RemoteIoT Firewall Examples: A Comprehensive Guide For Enhanced Cybersecurity
In the rapidly evolving digital landscape, ensuring robust cybersecurity measures is more crucial than ever. RemoteIoT firewall examples serve as a cornerstone for safeguarding networks and devices against unauthorized access and cyber threats. These firewalls are specifically designed to protect Internet of Things (IoT) devices, which are increasingly being used in homes, businesses, and industrial settings. As the number of connected devices grows, so does the need for advanced security solutions.
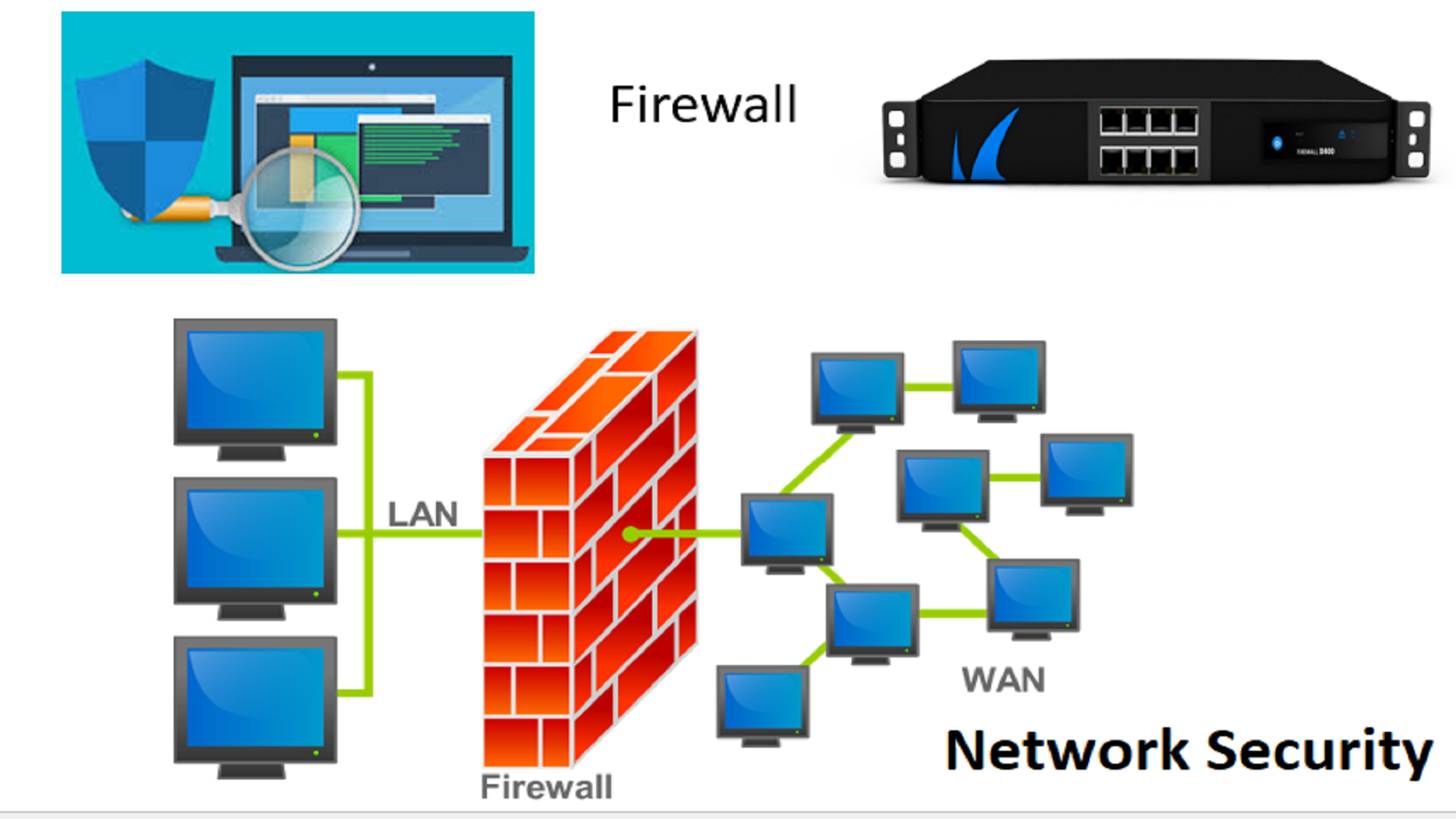
A remoteIoT firewall offers a powerful layer of protection by monitoring and controlling incoming and outgoing network traffic. It acts as a barrier between your IoT devices and potential cyber threats, ensuring that only legitimate data packets pass through. With the rise in sophisticated cyberattacks targeting IoT networks, understanding how remoteIoT firewalls work and their implementation is essential for maintaining data integrity and privacy.
This article delves deep into remoteIoT firewall examples, exploring their functionality, benefits, and best practices for implementation. Whether you're a business owner, IT professional, or simply someone interested in cybersecurity, this guide will provide valuable insights into enhancing your IoT security infrastructure. Let's explore how remoteIoT firewalls can protect your network and devices from potential threats.
Table of Contents
- Introduction to RemoteIoT Firewalls
- What is a RemoteIoT Firewall?
- Types of RemoteIoT Firewalls
- Benefits of Using RemoteIoT Firewalls
- Examples of RemoteIoT Firewalls
- How RemoteIoT Firewalls Work
- Best Practices for Implementation
- Common Challenges and Solutions
- Data Security and Privacy
- The Future of RemoteIoT Firewalls
Introduction to RemoteIoT Firewalls
As the Internet of Things (IoT) continues to expand, the demand for secure network environments has surged. RemoteIoT firewalls are designed to address the unique security challenges posed by IoT devices. These firewalls offer advanced filtering capabilities, ensuring that only authorized traffic passes through the network.
In this section, we will explore the basics of remoteIoT firewalls, their role in modern cybersecurity strategies, and why they are essential for safeguarding IoT networks. By understanding the fundamental principles of remoteIoT firewalls, you can make informed decisions about implementing them in your environment.
What is a RemoteIoT Firewall?
A remoteIoT firewall is a specialized security solution designed to protect IoT devices and networks from unauthorized access and cyber threats. Unlike traditional firewalls, remoteIoT firewalls focus specifically on securing IoT ecosystems, which often include a wide range of devices with varying levels of security.
- How Old Is Laurie From Shark Tank
- Aishwarya Rajesh Father
- Gigi Zanchetta
- They Gently Wave Both Their Hands Awkwardly
Key Features of RemoteIoT Firewalls
- Advanced packet filtering
- Real-time threat detection
- Centralized management
- Scalability for growing IoT networks
These features make remoteIoT firewalls an indispensable tool for organizations looking to enhance their IoT security infrastructure.
Types of RemoteIoT Firewalls
There are several types of remoteIoT firewalls, each catering to different security needs and environments. Understanding the differences between these types can help you choose the right solution for your specific requirements.
1. Hardware-Based Firewalls
Hardware-based remoteIoT firewalls are physical devices that are installed at the network perimeter. They offer robust protection and are ideal for large-scale deployments.
2. Software-Based Firewalls
Software-based remoteIoT firewalls are installed on servers or devices within the network. They provide flexibility and are suitable for smaller networks or those with limited budget constraints.
3. Cloud-Based Firewalls
Cloud-based remoteIoT firewalls offer scalability and ease of management. They are hosted on remote servers and can be accessed and managed from anywhere, making them a popular choice for modern businesses.
Benefits of Using RemoteIoT Firewalls
Implementing a remoteIoT firewall brings numerous benefits, including enhanced security, improved network performance, and centralized management. Here are some key advantages:
- Protection against unauthorized access
- Real-time threat detection and mitigation
- Centralized control and monitoring
- Scalability for growing IoT networks
- Reduced risk of data breaches
By leveraging these benefits, organizations can create a secure and efficient IoT ecosystem.
Examples of RemoteIoT Firewalls
Several remoteIoT firewall solutions are available in the market, each offering unique features and capabilities. Below are some notable examples:
1. Palo Alto Networks
Palo Alto Networks provides advanced remoteIoT firewalls with features like threat prevention, URL filtering, and application visibility.
2. Fortinet FortiGate
FortiGate offers robust security for IoT networks with features like intrusion prevention, SSL inspection, and centralized management.
3. Cisco ASA
Cisco ASA firewalls provide comprehensive security for IoT devices with features like firewalling, VPN, and intrusion prevention.
How RemoteIoT Firewalls Work
RemoteIoT firewalls operate by monitoring and filtering network traffic based on predefined rules and policies. They analyze incoming and outgoing data packets, ensuring that only legitimate traffic is allowed to pass through. This process involves several key steps:
- Packet inspection
- Rule-based filtering
- Threat detection and mitigation
- Logging and reporting
By following these steps, remoteIoT firewalls effectively protect IoT networks from potential cyber threats.
Best Practices for Implementation
Implementing a remoteIoT firewall requires careful planning and execution to ensure maximum effectiveness. Here are some best practices to consider:
- Conduct a thorough risk assessment
- Choose the right firewall solution for your needs
- Configure rules and policies based on your security requirements
- Regularly update and patch the firewall software
- Monitor and analyze firewall logs for suspicious activity
By adhering to these best practices, you can maximize the security benefits of your remoteIoT firewall.
Common Challenges and Solutions
While remoteIoT firewalls offer significant security advantages, they also come with certain challenges. Some common challenges include:
1. Complexity of Configuration
Solution: Use intuitive management interfaces and seek professional assistance if needed.
2. Scalability Issues
Solution: Opt for cloud-based solutions that offer scalable deployment options.
3. Performance Impact
Solution: Regularly optimize firewall rules and policies to minimize performance overhead.
Data Security and Privacy
RemoteIoT firewalls play a critical role in ensuring data security and privacy in IoT networks. By implementing strong encryption protocols and access controls, these firewalls help protect sensitive information from unauthorized access and cyber threats. Additionally, they provide detailed logging and reporting capabilities, enabling organizations to monitor and respond to potential security incidents effectively.
The Future of RemoteIoT Firewalls
As IoT technology continues to evolve, so will the capabilities of remoteIoT firewalls. Future advancements are likely to include:
- Enhanced AI-driven threat detection
- Improved scalability for large-scale IoT deployments
- Integration with other security solutions for comprehensive protection
By staying informed about these advancements, organizations can ensure their IoT security measures remain up-to-date and effective.
Conclusion
RemoteIoT firewalls are essential tools for securing IoT networks and devices against cyber threats. By understanding their functionality, benefits, and implementation best practices, you can create a robust security infrastructure that protects your data and privacy. As the IoT landscape continues to grow, investing in advanced security solutions like remoteIoT firewalls is more important than ever.
We invite you to share your thoughts and experiences with remoteIoT firewalls in the comments section below. Additionally, feel free to explore other articles on our site for more insights into cybersecurity and IoT technologies.
What Is a Firewall? (Definition, Types, Examples) Built In
How To Use RemoteIoT Behind Firewall Examples For Secure Device Management

RemoteIoT Firewall Examples Comprehensive Guide To Secure Your IoT Devices