Unlocking The Potential Of SSH Remote IoT Device Access On Android
In today's interconnected world, the ability to remotely access IoT devices from your Android device using SSH has become an essential skill for tech enthusiasts, developers, and professionals alike. Secure Shell (SSH) serves as a robust tool that enables secure communication between devices over potentially unsecured networks. Whether you're managing a home automation system or monitoring industrial equipment, understanding how to leverage SSH remote IoT device access can significantly enhance your capabilities.
As the Internet of Things continues to expand, the demand for secure and efficient methods to interact with these devices remotely has grown exponentially. SSH provides a secure channel for communication, ensuring that sensitive data remains protected while enabling seamless control over IoT devices. This article aims to provide an in-depth exploration of SSH remote IoT device access on Android, covering everything from setup to advanced techniques.
By the end of this comprehensive guide, you will have a thorough understanding of how to configure and utilize SSH for remote IoT device management on your Android device. We will delve into the technical aspects, explore best practices, and discuss security considerations to ensure a reliable and secure connection. Let's begin by exploring the fundamentals of SSH and its role in IoT device management.
Table of Contents
- Introduction to SSH and Its Importance in IoT
- Benefits of Using SSH for Remote IoT Device Access
- Setting Up SSH on Your Android Device
- Choosing the Right SSH Client for Android
- Securing Your SSH Connections
- Advanced SSH Techniques for IoT Devices
- Troubleshooting Common SSH Issues
- Best Practices for SSH Remote IoT Device Access
- Case Studies: Real-World Applications of SSH in IoT
- The Future of SSH in IoT Device Management
Introduction to SSH and Its Importance in IoT
SSH, or Secure Shell, is a cryptographic network protocol designed to provide secure communication over unsecured networks. It plays a pivotal role in IoT device management by enabling users to remotely access and control devices with encrypted data transfer. The importance of SSH in IoT cannot be overstated, as it ensures data integrity, confidentiality, and authentication.
In the context of IoT, SSH remote IoT device access allows users to manage and monitor devices from anywhere in the world. This capability is particularly valuable for industries such as manufacturing, healthcare, and smart homes, where real-time monitoring and control are critical. By leveraging SSH, organizations can streamline operations, reduce downtime, and enhance security.
How SSH Works in IoT
SSH operates by establishing a secure connection between a client and a server. When applied to IoT devices, the Android device acts as the client, while the IoT device serves as the server. The communication is encrypted using strong algorithms, ensuring that even if intercepted, the data remains unreadable to unauthorized parties.
Benefits of Using SSH for Remote IoT Device Access
Utilizing SSH for remote IoT device access on Android offers numerous advantages that make it an indispensable tool for modern device management. Below are some of the key benefits:
- Enhanced Security: SSH employs encryption protocols that protect data from unauthorized access and interception.
- Reliability: The protocol ensures stable and consistent connections, even over unreliable networks.
- Flexibility: SSH supports a wide range of commands and operations, making it suitable for various IoT applications.
- Scalability: It can handle multiple devices simultaneously, making it ideal for large-scale IoT deployments.
Setting Up SSH on Your Android Device
Configuring SSH on your Android device involves several steps, including downloading the necessary applications and setting up the server on your IoT device. Follow this step-by-step guide to ensure a successful setup:
Step 1: Install an SSH Client
Begin by downloading a reliable SSH client from the Google Play Store. Popular options include JuiceSSH and Termux. These applications provide user-friendly interfaces and robust features for managing SSH connections.
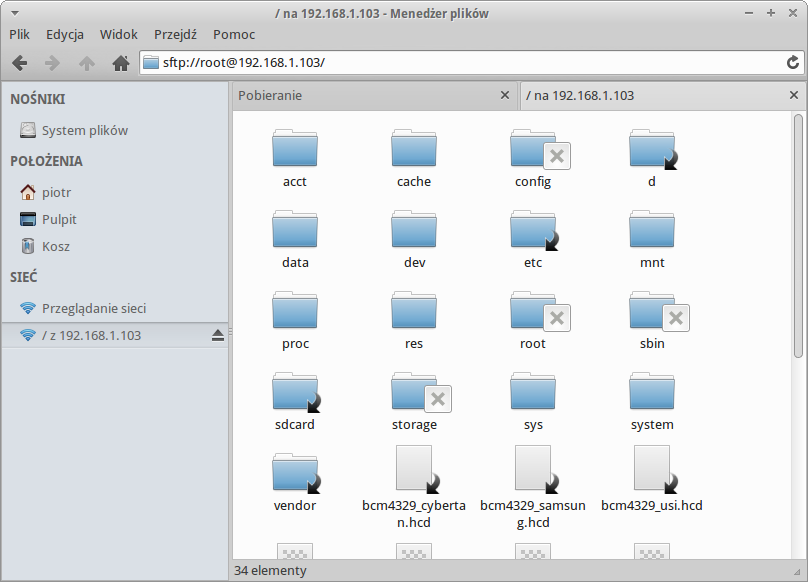
Step 2: Configure the IoT Device
Ensure that your IoT device is configured to accept SSH connections. This typically involves enabling SSH in the device's settings and configuring the necessary authentication methods.
Step 3: Establish the Connection
Once both the Android device and the IoT device are ready, establish the connection by entering the device's IP address, port number, and authentication credentials in the SSH client.
Choosing the Right SSH Client for Android
Selecting the appropriate SSH client is crucial for a seamless user experience. Consider the following factors when making your decision:
- User Interface: Choose a client with an intuitive and easy-to-navigate interface.
- Feature Set: Ensure the client supports all the features you require, such as key-based authentication and session management.
- Performance: Opt for a client that offers fast and reliable connections, even on slow networks.
- Security: Prioritize clients that implement the latest security protocols and updates.
Securing Your SSH Connections
Security is paramount when dealing with remote IoT device access. Implement the following best practices to safeguard your SSH connections:
Use Strong Authentication Methods
Instead of relying solely on password-based authentication, consider using SSH keys. This method provides a higher level of security by eliminating the risk of brute-force attacks.
Regularly Update Software
Keep both your Android device and IoT devices up to date with the latest software patches and security updates. This practice helps mitigate potential vulnerabilities.
Limit Access
Restrict SSH access to authorized users only. Use firewalls and access control lists to ensure that only trusted devices can connect to your IoT devices.
Advanced SSH Techniques for IoT Devices
For users seeking to maximize the capabilities of SSH, several advanced techniques can enhance functionality and security:
Tunneling
SSH tunneling allows you to securely transfer data between devices by encapsulating it within an encrypted SSH connection. This technique is particularly useful for accessing sensitive information or bypassing network restrictions.
Port Forwarding
Port forwarding enables you to redirect network traffic from one port to another, facilitating access to services that may not be directly exposed to the internet.
Troubleshooting Common SSH Issues
Despite its robustness, SSH connections can sometimes encounter issues. Below are some common problems and their solutions:
- Connection Refused: Verify that the SSH service is running on the IoT device and that the correct IP address and port number are used.
- Authentication Failure: Double-check your credentials and ensure that the authentication method is correctly configured.
- Network Issues: Ensure that both devices are connected to the same network and that no firewalls are blocking the connection.
Best Practices for SSH Remote IoT Device Access
Adhering to best practices ensures a secure and efficient SSH experience. Consider the following recommendations:
- Always use encryption for data transfer.
- Regularly audit your SSH configurations and access logs.
- Implement multi-factor authentication for added security.
- Backup your SSH keys and configurations in a secure location.
Case Studies: Real-World Applications of SSH in IoT
To illustrate the practical applications of SSH in IoT, let's explore a few real-world case studies:
Smart Home Automation
Homeowners use SSH to remotely manage their smart home systems, adjusting settings and monitoring activity from their Android devices.
Industrial Equipment Monitoring
Manufacturing facilities employ SSH to monitor and control industrial equipment, ensuring optimal performance and minimizing downtime.
The Future of SSH in IoT Device Management
As technology continues to evolve, the role of SSH in IoT device management is likely to expand. Emerging trends such as quantum computing and artificial intelligence may introduce new challenges and opportunities for SSH. Staying informed about these developments will be essential for maintaining secure and effective IoT systems.
Conclusion
In conclusion, SSH remote IoT device access on Android offers a powerful solution for managing and monitoring IoT devices securely and efficiently. By understanding the fundamentals, implementing best practices, and leveraging advanced techniques, you can unlock the full potential of SSH in your IoT projects. We encourage you to share your experiences, ask questions, and explore further resources to enhance your knowledge and skills in this exciting field.
Feel free to leave a comment or share this article with others who may find it beneficial. For more insights into IoT and related technologies, explore our other articles and stay updated on the latest trends and innovations.
SSH server on Android remote access to your green robot device

Mastering SSH RemoteIoT Device Android APK A Comprehensive Guide

Mastering SSH RemoteIoT Device Android APK A Comprehensive Guide