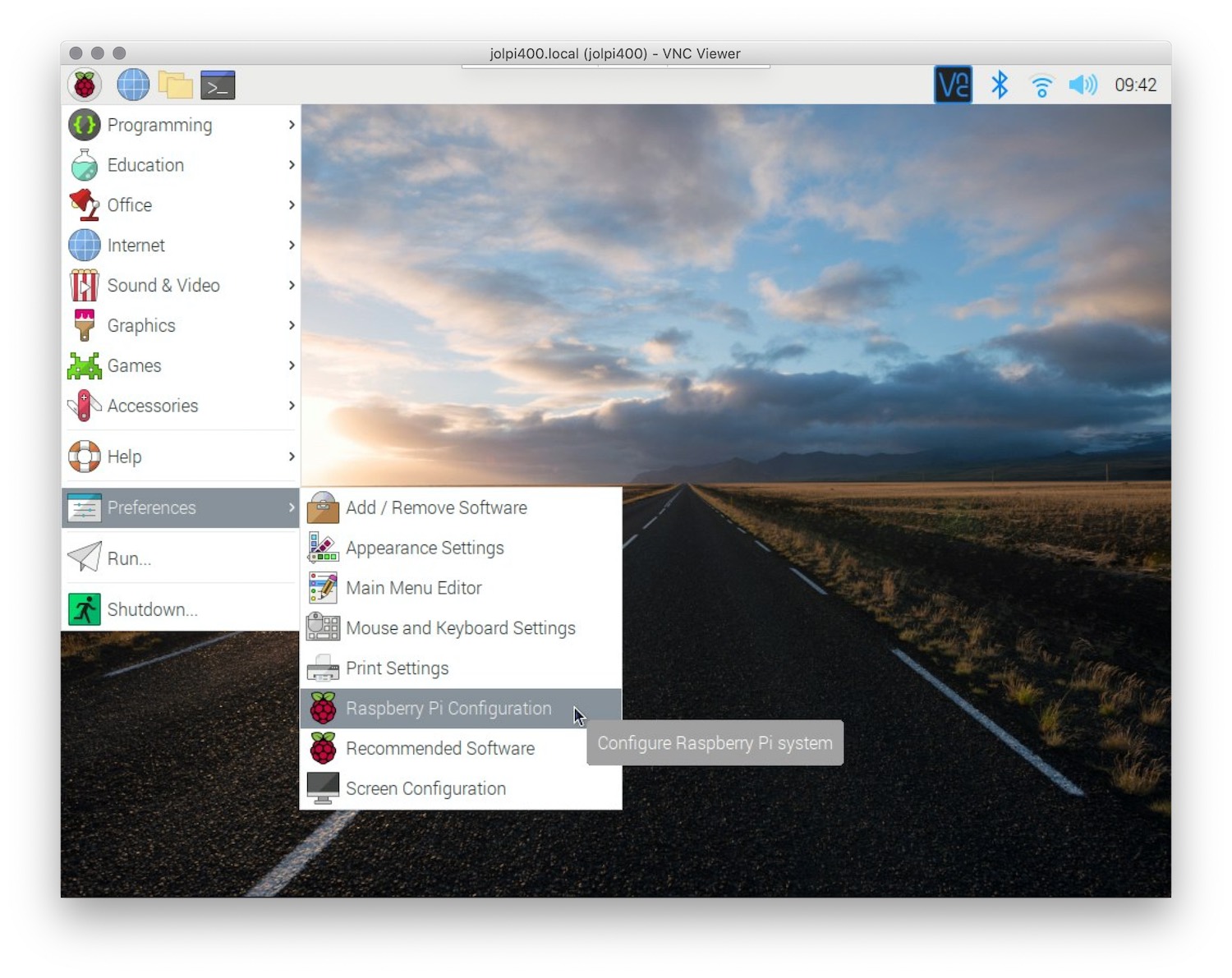
- Configure network settings in the Raspberry Pi Configuration tool.
Why Use SSH for IoT
Using SSH for IoT platforms offers several advantages over other remote management solutions. First and foremost, SSH ensures secure communication between devices, protecting sensitive data from potential threats. Additionally, SSH is lightweight and efficient, making it suitable for resource-constrained IoT devices like the Raspberry Pi.
Another benefit of SSH is its versatility. It can be used for a wide range of tasks, from executing commands to transferring files, all while maintaining a high level of security. This flexibility makes SSH an indispensable tool for managing IoT platforms.
Downloading SSH
Downloading SSH for your Raspberry Pi is a straightforward process. In most cases, SSH is already pre-installed on Raspberry Pi OS. However, if you're using a custom or minimal installation, you may need to install it manually.
To check if SSH is installed, open the terminal on your Raspberry Pi and type the following command:
ssh
If SSH is installed, you'll see a list of available options. If not, you can install it using the following command:
sudo apt-get install openssh-server
Alternative SSH Clients
- PuTTY (for Windows users).
- Terminal (for macOS and Linux users).
- MobaxTerm (a comprehensive SSH client for Windows).
Configuring SSH
Once SSH is installed, the next step is to configure it for your IoT platform. This involves setting up authentication methods, adjusting security settings, and enabling remote access. Proper configuration is essential for ensuring the security and functionality of your IoT platform.
Start by editing the SSH configuration file located at /etc/ssh/sshd_config. Use a text editor like nano to make changes:
sudo nano /etc/ssh/sshd_config
From here, you can modify settings such as the port number, authentication methods, and security options.
Key Configuration Settings
- Port: Change the default port (22) to enhance security.
- Authentication: Disable password authentication and use public key authentication instead.
- Logging: Enable detailed logging to monitor SSH activity.
Remote Access
With SSH configured, you can now access your Raspberry Pi remotely. This allows you to manage your IoT platform from anywhere in the world, provided you have an internet connection. Remote access is particularly useful for troubleshooting and maintaining devices without physical access.
To connect to your Raspberry Pi via SSH, you'll need its IP address. You can find this information by running the following command on your Pi:
ifconfig
Once you have the IP address, use an SSH client to establish a connection. For example, if your Pi's IP address is 192.168.1.100, you can connect using the following command:
ssh pi@192.168.1.100
Dynamic DNS for Remote Access
If your Raspberry Pi's IP address changes frequently, consider setting up a dynamic DNS service. This allows you to access your Pi using a static domain name, regardless of its actual IP address. Popular dynamic DNS providers include No-IP and DuckDNS.
Securing Your IoT Platform
Security is a top priority when setting up a remote IoT platform. By implementing best practices, you can protect your devices from unauthorized access and potential threats. This includes using strong passwords, enabling firewalls, and keeping your software up to date.
One of the most effective ways to secure your IoT platform is to use public key authentication instead of passwords. This method eliminates the risk of brute-force attacks and ensures only authorized users can access your devices.
Security Best Practices
- Use strong, unique passwords.
- Enable a firewall to restrict incoming connections.
- Keep your software and firmware updated.
- Monitor SSH logs for suspicious activity.
Troubleshooting
Despite careful planning, issues can arise when setting up a remote IoT platform. Common problems include connection errors, authentication failures, and configuration mistakes. Understanding how to troubleshoot these issues will help you resolve them quickly and efficiently.
If you're unable to connect to your Raspberry Pi via SSH, check the following:
- Ensure SSH is enabled on your Pi.
- Verify the IP address and port number.
- Check firewall settings to ensure SSH traffic is allowed.
Common SSH Errors
- "Connection refused": Indicates SSH is not running or the port is blocked.
- "Permission denied": Suggests authentication issues, such as incorrect credentials.
- "Host key verification failed": Occurs when the server's host key doesn't match the stored key.
Best Practices
Adhering to best practices will help you create a robust and secure remote IoT platform. This includes using SSH effectively, maintaining secure configurations, and regularly updating your devices. By following these guidelines, you can ensure your IoT platform remains reliable and protected.
In addition to security measures, consider implementing automation tools to streamline management tasks. This can include setting up scripts for routine maintenance, monitoring system performance, and automating backups.
Automation Tools for IoT Platforms
- Cron jobs for scheduling tasks.
- Monitoring tools like Nagios or Zabbix.
- Backup solutions like rsync or Duplicati.
Conclusion
Setting up a remote IoT platform using SSH on a Raspberry Pi is a powerful way to manage and monitor devices efficiently. By following the steps outlined in this guide, you can create a secure and functional platform without unnecessary complications. Remember to prioritize security and regularly update your devices to protect against potential threats.
We encourage you to share your experiences and insights in the comments below. Your feedback helps us improve and provides valuable information to other readers. Don't forget to explore our other articles for more tips and tricks on IoT and technology.
Remote IoT Platform SSH Download Raspberry Pi Without Windows
How To Access A Remote IoT Platform And Download Raspberry Pi Files
How to enable SSH and WiFi on Raspberry PI (without monitor) IoT